Hackers can repurpose the Cortex XDR Live Terminal feature as a stealthy, EDR‑trusted command‑and‑control (C2) channel, effectively turning a built‑in response tool into a “living off the land” backdoor on protected endpoints.
This abuse leverages the agent’s trusted communications and flexible remote‑execution capabilities to blend malicious operations into normal Cortex XDR traffic.
Cortex XDR Live Terminal provides defenders with remote shell access to endpoints for investigation and response via a secure channel managed by the Cortex agent.
Once a Live Terminal session is initiated from the Cortex XDR tenant, the agent connects to an operations socket such as https://[tenant].traps.paloaltonetworks.com/operations/socket and downloads a helper executable, commonly observed to power interactive operations on the endpoint.
This helper offers rich functionality, including command execution, PowerShell and Python execution, process inspection, and file system browsing with upload and download capabilities, all exposed through a graphical console intended for administrators.
For attackers with local administrator privileges on a host, this makes an attractive pre‑installed C2 implant: it is signed and trusted by the EDR, communicates over outbound TLS on port 443 to Palo Alto infrastructure, and is often excluded from deep TLS interception for privacy and reliability reasons.
With minimal tweaking, adversaries can execute arbitrary commands via this channel without triggering standard content or prevention rules, avoiding the need to deploy custom malware or maintain bespoke implants.
Cortex XDR Live Terminal
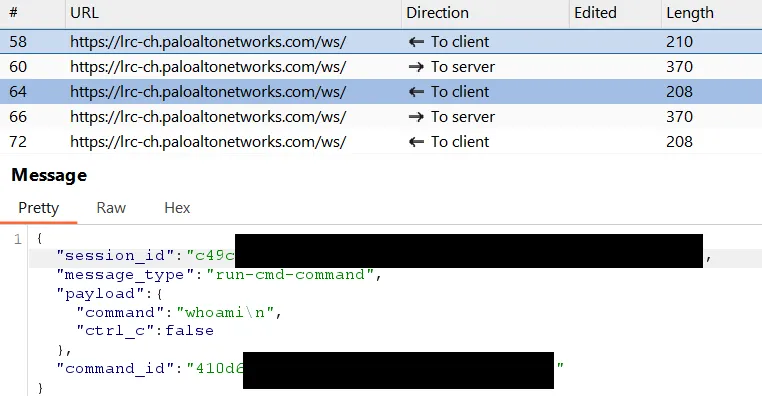
Researchers analyzing Cortex agent network traffic observed that Live Terminal communication relies on WebSockets over HTTPS to a regional endpoint such as lrc-ch.paloaltonetworks.com, without strong certificate or CA pinning by default.
A “certificate enforcement” mechanism exists and relies on an internal CA store, but this can be turned off or modified at the configuration and file‑system level on compromised systems.
By extracting and decompiling a packed Python 3.12 executable built with PyInstaller analysts identified the internal CA bundle used to validate certain connections and demonstrated that adding a custom certificate (for example, a trusted proxy CA) allows full interception and inspection of Live Terminal traffic.
Once interception is possible, the Live Terminal protocol revealed a relatively simple, unsigned command channel over WebSockets, where the server instructs the agent to execute actions and return output.
Crucially, there is no cryptographic command signing or mutual authentication beyond TLS, which means that if an attacker can redirect the agent to a rogue server trusted by the modified CA bundle, they can issue arbitrary commands that will be executed under the Cortex process context.
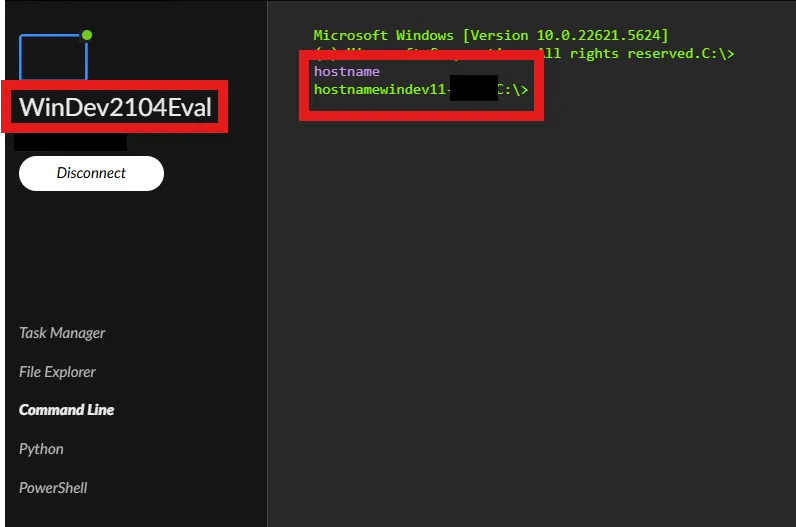
One demonstrated abuse method relies on a malicious or compromised Cortex tenant to perform a cross‑tenant hijack.
An attacker with their own Cortex tenant initiates a legitimate Live Terminal session, intercepts the initial WebSocket message containing the Live Terminal host and token parameters, and repurposes these values to launch on a victim host under their control.
When the payload runs with the supplied server and token, the victim machine establishes a Live Terminal session that appears in the attacker’s tenant console, granting full remote control via the official GUI.
The WebSocket message containing the host and token (-port 443 -server lrc-ch.paloaltonetworks.com -token [REDACTED] -d) is generated. The attacker must intercept this initial message and prevent it from reaching the legitimate agent on their own machine.
A second method avoids using a Cortex tenant entirely by re‑implementing the Live Terminal server‑side WebSocket logic.
Because the protocol is straightforward and lacks signatures, it can be replicated with modest effort potentially automated with LLM‑assisted coding to accept inbound connections from agents and respond with command instructions.
While nominally validates that its server parameter ends with the implementation applies this check to the entire URL string.
This allows trivial bypasses such as attacker.com/test.paloaltonetworks.com, which passes the suffix check but resolves to infrastructure controlled by the attacker once DNS or hosts‑file entries are manipulated.
Limitations and Detection
There are still practical hurdles for adversaries. Executing from its native location and hijacking its configuration typically requires local administrator privileges, and Cortex XDR ships with default content rules designed to detect or block when its own binaries are spawned by non‑standard parent processes.
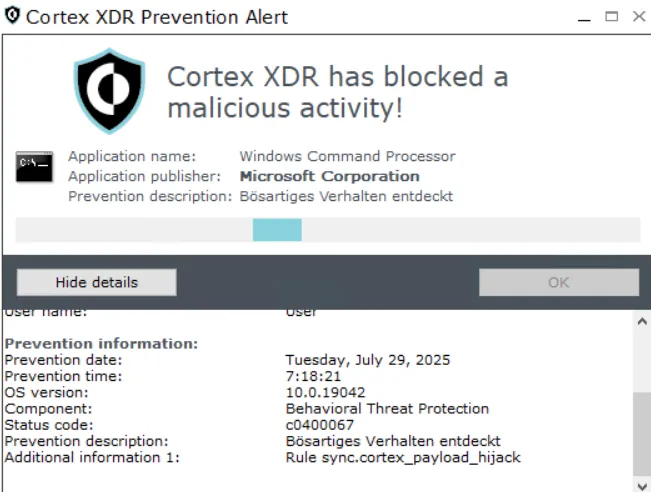
However, determined attackers with sufficient privileges can attempt to bypass these behavioral rules, and there are indications that fixes claimed to have been delivered in recent Cortex XDR content updates do not fully close the Live Terminal abuse paths validated during early 2026 testing.
Ultimately, this research underscores the need for secure‑by‑design features in EDR remote‑access tooling such as strict certificate pinning, mutual authentication features, and signed commands to prevent attackers from turning trusted response features into covert C2 channels.
Defenders should treat any instance launched outside the normal cyserver.exe parent relationship as highly suspicious and continuously monitor process‑creation telemetry for anomalous parent–child chains involving Cortex binaries.
Network defenders should also scrutinize outbound connections to Live Terminal endpoints and related FQDNs, including unexpected connections to suffixed URLs that do not align with official documentation, as these may represent attempts to redirect agents to attacker‑controlled servers.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.




