After countless attacks across a multitude of organizations, the cyber security industry has a fairly good grasp of how adversaries…
SquareX first discovered and disclosed Last Mile Reassembly attacks at DEF CON 32 last year, warning the security community of…
Palo Alto, California, September 18th, 2025, CyberNewsWire SquareX first discovered and disclosed Last Mile Reassembly attacks at DEF CON 32…
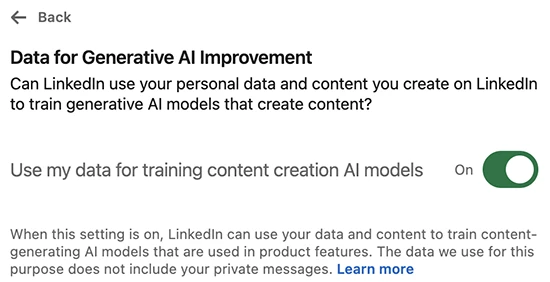
LinkedIn is making major changes to its User Agreement and Privacy Policy, effective November 3, 2025. Among the most notable…
AI’s growing role in enterprise environments has heightened the urgency for Chief Information Security Officers (CISOs) to drive effective AI…
Two men, named as Owen Flowers and Thalha Jubair, have today appeared before Westminster Magistrate’s Court in connection with a…
APT28, the long-running actor tracked as Fancy Bear, Sofacy and Sednit, used a compact but technically sophisticated campaign that researchers…
Emerging in mid-2025, the shinysp1d3r ransomware-as-a-service (RaaS) platform represents the next evolution of cloud-focused extortion tools. Unlike traditional ransomware that…
EclecticIQ analysts assess with high confidence that ShinyHunters is expanding its operations by combining AI-enabled voice phishing, supply chain compromises,…
Cybersecurity Ventures predicts that the global cost of cybercrime it will surpass $10.5 trillion annually in 2025. When it comes to…
Google has released a security update for the Chrome stable channel to fix a zero‑day vulnerability (CVE-2025-10585) reported by its…
Sep 18, 2025Ravie LakshmananMalware / Supply Chain Attack Cybersecurity researchers have discovered two new malicious packages in the Python Package…