Last week, a security researcher sent me 122GB of data scraped out of thousands of Telegram channels.
It contained 1.7k files with 2B lines and 361M unique email addresses, of which 151M had never been seen in Have I Been Pwned (HIBP) before.
Alongside those addresses were passwords and, in many cases, the website the data pertains to.
I loaded it into HIBP today because there are a large number of previously unseen email addresses, and based on all the checks I’ve done, it’s legitimate data.
That’s the high-level overview. Here are the details.
Telegram: A Breeding Ground for Data Breaches
Telegram is a popular messaging platform that makes it easy to set up a “channel” and share information with those who wish to visit it.
As Telegram describes the service, it’s simple, private, and secure.
As such, it has become very popular with those wishing to share content anonymously, including content related to data breaches.
Many of the breaches I’ve previously loaded into HIBP have been distributed via Telegram as it’s simple to publish this class of data to the platform.
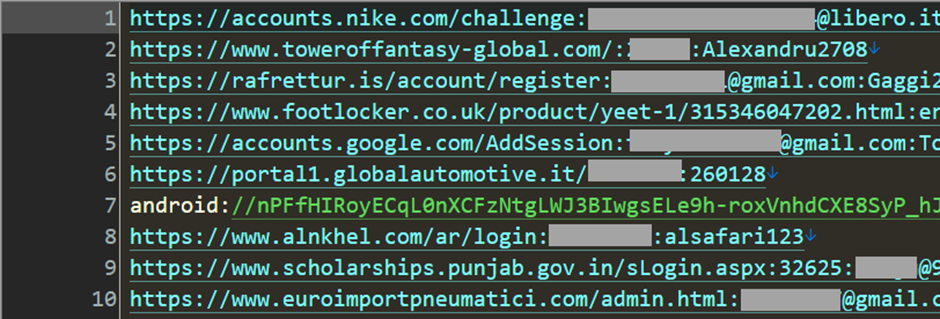
According to Troyhunt’s blog, the data posted to Telegram often appears as “combolists,” which are combinations of email addresses or usernames and passwords.
These combinations are used to authenticate to various services, and attackers often use these lists to mount “credential stuffing” attacks, where they attempt to access accounts en masse.
The list above is simply breaking the combos into their respective email service providers.
The Scale of the Breach
The data sent to me last week was sourced from 518 different channels and amounted to 1,748 separate files similar to the one above.
With ANYRUN You can Analyze any URL, Files & Email for Malicious Activity : Start your Analysis
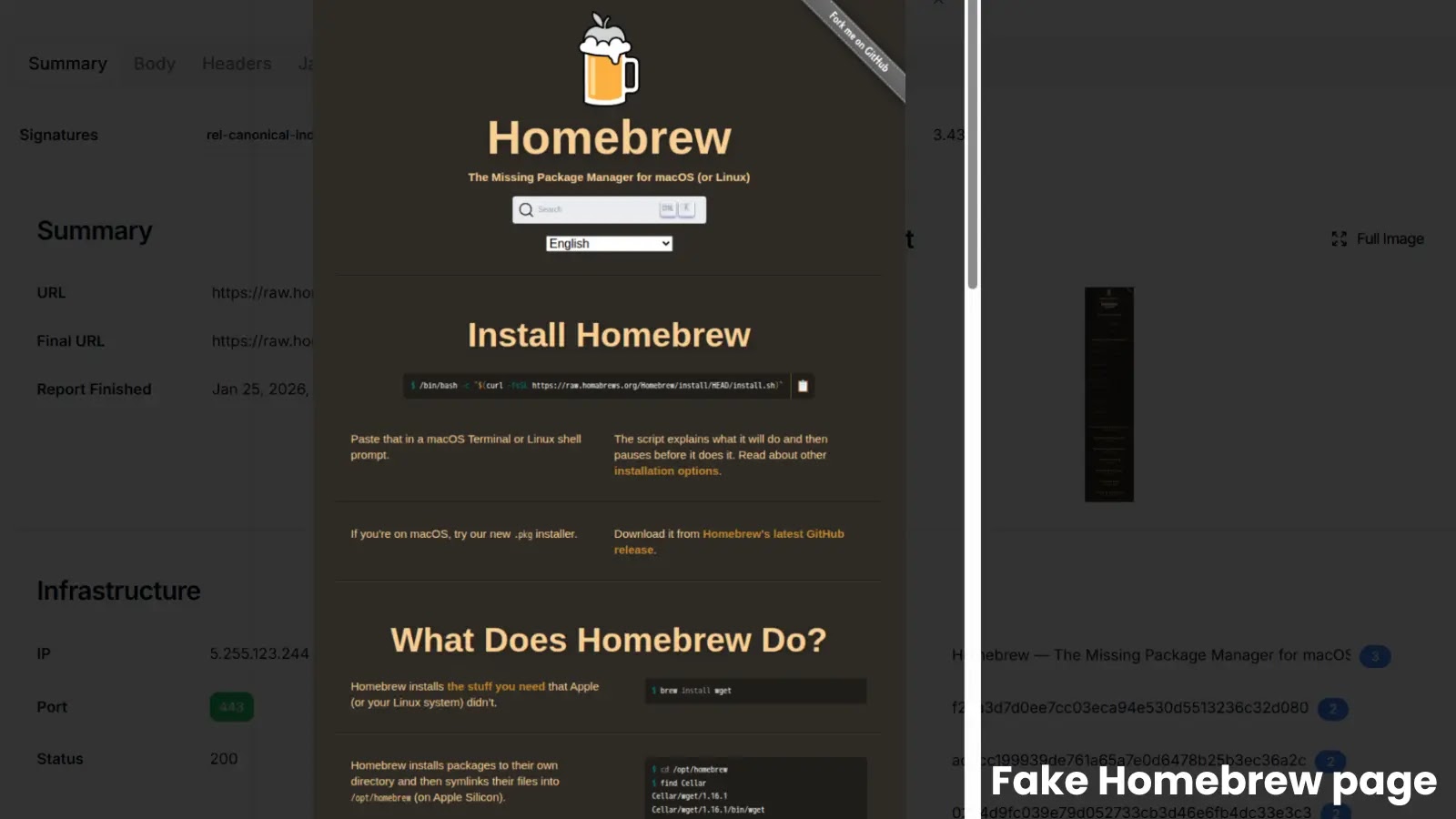
Some of the files have no data (0kb), while others are many gigabytes with many tens of millions of rows. For example, the largest file starts like this:
This looks very much like the result of info stealer malware that has obtained credentials as they were entered into websites on compromised machines.
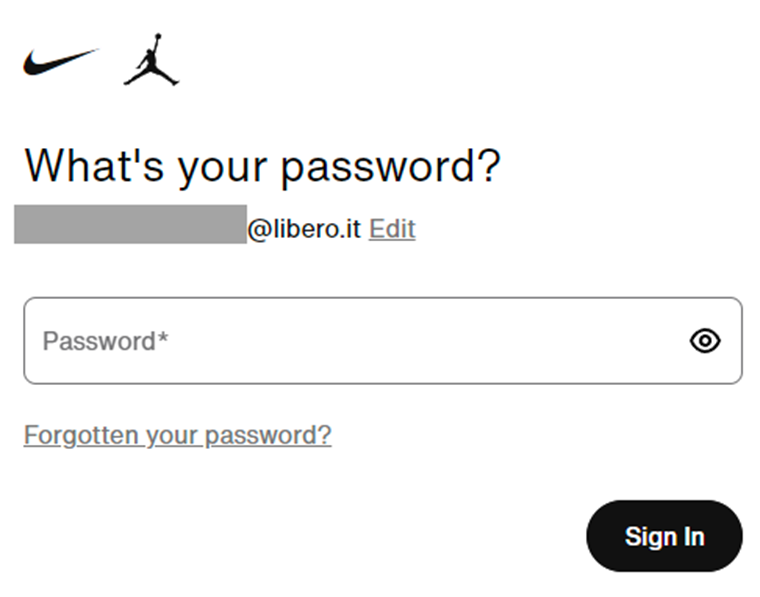
For example, the first record appears to have been snared when someone attempted to log in to Nike.
Verifying the Data
To get a sense of the accuracy of this data, I tested several email addresses on various websites.
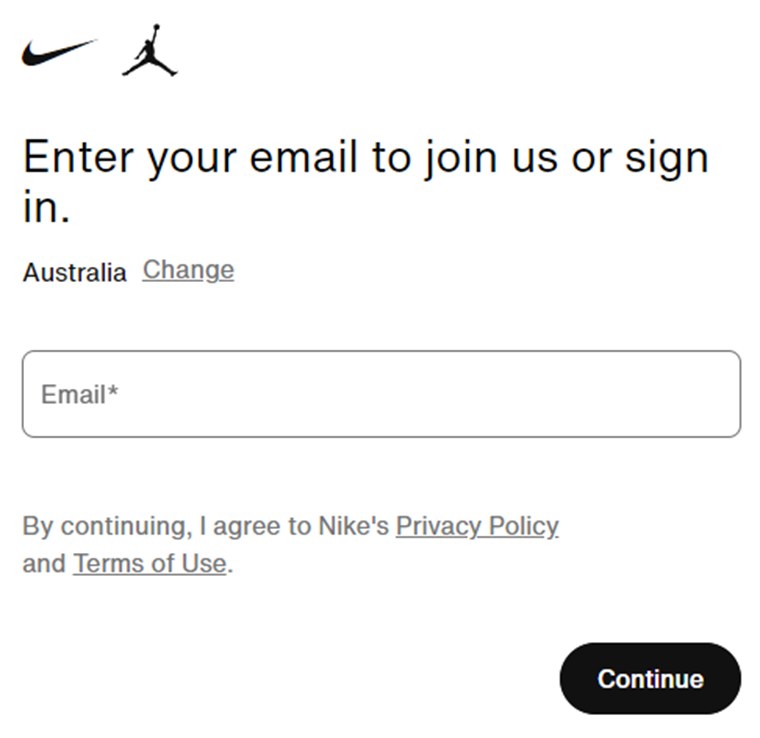
For instance, entering an email address from the stealer log on the Nike homepage confirmed that the address had an account.
Similarly, other services like Footlocker and an Italian tire retailer confirmed the existence of the tested accounts.
Subscriber Feedback
I reached out to existing HIBP subscribers to verify the legitimacy of the data.
One subscriber, already in 13 different breaches, confirmed the accuracy of the details but noted they were leaked in previous data breaches.
Another subscriber, in 7 prior breaches, found the credentials familiar, likely reused from previous breaches.
One fascinating case involved a subscriber’s daughter who had an Epic Games account.
The credentials matched her old account, confirming the legitimacy of the data.
To understand the impact of the unseen addresses, I contacted HIBP subscribers who had never appeared in a breach before.
This ruled out repurposed prior incidents and provided a clearer picture of the data’s significance.
The responses confirmed the legitimacy and uniqueness of the data, highlighting the breach’s extensive reach.
The leak of 361 million unique email credentials on Telegram channels is a significant data breach, with 151 million previously unseen addresses now loaded into HIBP.
This incident underscores the importance of robust cybersecurity measures and the need for users to remain vigilant about their online credentials.
Looking for Full Data Breach Protection? Try Cynet's All-in-One Cybersecurity Platform for MSPs: Try Free Demo