A new phishing campaign exploiting Microsoft’s OAuth 2.0 Device Authorization Grant flow to gain unauthorized and persistent access to Microsoft 365 accounts.
The sophisticated attack active since December 2025 specifically targets professionals and enterprises in North America, with over 44% of identified victims based in the United States. Sectors hit hardest include technology, manufacturing, and financial services.
This campaign stands out because it bypasses traditional credential theft and even multi-factor authentication (MFA).
Instead of tricking victims into entering usernames and passwords on fake pages, attackers manipulate the authentication flow itself.
KnowBe4 Threat Labs has detected a phishing campaign targeting North American businesses and professionals.
Victims unknowingly help them obtain valid OAuth access and refresh tokens, which provide full access to corporate Microsoft 365 environments.
How the Attack Works
The attack begins when an adversary registers a malicious application with Microsoft’s OAuth platform and generates a unique device code.
This code is embedded in a phishing email and sent to targeted employees. The email uses compelling social engineering tactics such as fake payment notifications, document sharing prompts, or voicemail alerts to convince recipients to click the embedded link.
Victims who follow the link are sent to an attacker-controlled landing page designed to appear legitimate.
They are prompted to enter their email and are shown “secure authentication” instructions, asking them to visit Microsoft’s official portal at microsoft.com/devicelogin.
Believing it to be part of a legitimate security verification, the user enters the attacker’s provided device code and completes the standard authentication process, including MFA.
Once the user authenticates, Microsoft issues OAuth tokens that grant full account access to the application associated with the device code.
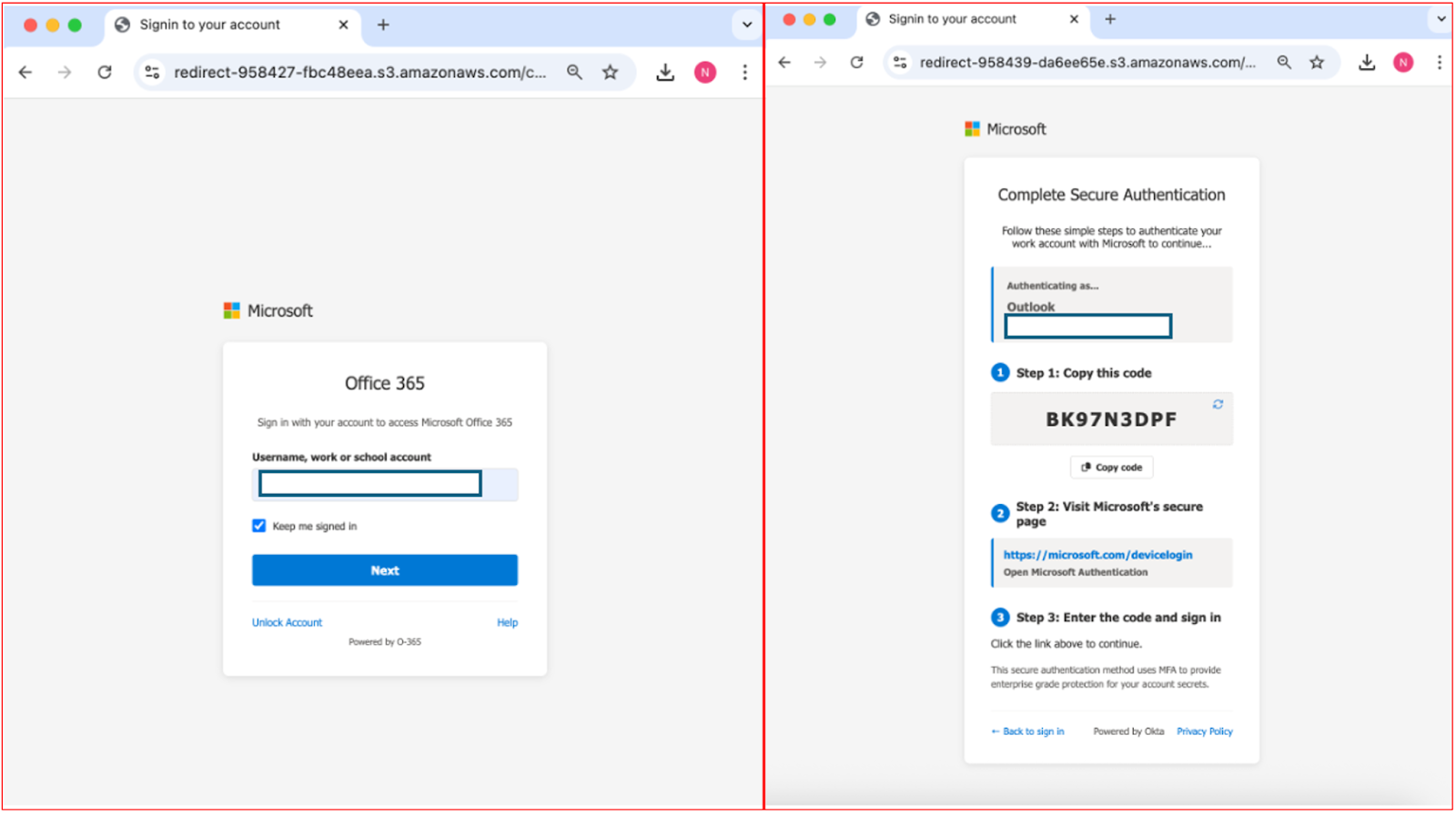
Because the attacker controls that application, they immediately receive the valid access and refresh tokens.
These tokens allow them to act as the user reading and sending emails, accessing OneDrive and SharePoint files code, scheduling meetings, and even performing administrative tasks without ever needing to re-enter credentials or trigger MFA challenges.
Mitigations
The most damaging aspect of this campaign is the persistence it enables. Refresh tokens let attackers continuously generate new access tokens, effectively maintaining an open backdoor to the victim’s Microsoft 365 account for as long as the tokens remain valid.
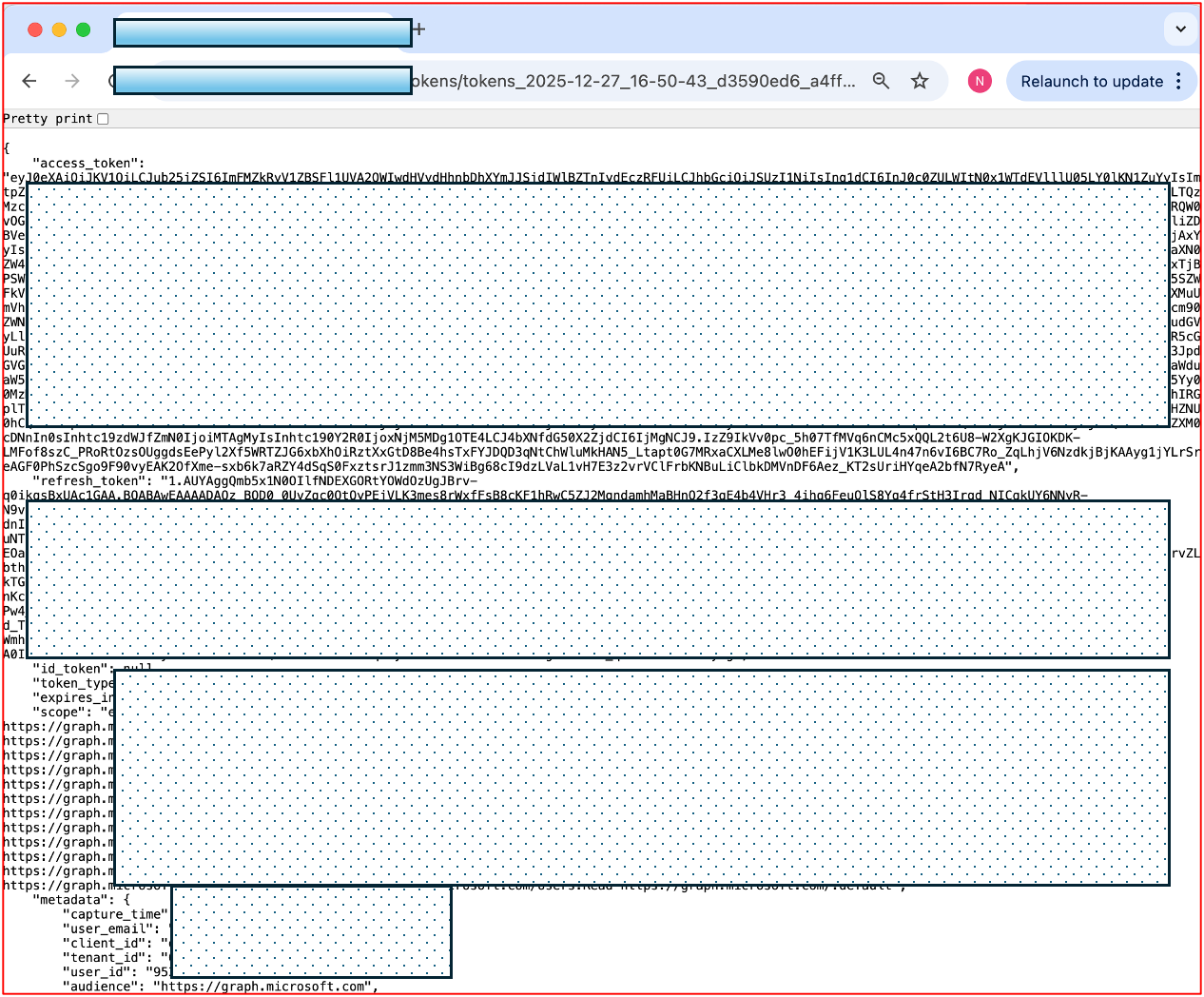
This means corporate data, intellectual property, and sensitive communications remain at risk even after password resets or MFA reconfigurations.
Organizations are urged to audit all recently consented OAuth applications within their Microsoft 365 environment. Admins should look for suspicious apps that users did not explicitly approve.
Additionally, IT teams should search email gateways and logs for recurring sender patterns or subject lines resembling fake payment or voicemail notifications.
Security professionals can reduce exposure by turning off the device code flow for nonessential use through Conditional Access policies.
Educating employees about OAuth-based phishing and emphasizing caution with unexpected login requests are equally critical.
As attackers increasingly exploit trusted authentication flows, defense strategies must evolve beyond password and MFA protections.
Continuous monitoring and tight application consent policies are now essential to preventing OAuth token abuse within enterprise ecosystems.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.