A sophisticated phishing campaign has been identified, where threat actors impersonate IT helpdesk personnel through Teams’ external communication features, exploiting the platform’s default configuration to bypass traditional email security measures and gain unauthorized screen-sharing and remote-control capabilities.
The attacks leverage Teams’ external collaboration features, which are enabled by default in Microsoft 365 tenants, allowing attackers to initiate contact with organizational users without prior authentication.
Key Takeaways
1. Default Teams settings enable direct IT helpdesk impersonation attacks, bypassing email security.
2. Voice calls avoid security warnings, leading to screen sharing and remote access.
3. Monitor ChatCreated/MessageSent logs for external .onmicrosoft.com domains.
This fundamental design choice has created an unprecedented attack surface that combines social engineering with legitimate platform functionality to devastating effect.
Voice Call Phishing and Remote Control
According to Axon Team reports, Cybercriminals have developed multiple sophisticated attack vectors within the Microsoft Teams ecosystem, each exploiting different aspects of the platform’s communication capabilities.
The primary attack method involves one-on-one chat phishing, where attackers use compromised Teams accounts or create malicious Entra ID tenants with .onmicrosoft.com domains – Microsoft’s default fallback domains for business accounts without custom domain configurations.
The technical implementation begins with threat actors conducting reconnaissance through Teams’ user search functionality, which allows external users to verify target email addresses and confirm message delivery capabilities.
When successful, attackers can initiate direct communication, though Microsoft has implemented security warnings, including “external communication warning” pop-ups and “potential phishing warning messages” that appear based on algorithmic threat detection.
However, attackers have discovered methods to circumvent these security measures through voice call phishing (vishing).
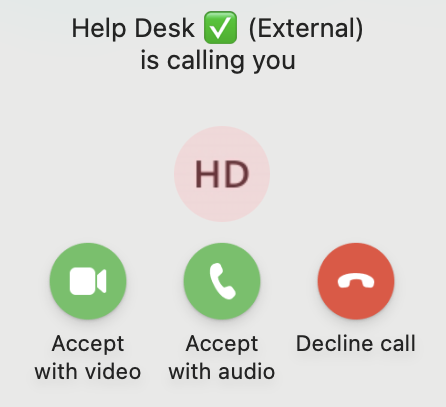
Unlike text-based communications, voice calls from external Teams users generate no warning pop-ups, creating a seamless attack vector.
Once trust is established through voice communication, attackers request screen sharing permissions, enabling them to observe victim activities and potentially guide them through malicious actions.
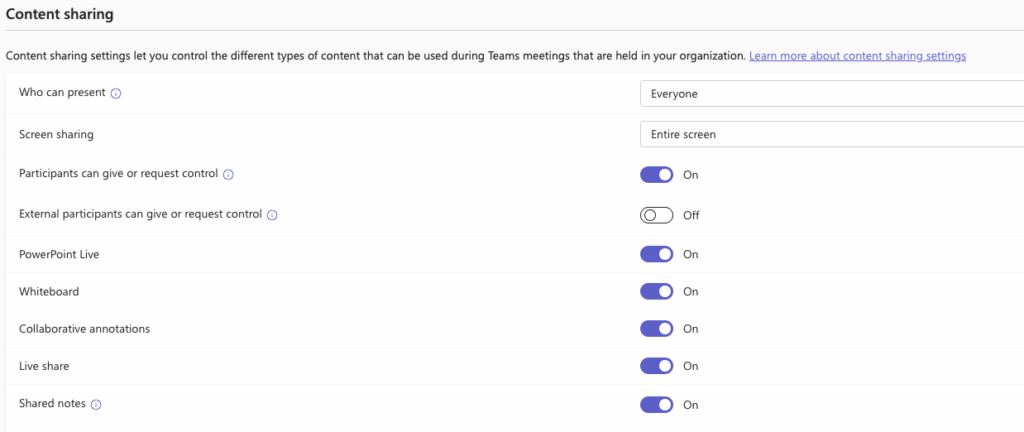
The most concerning development involves remote control capabilities. While Microsoft has implemented security controls that disable the “Give Control” and “Request Control” options by default for external participants, organizations that have modified these settings face significant exposure, according to the Axon Team.
Attackers can potentially gain full remote access to victim workstations through Teams’ integrated remote control features, eliminating the need for traditional Remote Monitoring and Management (RMM) tools like QuickAssist or AnyDesk.
Detection Methodologies
Security teams can identify these attacks through specific Microsoft 365 audit log entries that serve as digital forensic artifacts.
The primary indicators include ChatCreated events that establish new “OneOnOne” chats between attackers and victims, containing crucial metadata including Chat Thread IDs, sender display names, email addresses, and Organization IDs for both parties.
MessageSent logs complement ChatCreated entries by providing sender IP addresses and embedded URL information, though message content itself is not logged.
Additional forensic indicators include UserAccepted events when victims click “Accept” buttons in external sender pop-ups, and TeamsImpersonationDetected events triggered by Microsoft’s brand impersonation detection algorithms.
Advanced threat hunting requires monitoring for specific M365 audit log patterns, including ChatCreated operations with participant_info:has_foreign_tenant_users = true and communication_type = “OneOnOne” parameters.
As threat actors continue refining these techniques, organizations must implement comprehensive monitoring of Teams audit logs, user education programs focused on IT helpdesk impersonation tactics, and restrictive external communication policies to mitigate this evolving threat landscape.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.
