In a sophisticated campaign uncovered during a recent Advanced Continual Threat Hunt (ACTH) by Trustwave’s SpiderLabs team, threat actors weaponized a legitimate remote management tool, ScreenConnect, to deploy the Xworm Remote Access Trojan (RAT) through a deceptive, multi-stage infection chain.
By abusing fake AI-themed content and manipulating digital signatures, the attackers bypassed Endpoint Detection and Response (EDR) alerts and relied on human-led threat hunting to reveal the hidden payloads.
The operation began with social engineering lures masquerading as AI video files. Victims were enticed to visit a fake AI website, “gptgrok[.]ai,” which redirected to “anhemvn6[.]com.”
There, users downloaded a file named “Creation_Made_By_GrokAI.mp4 Grok.com” that was in fact the “ScreenConnect.ClientSetup.msi” installer. Variations including “Creation_Made_By_GoogleAI.mp4 Google.com” and “Creation_Made_By_SoraAI.mp4 OpenAI.com” suggest a broad campaign leveraging AI buzzwords for credibility.
Code-Signing Certificate Abuse
Interestingly, collected samples showed that the threat actors manipulated Authenticode Microsoft code-signing certificates to embed malicious configurations within the digital signature of the legitimate ScreenConnect binary.
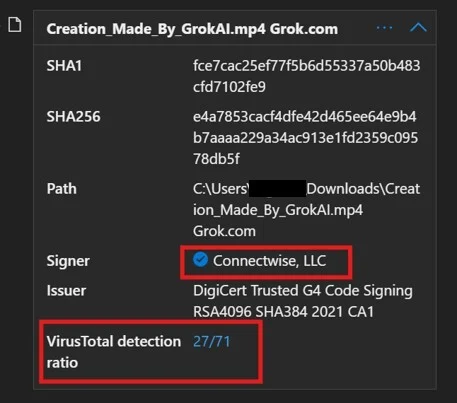
Once executed, the installer dropped and launched the ScreenConnect client in the user’s Temp directory. Preconfigured to run hidden, it connected silently to an attacker-controlled ScreenConnect server via a relay, using parameters embedded within the authenticode signature to evade tampering and maintain a valid digital signature.
Visual indicators such as icons and notifications were disabled, ensuring the session remained invisible to the end user.
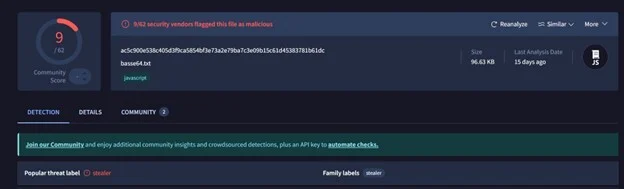
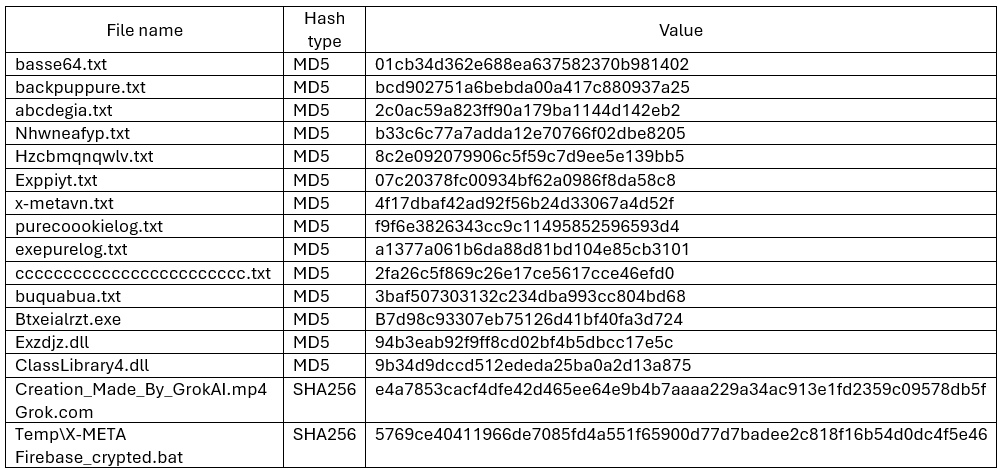
During the remote access session, the attackers deployed a batch script, “X-META Firebase_crypted.bat,” triggering mshta.exe to launch another hidden batch file. This script downloaded and unpacked “5btc.zip” from “anhemvn4[.]com,” revealing a Python interpreter renamed to pw.exe and an encoded “basse64.txt” payload.
Instead of saving malicious code to disk, the threat actors used msedge.exe and chrome.exe process hollowing—injecting Base64–encoded Python commands fetched directly from a public GitHub repository. This fileless execution technique hindered static detection and allowed Xworm RAT components to be delivered stealthily.
Persistence was established by creating a Run key in HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun named “Windows Security,” pointing to a “backup.bat” script in “C:xmetavip.”
On each login, this script re-launched pw.exe with new Base64 commands, fetching additional payloads such as “buquabua.txt” to maintain long-term access.
The campaign also included credential access and discovery stages. WMI queries gathered operating system and antivirus details, while the RAT attempted to harvest browser-stored login data from Chrome, Edge, and Firefox profiles.
SpiderLabs analysts noted that the GitHub repository hosting the obfuscated Python scripts contained eleven files—split between persistence implanters and complex RAT loaders created just a week before the attack.
One final payload script, “Exppiyt.txt,” embedded a command-and-control server IP (5[.]181[.]165[.]102:7705) that was not flagged as malicious on VirusTotal at the time of analysis.
This incident highlights a growing trend: attackers are co-opting trusted tools and AI branding to bypass automated defenses. Modern EDR and signature-based solutions struggled to detect this threat, underscoring the vital role of proactive, human-led threat hunting.
The SpiderLabs team’s investigation demonstrated that only through meticulous manual timeline analysis and behavioral hunting can these stealthy attacks be revealed.
As adversaries refine their tradecraft, leveraging code-signing manipulation, fileless execution, and legitimate management platforms, organizations must invest in skilled threat hunters who can think like attackers.
The SpiderLabs findings reinforce the strategic advantage of combining automated detection with expert analysis to uncover hidden threats before they can inflict damage.
Appendix – Indicators of compromise:
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.
