Cisco has issued a High-severity security advisory alerting customers to a critical vulnerability in the Intermediate System-to-Intermediate System (IS-IS) feature of NX-OS Software for Cisco Nexus 3000 and 9000 Series switches.
Tracked as CVE-2025-20241 with a CVSS base score of 7.4, the flaw could allow an unauthenticated, Layer 2-adjacent attacker to send a malformed IS-IS packet that restarts the IS-IS process, potentially reloading the device and causing a denial-of-service (DoS) condition.
Key Takeaways
1. Cisco Nexus 3000/9000 IS-IS flaw allows adjacent DoS.
2 No workaround; enable IS-IS area authentication.
3. Apply Cisco’s free NX-OS update.
Cisco Nexus 3000 and 9000 Vulnerabilities
The vulnerability stems from insufficient input validation when parsing ingress IS-IS packets. An attacker must be on the same broadcast domain as the target switch and can exploit the flaw by transmitting a specially crafted IS-IS L1 or L2 packet.
Upon receipt, the NX-OS IS-IS daemon may crash and subsequently reload the entire switch, disrupting network routing and traffic forwarding. This condition affects:
- Cisco Nexus 3000 Series Switches
- Cisco Nexus 9000 Series Switches in standalone NX-OS mode
Only devices with IS-IS enabled on at least one interface are vulnerable. Products such as Nexus 9000 in ACI mode, Firepower 1000/2100/4100/9300, MDS 9000, and UCS Fabric Interconnects are confirmed not vulnerable.
The advisory notes that if IS-IS authentication is configured, the attacker must supply valid keys to exploit the issue.
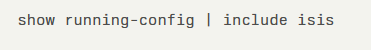
To verify IS-IS status, administrators can run the CLI command:
Presence of feature isis, router isis name, and at least one ip router isis name entry confirms exposure. To view live IS-IS peers, use:

| Risk Factors | Details |
| Affected Products | Cisco Nexus 3000 Series SwitchesCisco Nexus 9000 Series Switches (standalone NX-OS) |
| Impact | IS-IS process restart causing device reload (DoS) |
| Exploit Prerequisites | Layer 2 adjacency; IS-IS enabled on interface |
| CVSS 3.1 Score | 7.4 (High) |
No temporary workarounds exist; however, enabling area authentication for IS-IS can mitigate risk by requiring attackers to authenticate before sending malicious packets.
Cisco strongly recommends that customers thoroughly evaluate this mitigation to ensure compatibility with their network requirements.
Cisco has released free software updates to address the vulnerability. Customers with valid service contracts should download and install the fixed releases from the Cisco Support and Downloads portal.
For those without service contracts, contacting the Cisco TAC with the advisory URL and product serial number will enable entitlement to the necessary patches.
Tired of Filling Forms for security & Compliance questionnaires? Automate them in minutes with 1up! Start Your Free Trial Now!
