Digital Forensics, Investigation, and Response, 5th Edition presents a structured survey of the digital forensics discipline. The book spans foundational principles, platform specific analysis, specialized branches, and incident response integration.
About the author
Chuck Easttom has many years of practical experience across a wide range of computer science, mathematics, and related fields. He holds a Doctor of Science in Cyber Security, a Ph.D. in Nanotechnology, a Ph.D. in Computer Science, and four master’s degrees. He has authored over 40 computer science books and 80 research papers.
Inside the book
The emphasis of the opening section rests on methodology, repeatability, and evidentiary integrity. Chain of custody, documentation, and preservation standards receive sustained attention.
A full chapter examines U.S. legal frameworks that intersect with digital investigations. Statutes such as the Electronic Communications Privacy Act, the Computer Fraud and Abuse Act under 18 USC 1030, the USA PATRIOT Act, and the Digital Millennium Copyright Act appear in context. The text also outlines the Daubert standard and Federal Rules of Evidence relevant to expert testimony.
Expert reports and testimony receive detailed treatment. The book outlines how to document methods, support conclusions with references, and prepare for deposition and trial. Practitioners who serve as expert witnesses will find that this material connects investigative technique with litigation practice.
The discussion then shifts to formal methodologies and lab practices. Frameworks such as DoD forensic standards, DFRWS, and SWGDE are described alongside evidence handling procedures and analysis planning. The reader encounters practical guidance on minimizing interaction with original media, maintaining documentation trails, and securing evidence storage.
Tool coverage includes EnCase, Forensic Toolkit, OSForensics, The Sleuth Kit, Kali Linux, CAINE, and SIFT. Imaging procedures, RAID acquisition, and mathematical authentication of storage devices are addressed in operational detail. Certifications such as EnCE, AccessData ACE, and GIAC appear within the professional development context.
The technical depth increases in chapters on disk structure, file slack, hidden partitions, encryption, steganography, and file carving. These sections connect anti forensic techniques with investigative countermeasures, reinforcing the adversarial dimension of digital analysis.
Dedicated chapters examine Windows, Linux, and macOS artifacts. Windows coverage spans the registry, Prefetch, Shimcache, Amcache, SRUM, UserAssist, ShellBags, Volume Shadow Copy, and PowerShell. Linux sections address file systems, logs, shell history, and key command line tools. macOS analysis includes Unified Logs, KnowledgeC, AirDrop artifacts, and Target Disk Mode.
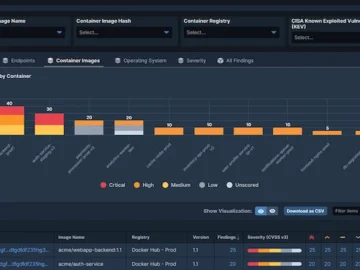
Email forensics covers headers, server artifacts, and legal constraints. Mobile analysis includes Android and iOS acquisition, SQLite databases, rooting, and chip off techniques. Network forensics addresses packet analysis, common tools, router evidence, firewall logs, and cloud environments. Memory forensics introduces capture methods and Volatility.
The structure moves from theory to artifact level examination across common enterprise systems.
Later chapters connect forensic work with incident response phases, including detection, containment, eradication, recovery, and follow up. Standards such as ISO 27001, ISO 27035, NIST 800 34, PCI DSS guidance, and GDPR breach notification requirements appear in operational context.
The closing section reviews machine learning, AI in cybersecurity, deepfakes, and related legal issues, presenting them as developing areas that require continued study.
Conclusion
Digital Forensics, Investigation, and Response, 5th Edition targets undergraduate and graduate programs in cybersecurity, information assurance, and computer science. It also aligns with practitioners preparing for certifications or transitioning into forensic roles. It’s suitable as a semester text or as a desk reference for analysts who require a consolidated overview of legal, technical, and procedural domains.
Digital investigations demand technical fluency, procedural discipline, and legal awareness. This text organizes those elements into a single reference that reflects the operational realities of contemporary digital forensics.