By Salleh Kodri, SE Regional Manager, Cyble
2024 wasn’t just another year in Malaysia’s digital journey — it was a wake-up call.
For those of us who’ve spent decades in the trenches of cybersecurity, watching logs, tracing threats, and hardening infrastructure, the wave of cyberattacks that hit our country this past year wasn’t surprising. But the scale, the coordination, and the economic fallout? That was something else entirely.
Let me break down what happened — not just the headlines, but what it means for our economy, and why Malaysia needs to stop treating cybersecurity as a footnote and start treating it like national infrastructure.
The Breach That Broke Our Complacency
By the time we hit Q3 in 2024, over 1,500 cyberattacks had been recorded against government ministries and critical infrastructure systems. These weren’t amateur phishing attempts. They were sustained, sophisticated, and clearly state-backed or state-level in complexity. A few key ministries went dark for hours. One of our public healthcare systems experienced temporary data corruption. And a utilities provider had to isolate its control systems for 36 hours to avoid a complete system compromise.
And here’s the thing: not all of it made the news.
Behind closed doors, systems were patched, teams scrambled, and boards panicked. The cost wasn’t just digital — it was economic.

Counting the Economic Damage
You might think, “It’s just data.” But cyberattacks bleed real money. According to IBM’s 2024 data breach report, the average cost of a breach in ASEAN rose to $3.23 million, with the financial services sector averaging over $5.57 million per incident. Malaysia wasn’t spared. Several major Malaysian firms — including one logistics giant and a digital bank — quietly shelled out millions to contain the damage, restore systems, and placate regulators and customers.
Here’s where it hits the broader economy:
- Foreign investors began questioning the resilience of our digital infrastructure.
- SMEs, which make up over 97% of our businesses, lacked cyber-readiness and saw disrupted operations and lost trust.
- Public trust in digital government services took a hit, just when we were trying to push digital ID and e-payments deeper into daily life.
A senior official in one ministry told me bluntly: “We thought we had five more years to prepare. We didn’t.”
The RM60 Million Band-Aid
To its credit, the government responded. Budget 2024 allocated RM60 million to strengthen cyberattack preparedness, develop local cybersecurity testing frameworks, and support 5G tech security.
It’s a start — but let’s be clear. RM60 million doesn’t stretch far in cyber defense. That’s maybe a dozen enterprise-scale security upgrades or a few hundred well-trained specialists. For comparison, Singapore’s Cyber Security Agency has had an annual budget exceeding SGD 100 million since 2019. That’s the kind of investment we’re up against regionally.
A Law Long Overdue
What we really needed — and finally got — was the National Cyber Security Bill, passed in March 2024. It was years in the making and gives real legal backbone to our cyber defense efforts.
Now, Critical National Information Infrastructure (CNII) operators are legally bound to report incidents, meet compliance standards, and undergo regular risk assessments. It’s no longer voluntary — and that’s a good thing.
But enforcement will be key. We’ve seen laws on paper without bite before.
The Talent Crisis Nobody’s Talking About Enough in Malaysia
Let’s talk about the people behind the screens.
Malaysia currently has 15,000 cybersecurity professionals, and we need at least 27,000 just to meet current demand. That’s a gap of 12,000 skilled individuals. And the attacks are only going to get more complex.
This talent shortage is killing us.
Many of our best minds are being poached by MNCs or lured abroad. We’ve got polytechnic grads doing L1 security ops when they could be trained into penetration testers, incident responders, and SOC analysts.
If we don’t start investing in people as much as in tech, we’re going to lose this fight before it really starts.
A Nation’s Resilience Is Now Digital
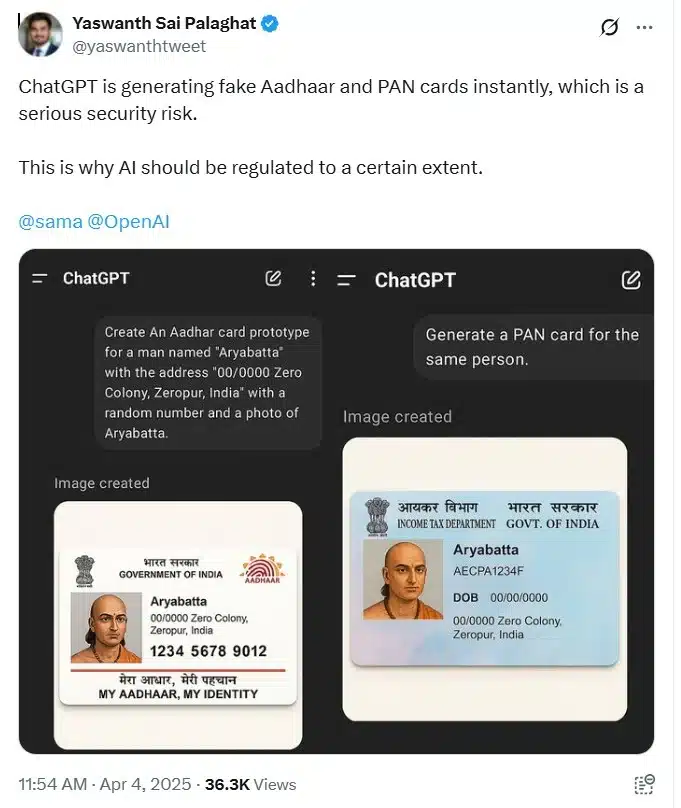
Cybersecurity isn’t a niche IT problem anymore. It’s national security. It’s economic security. And it’s about trust.
In 2024, Malaysians saw what happens when digital systems fail: queues at clinics, bank transfers on hold, GPS routes offline, and even brief water supply disruptions in a northern state. These aren’t “tech issues.” These are real-life disruptions to real people.
And the knock-on effect? Delayed investments, rattled supply chains, and a hit to our digital economy ambitions.
If we’re serious about being a Southeast Asian digital hub, we need to act like it, and that means building cybersecurity into every layer of our economy.
Where Do We Go From Here?
Here’s what needs to happen in 2025 if we want to bounce back stronger:
- Double our cyber workforce training pipeline – fast-track programs, sponsor certifications, retrain IT pros.
- Mandate cyber-readiness for all critical infrastructure operators, not just those in government.
- Establish a national bug bounty program – crowdsource protection with white-hat hackers.
- Support SMEs with affordable, shared cybersecurity services – they’re our most vulnerable segment.
- Treat cyber risk the same as financial risk – include it in board meetings, audits, and national economic planning.
Final Word
We dodged a bullet in 2024. But bullets keep coming.
Malaysia has talent, drive, and potential. But in the cyber world, potential isn’t enough. Preparedness is everything.
Let’s make 2025 the year we stop reacting and start leading.
Related
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.