A new malware loader, dubbed Foxveil, that abuses trusted platforms such as Cloudflare Pages, Netlify, and Discord to stage and deliver malicious payloads while evading traditional detection methods.
Active since at least August 2025, the loader is used as an initial-stage component, establishing a foothold on victim machines, executing shellcode in memory, and preparing the environment for follow-on post‑exploitation tools.
Researchers have documented two variants, Foxveil v1 and v2, each using different injection and persistence techniques but sharing a common focus on stealth and defense evasion.
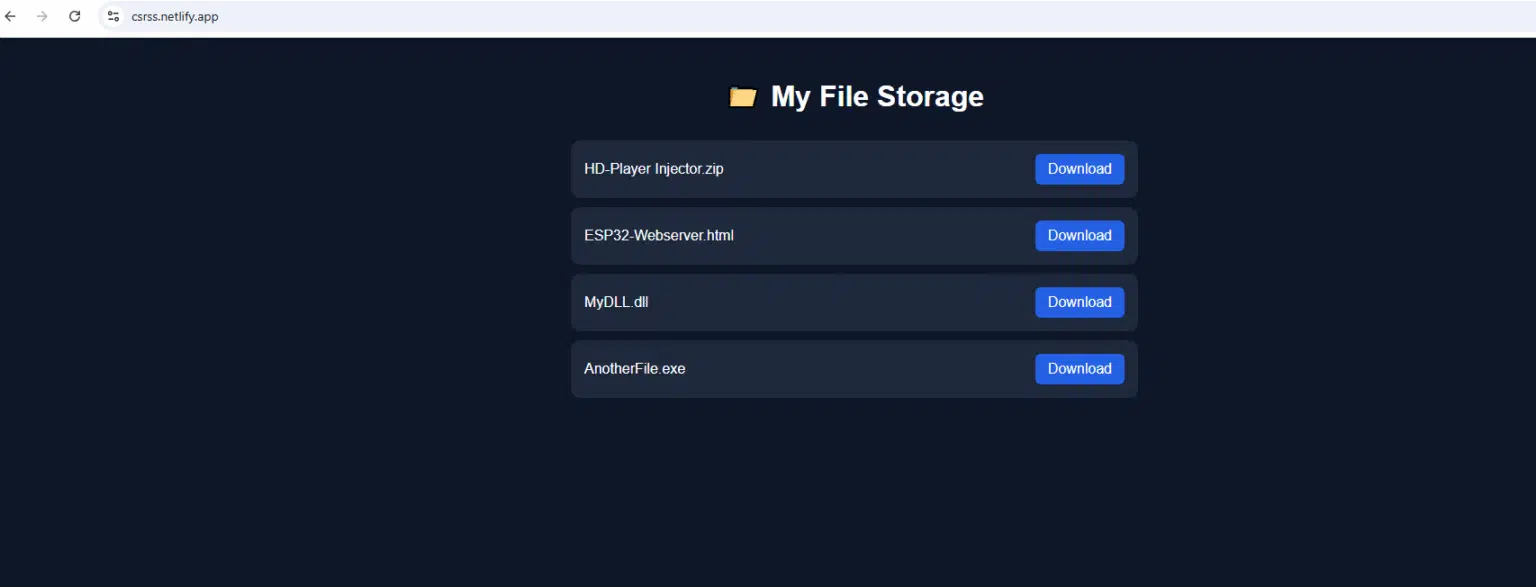
Instead of relying on obvious attacker‑owned infrastructure, Foxveil retrieves next‑stage payloads from content hosted on Cloudflare Pages, Netlify, and, in some cases, Discord attachment URLs.
This tactic allows malicious traffic to blend in with legitimate enterprise use of CDNs and collaboration tools, making it harder for defenders to rely on static blocklists or domain reputation alone.
Cato CTRL reported the malicious Netlify and Cloudflare staging to the affected providers, who restricted or removed the reported URLs in January 2026, and confirmed that the Discord attachment links used in the campaign had already expired and were no longer accessible.
Once a user runs a malicious EXE or DLL, Foxveil contacts threat actor‑controlled content on these platforms, downloads a shellcode stage (frequently generated with the Donut framework), and executes it through in‑memory injection.
This pattern reduces on‑disk artifacts and complicates traditional endpoint‑only detection approaches that depend on file scanning and simple URL filtering.
Foxveil Malware Loader
Foxveil v1 primarily uses Cloudflare Pages and Netlify as its staging sources and implements Early Bird Asynchronous Procedure Call (APC) injection into a newly spawned process masquerading as svchost.exe.
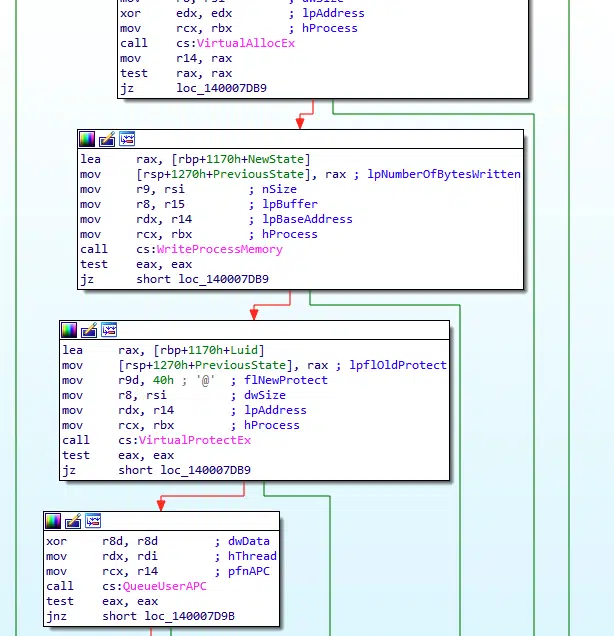
By queuing the APC before the target thread fully resumes, Early Bird‑style injection narrows the visibility window for security tools that monitor process execution and thread activity.
After successful injection, v1 registers itself as a Windows service named similarly to legitimate components and writes additional executables into C:WindowsSysWOW64, using filenames such as sms.exe, sihost.exe, taskhostw.exe, taskhostw1.exe, and audiodg.exe to mimic genuine Windows processes.
Foxveil v2 more commonly retrieves Donut‑generated shellcode from Discord attachments and performs self‑injection, executing the payload within the same process instead of spawning a new host.
Investigators also observed v2 writing next‑stage payloads into C:WindowsSysWOW64 and attempting to manipulate Microsoft Defender configuration via WMI calls to the MSFT_MpPreference class targeting the ExclusionPath for that directory.
Although the specific command sequence appeared to remove rather than add an exclusion, this interaction indicates an effort to tamper with built‑in defenses around the SysWOW64 path.
Post‑exploitation tooling
A notable feature of Foxveil is a runtime string‑mutation routine that scans for high‑signal analysis and C2‑related keywords such as “SilverFox,” “fox,” “payload,” “inject,” “shellcode,” “meterpreter,” “beacon,” URL prefixes, and file extensions, then replaces them with random values.
Netlify-hosted payloads using benign-looking names such as real1.exe or real2.exe, likely intended to appear non-malicious in logs and blend with ordinary download events.
This approach is unusual for a first‑stage loader and appears designed to remove easily searchable identifiers, break simple signatures, and slow reverse engineering by obscuring references to common post‑exploitation frameworks.
Telemetry from investigations suggests Foxveil functions as a staging loader for a later‑stage framework capable of lateral movement and additional payload delivery, with indicators pointing toward tools like Cobalt Strike.
Analysts observed localhost listening behavior on ports in the 9933–9934 range and relied on a Cobalt Strike configuration extractor during memory analysis, aligning with the loader’s focus on Donut‑generated shellcode and beacon‑related string mutation.
For defenders, Foxveil underscores the shift from monitoring “known bad” infrastructure to scrutinizing behavior and context, such as unusual process chains, staged downloads from trusted platforms, in‑memory shellcode injection, and suspicious writes into sensitive directories.
The Cato SASE Platform detects and blocks Foxveil activity before the staged payload can execute, using network‑aware controls to disrupt the intrusion early in the kill chain.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.