A newly uncovered malware campaign dubbed KadNap has silently conscripted more than 14,000 internet‑exposed routers and edge devices into a stealth proxy botnet, with Asus routers the primary victims.
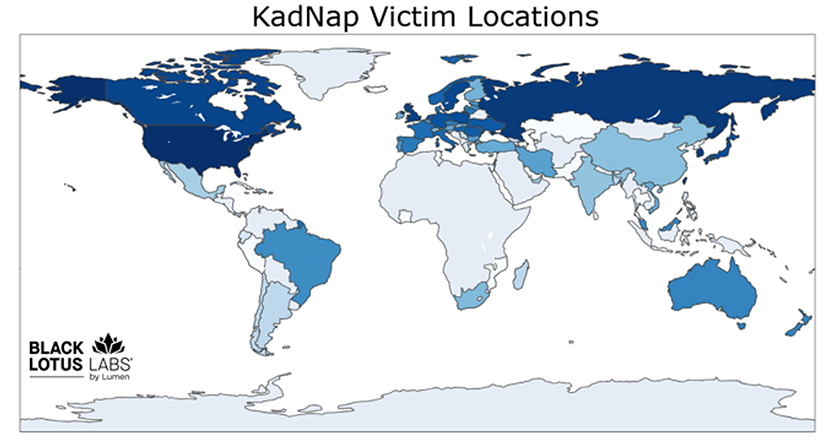
More than 60% of known victims are located in the United States, with additional infections observed in Taiwan, Hong Kong, Russia, and other countriesHow KadNap Infects Routers
The campaign was first flagged when more than 10,000 Asus devices were seen talking to a suspicious cluster of servers in early August 2025.
Further analysis revealed a malicious download chain that starts with a shell script hosted at 212.104.141[.]140 named aic.sh, which is used to gain persistence and stage the KadNap payload.
The script creates an hourly cron job that repeatedly retrieves a malicious shell script, renames it to “.asusrouter,” and executes it from the /jffs/.asusrouter path, ensuring the compromise survives reboots and configuration changes.
Discovered by Lumen’s Black Lotus Labs, the operation has been active since at least August 2025. It is now being actively abused to route malicious traffic through compromised home and small office networks worldwide.
Once persistence is in place, the script pulls down an ELF binary for the router, renames it to “kad,” and runs it this is the KadNap malware itself.
Samples have been identified for both ARM and MIPS architectures, enabling the threat actors to target a wide range of consumer and edge networking hardware beyond just Asus models.
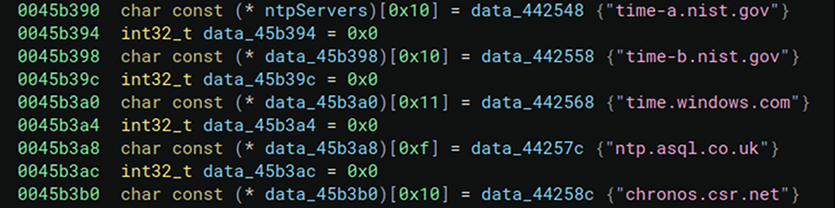
During initialization, KadNap daemonizes itself by forking and redirecting STDIN, STDOUT and STDERR to /dev/null, then determines the device’s external IP address and synchronizes time with public NTP servers, using the time and uptime values later to construct cryptographic hashes that drive peer‑to‑peer communications.
Abusing Kademlia to Hide C2
KadNap’s most notable innovation is its custom implementation of the Kademlia Distributed Hash Table (DHT) protocol, a peer‑to‑peer system also used in technologies such as BitTorrent and eMule for decentralized lookups.
In this botnet, Kademlia is repurposed to conceal the true IP addresses of command‑and‑control (C2) servers: infected devices use DHT lookups to discover C2 endpoints, while defenders see only noisy, seemingly benign P2P traffic that resists traditional blocklisting.
This design makes it much harder for security teams to enumerate and block KadNap’s infrastructure, giving the operators resilience against sinkholing and takedowns.
Internally, KadNap spins up multiple threads to implement this logic. A “find peers” thread uses known BitTorrent bootstrap nodes, NTP‑derived XOR keys and SHA‑1 hashes of hardcoded strings to craft a custom infohash that leads it to other KadNap‑infected peers.
A separate “contact peers” thread reads peer IP:port entries from a pipe, connects to them, decrypts responses with hardcoded keys, and establishes AES‑protected channels for further encrypted command traffic and secondary payload downloads such as fwr.sh (which modifies firewall rules) and .sose (which stores C2 configuration).
Although KadNap is built on a peer‑to‑peer model, researchers found a critical weakness in the operators’ custom Kademlia implementation.
In a properly functioning Kademlia network, the final hop before reaching a resource changes over time, reflecting true decentralization; however, all KadNap samples examined since August 2025 consistently contacted the same two final nodes 45.135.180[.]38 and 45.135.180[.]177 immediately before reaching the C2 servers.
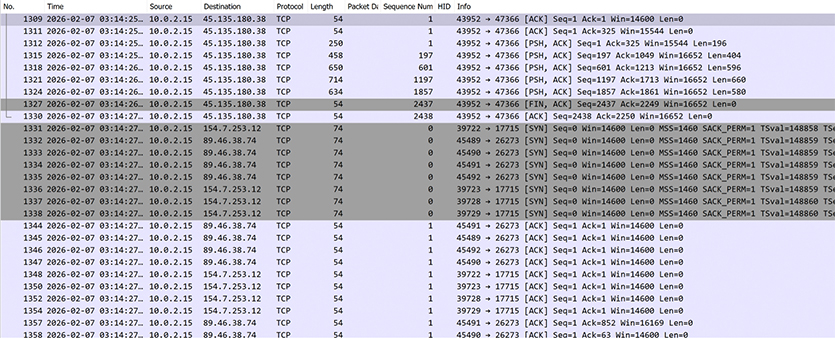
This fixed “chokepoint” structure suggests the attackers maintain long‑lived, centrally controlled peers to retain strong operational control over the botnet while still benefiting from the cover of P2P traffic.
Monetization via Doppelganger Proxy Service
Once enrolled, KadNap bots are monetized through a residential proxy service called “Doppelganger,” which appears to be a direct rebrand of the Faceless platform previously powered by TheMoon malware.
The victims are distributed across several countries, with 60% located in the United States and 5% each in Taiwan, Hong Kong and Russia.
Doppelganger markets access to these hijacked devices as highly anonymous residential proxies, enabling cybercriminals to conduct brute‑force attacks, account takeovers and targeted exploitation while hiding behind the IP addresses of ordinary home users.
Because the botnet’s infrastructure is segmented by device type and model, not all infected routers talk to every C2 server, complicating attribution and making malicious activity harder to link back to specific campaigns.
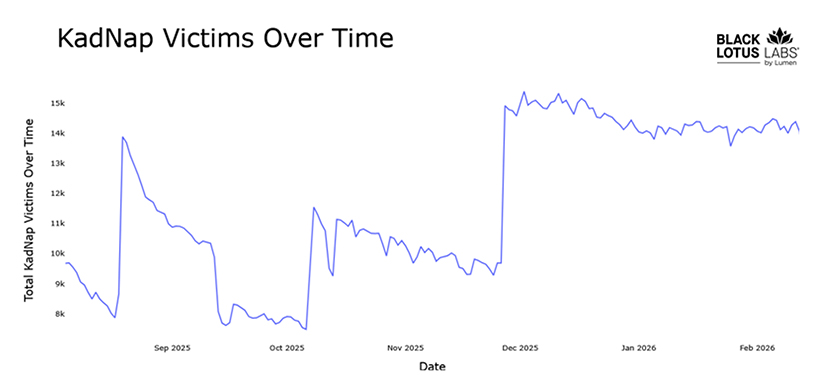
According to Lumen, the KadNap botnet has stabilized at an average of around 14,000 distinct infected devices per day, with three to four active C2s in use at any time.
For network defenders, the campaign underscores the growing risk posed by vulnerable SOHO and IoT devices updates and the importance of actions such as disabling remote administration, applying the latest firmware updates, enforcing strong router credentials.
Lumen reports that it has proactively blocked traffic to and from KadNap control infrastructure across its backbone and will be sharing indicators of compromise via public feeds to help the wider security community disrupt this threat, also acknowledging Spur’s role in tying the infrastructure to Doppelganger.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.



