A new security investigation has uncovered 287 Chrome extensions that appear to secretly send users’ browsing data to remote servers, impacting an estimated 37.4 million installs.
That is roughly 1% of the global Chrome user base, based on the researchers’ estimate.
The researchers built an automated testing pipeline to catch “spying” behavior at scale.
They ran Chrome inside a Docker container, routed all browser traffic through a man-in-the-middle (MITM) proxy, and then visited controlled web addresses designed to reveal leakage patterns.
Instead of relying on extension descriptions or permissions alone, the team focused on what the extensions actually did on the network.
The findings were published in a public GitHub repository along with a detailed report and an HTML version for easier browsing.
Their key idea was simple: if an extension is harmless (for example, changing themes or managing tabs), its outbound traffic should not grow just because a visited URL becomes longer.
But if an extension is sending the full URL or parts of it to a third party, outbound traffic tends to rise in line with URL size.
The team measured this using a leakage metric: bytes_out=R⋅payload_size+b.
If R≥1.0, the endpoint was treated as “definitely leaking,” while 0.1≤R<1.0 was flagged as probable leakage for manual review.
Scale was a big part of the work. The report says the scanning effort consumed about 930 CPU-days, with an average run taking around 10 minutes per extension.
The researchers also avoided releasing full tooling details, arguing that publishing every implementation step could help extension operators change tactics and evade detection faster.
The alleged data collectors ranged from well-known analytics and data-broker ecosystems to smaller, obscure actors.
The report names groups and brands such as Similarweb, “Big Star Labs” (described as appearing linked to Similarweb), Curly Doggo, Offidocs, and other actors the researchers describe as Chinese, alongside multiple minor brokers.
The main concern is not only privacy: leaked URLs can contain personal identifiers, password reset links, document names, internal admin paths, and other clues useful for targeted attacks.
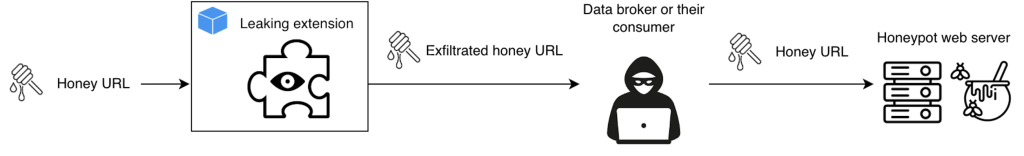
To understand downstream use, the team also created a honeypot using “honey URLs” and watched who tried to access them later.
Several IP ranges repeatedly hit the honeypot, including infrastructure associated in the report with Kontera (multiple AWS NAT endpoints), HashDit, and Blocksi AI Web Filter suggesting at least some scraped browsing data may be re-queried or resold after collection.
What users can do now:
- Remove extensions you don’t recognize or no longer use
- Prefer well-known publishers with clear privacy policies
- Review extension permissions (especially “Read and change all your data on websites you visit”)
- Watch for unusual network activity or browser slowdowns after installing an extension
- In organizations, limit extension installs via admin policy and allowlist only vetted add-ons
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google




