Imagine this scenario: Your protection software is running perfectly. Systems are protected, definitions are up to date, behavioral analysis is active. Then, suddenly, files across your network start getting encrypted. Backups are being deleted. Ransom notes appear across your machines. Your security software shows nothing. No alerts, no detections, no blocked processes. How is this possible?
This isn’t a hypothetical situation. It’s a real attack technique that ransomware operators are actively using to bypass even sophisticated protection systems. The attack exploits a fundamental assumption in how security software operates: that the malicious process and the files being attacked are on the same machine. When that assumption breaks down, traditional defenses fail.
Malwarebytes ransomware protection works through multiple defensive layers. These include AI-based analysis, machine learning models, signature detection, runtime sandboxing, exploit mitigation, and web protection. Each layer stops threats at different stages. The Anti-Ransomware behavioral layer monitors actual file encryption behavior in real time. Malwarebytes continuously enhances all layers of its defense.
This article discusses a recent innovation in our Anti-Ransomware behavioral monitoring technology. The result is a comprehensive enhancement incorporating innovations in file monitoring, network session tracking, behavioral analysis, and real-time threat correlation.
Why traditional protection fails
To understand why a ransomware attack over a network is so effective, we need to understand how this technology typically works. The Anti-Ransomware component sits between applications and the file system, allowing it to see every file operation before it completes.
When a process tries to open, read, or write a file, specialized callbacks are triggered. Think of these as security checkpoints where the security driver can inspect what’s happening and decide whether to allow the operation. The software looks at patterns: Is this process rapidly encrypting many files? Is it adding suspicious extensions? Is it attempting to delete backup Copies? These behavioral indicators, when combined, signal ransomware.
This architecture works brilliantly when the ransomware process and the files being encrypted are on the same machine. The driver sees the process, tracks its behavior over time, builds a threat profile, and can block it before significant damage occurs.
But what happens when ransomware runs on one device and attacks files on another? For example, an attacker compromises an unprotected device, a legacy device without current protection or an unmanaged guest device, and uses it to encrypt files on protected systems through network shares. Your machine doesn’t see any suspicious programs running. It just looks like someone is accessing files over the network, which happens all the time.
This creates a perfect hiding spot for ransomware. On the attacking device, there might be no security software installed. On your main PC where files are being encrypted, the security software sees files changing but can’t tell which program is causing it. The connection between the malicious program and your files is hidden.
Multiple ransomware variants have adopted this technique. They use specific commands to target network folders and shared drives. These aren’t random attacks. They’re carefully designed to bypass security software through remote encryption
These aren’t opportunistic attacks. They’re carefully engineered for bypassing traditional anti-ransomware protection through remote encryption.
Two-part protection architecture
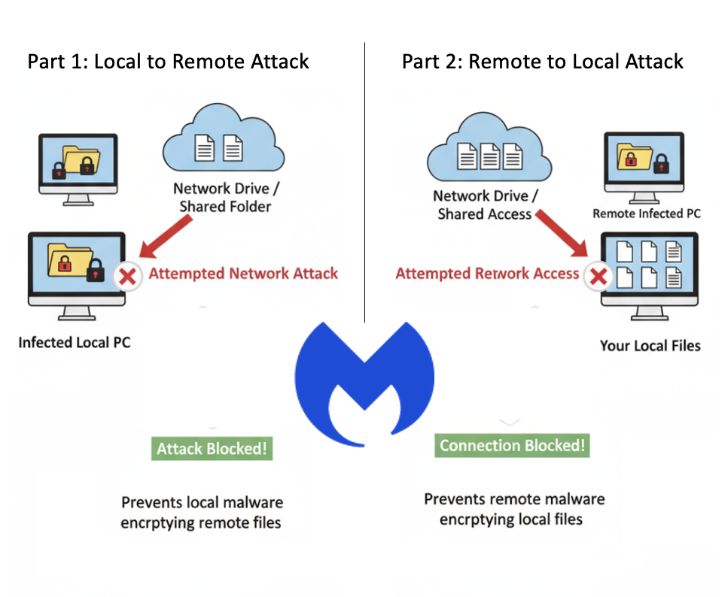
Solving this problem required addressing two distinct attack vectors. Part 1 involves a local process attacking remote files, while Part 2 involves a remote process attacking local files. Each required different technical approaches.
Part 1: Detecting local to remote attacks
When a program tries to access files on your network or shared folders, Malwarebytes checks if it’s behaving suspiciously. If the program is rapidly changing many files and creating ransom notes, the system builds a threat score in real time.
The key innovation is that Malwarebytes tracks local and network activity separately. A program might be safely working with files on your computer while attacking files on another device through the network. By monitoring both, we can catch ransomware without false alarms. When Malwarebytes detects ransomware behavior, it blocks the malicious program immediately, stopping the attack before your files are encrypted.
Part 2: Detecting remote to local attacks
The second challenge is harder: what if the ransomware is running on another device and attacking your files remotely? There’s no malicious program on your computer to block.
Our solution tracks network connections. When files are accessed from another device on your network, Windows keeps information about which device is connecting. Malwarebytes captures this information and watches for suspicious behavior, like rapidly changing many files, adding suspicious file extensions, or creating ransom notes. When we detect an attack coming from another device, we block that specific connection from accessing your files.
Innovation in ransomware protection
Our implementation operates through our specialized components. This architecture is essential for both performance and security. Every file operation goes through our filter, so we need to process decisions in microseconds to avoid impacting system responsiveness.
We implemented multiple optimization layers. First, we filter out file operations that categorically cannot be ransomware related. Opening a file for read only access is not a threat, so we skip detailed analysis. Operations that only query metadata happen constantly in Windows and can be safely ignored for ransomware detection purposes.
For operations that require analysis, we implemented a sophisticated indicator time-to-live (TTL) system. Behavioral indicators decay over time. This prevents false positives from legitimate activities like file synchronization tools or backup software.
The network session tracking component required deep integration with Windows networking. We extract session information by accessing internal structures that Windows uses for network file serving. Our exclusion system supports IPv4, IPv6, hostnames, and CIDR notation for network ranges.
What makes this protection different
Several factors distinguish the Malwarebytes approach from other solutions.
The first is comprehensiveness. Many security vendors address this partially. Remote processes attacking local files or where local processes attack remote files. An attacker who compromises a single endpoint can still encrypt the shared resources. Malwarebytes protects against both vectors.
Second is precision. Many solutions block entire network connections or lock accounts when they detect threats. Malwarebytes is more precise. We block only the specific malicious connection. Other activities from the same device continue working normally. Only the ransomware’s access is stopped.
Third is performance. Malwarebytes runs efficiently without slowing down your computer.
Fourth is proven protection. This technology has been tested and deployed across many different business and home networks. It is proven to work in real world situations.
The broader implications
This protection does more than just stop one type of ransomware attack. It represents a new way of thinking about network-aware security. The old approach treated each device separately, but that doesn’t work when attackers use network connections to spread threats. Security solutions need to understand that attacks can come from any device on the network and target any accessible files.
The technology we’ve built can do more than stop ransomware. The same system that tracks network connections and monitors suspicious behavior can help detect other threats, like someone trying to steal your data or access files they shouldn’t have permission to view.
Attackers will keep evolving their methods. The attacks we’re seeing now will become more sophisticated. They might try to disguise themselves as normal computer maintenance or file management. Our protection is designed to adapt. Because it watches for suspicious patterns of behavior rather than looking for specific known attacks, it can detect new variations without needing constant updates.
Ransomware keeps evolving, and attackers constantly find new ways to bypass security. Malwarebytes is committed to staying ahead with real innovation. This enhancement closes a critical gap that many security programs don’t address until it’s too late.
If you’re choosing security software or reviewing your current protection, ask yourself: Does it protect against ransomware that spreads through network shares? This is becoming increasingly important as more ransomware attacks use this technique.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.
