NodeBB, a popular open-source forum platform, has been found vulnerable to a critical SQL injection flaw in version 4.3.0.
The flaw, tracked as CVE-2025-50979, resides in the search-categories API endpoint, allowing unauthenticated, remote attackers to inject both boolean-based blind and PostgreSQL error-based payloads.
Successful exploitation could lead to unauthorized data access, information disclosure, or further system compromise.
Key Takeaways
1. NodeBB v4.3.0’s unsanitized search parameter allows unauthenticated SQL injection.
2. Exploits include Boolean-based blind and PostgreSQL error-based payloads.
3. Upgrade or use WAF rules, IP restrictions, and log monitoring.
SQL Injection Vulnerability
In NodeBB v4.3.0, the search parameter in the search-categories API is not properly sanitized before being passed to the underlying SQL query builder.
Consequently, specially crafted payloads can alter the intended logic of the SQL statements. Two proof-of-concept payloads demonstrate the severity:
Boolean-Based Blind Injection:
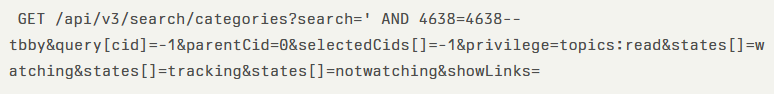
This payload appends AND 4638=4638 within the WHERE clause, which always evaluates to true, illustrating that the attacker can control conditional logic.
PostgreSQL Error-Based Injection:

This payload triggers a PostgreSQL casting error, revealing attack success through database error messages containing injected markers.
| Risk Factors | Details |
| Affected Products | NodeBB v4.3.0 |
| Impact | Unauthorized data access, information disclosure, and arbitrary SQL execution |
| Exploit Prerequisites | Remote HTTP access to; no authentication required |
| CVSS 3.1 Score | 9.8 (Critical) |
Mitigations
Attackers exploiting CVE-2025-50979 can read or modify sensitive data, escalate privileges within the forum, and execute arbitrary SQL commands.
Publicly exposed NodeBB instances are at particular risk, especially those configured without stringent firewall rules or running behind permissive reverse proxies.
NodeBB maintainers have released a patch in version 4.3.1, which properly escapes and parameterizes the search input.
Administrators are urged to upgrade immediately. For those unable to upgrade promptly, temporary mitigations include:
- Implementing a Web Application Firewall (WAF) rule to block requests containing SQL meta-characters .
- Restricting API access to trusted IP ranges via network ACLs or proxy configurations.
- Monitoring logs for suspicious patterns in the search parameter.
This vulnerability underscores the critical importance of input sanitization and the adoption of prepared statements for all SQL interactions.
Persistent vigilance and timely updates remain essential in defending community platforms like NodeBB from increasingly sophisticated injection attacks.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.
