Malicious actors are abusing Go’s open-source ecosystem by deploying a backdoored crypto module that steals passwords and installs a Rekoobe Linux backdoor on developer and CI environments.
The package imitates Go’s trusted cryptography library to turn ordinary password prompts into a full compromise chain quietly.
On pkg.go.dev it appears as a normal cryptography library with expected folders like argon2, bcrypt, and ssh, helping it blend into dependency graphs.
The threat actor also added a dependency on the legitimate github.com/bitfield/script module to simplify HTTP calls and shell execution while keeping the surrounding codebase looking routine.
Socket’s Threat Research Team identified a fake module, GitHub.]com/xinfeisoft/crypto, designed to mirror the legitimate golang.org/x/crypto repository structure and subpackages.
Malicious Go Crypto Module
When an application calls the malicious ReadPassword, the function first captures the user’s typed secret via term.ReadPassword as normal.
It then writes the plaintext password to /usr/share/nano/.lock, an unusual location repurposed as a persistent stash for harvested credentials.
The key modification sits in ssh/terminal/terminal.go, where the ReadPassword helper is backdoored. Many command-line tools use this helper for SSH keys, database passwords, and API tokens, making it an attractive single hook point for harvesting high-value secrets.
Next, it fetches a GitHub Raw “update” page (vue-element-admin/public/update.html) to obtain a staging URL, exfiltrates the password via HTTP POST to that dynamically supplied endpoint, and finally pulls and executes attacker-provided shell content via /bin/sh.
Because the backdoor only triggers during real interactive password entry, it remains quiet in many automated test runs and low-coverage scans.
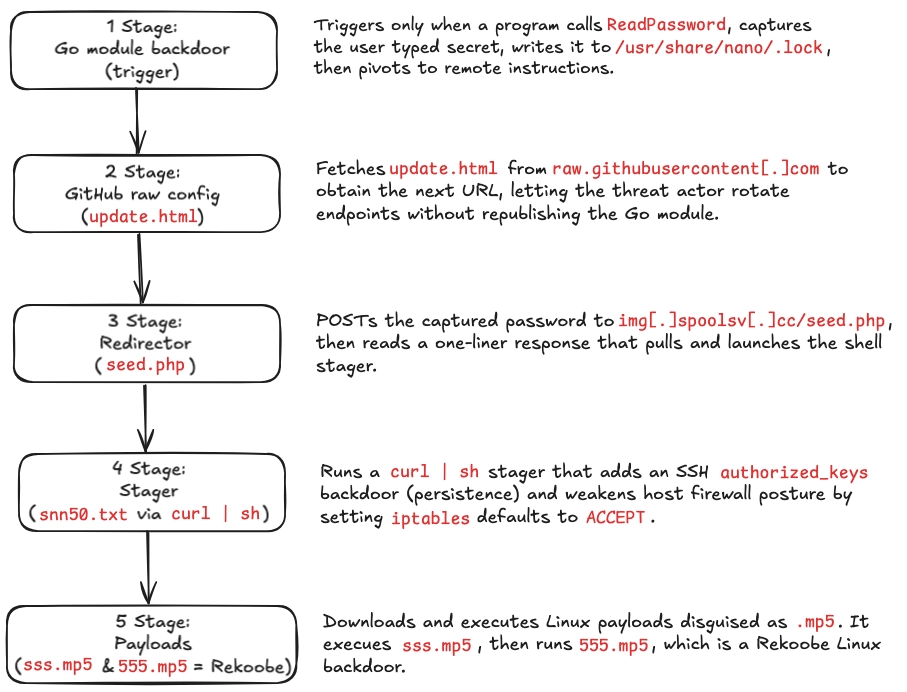
ReadPassword hook to Linux compromise (Source : Socket).Using GitHub Raw as an indirection layer also allows the threat actor to rotate downstream infrastructure (for example, changing seed.php hostnames) without republishing the Go module.
The shell script retrieved from the attacker’s infrastructure acts as a Linux stager that prepares the host and delivers additional payloads.
It appends an attacker-controlled SSH key to /home/ubuntu/.ssh/authorized_keys, sets iptables default policies to ACCEPT, and then downloads two binaries from img[.]spoolsv[.]cc disguised with .mp5 extensions (sss.mp5 and 555.mp5). After execution, the script deletes the temporary files to reduce on-disk artifacts and hinder forensic recovery.
Analysis shows sss.mp5 behaves as a helper component that checks connectivity and communicates over TCP 443 to 154[.]84[.]63[.]184, using traffic that does not match a standard TLS ClientHello.
The second payload, 555.mp5, is confirmed to be a Rekoobe Linux backdoor, a family previously linked to espionage-style activity and derived in part from Tiny SHell.
Packet captures from 555.mp5 execution revealed persistent, non-standard TLS-like communication with the same 154[.]84[.]63[.]184:443 endpoint, consistent with custom C2 running over port 443.
Threat Actor Infrastructure
The xinfeisoft GitHub account hosts four repositories, with crypto providing the backdoored module and vue-element-admin supplying the GitHub Raw pointer file used in staging.
Commit history shows the attacker actively maintained update.html, updating the staging URL from img.spoolsv[.]net/seed.php to img.spoolsv[.]cc/seed.php months after the module was published, suggesting an ongoing campaign rather than a one-off test.
Other repositories appear to play supporting roles, including content suitable for developer-side execution paths such as Git hooks.
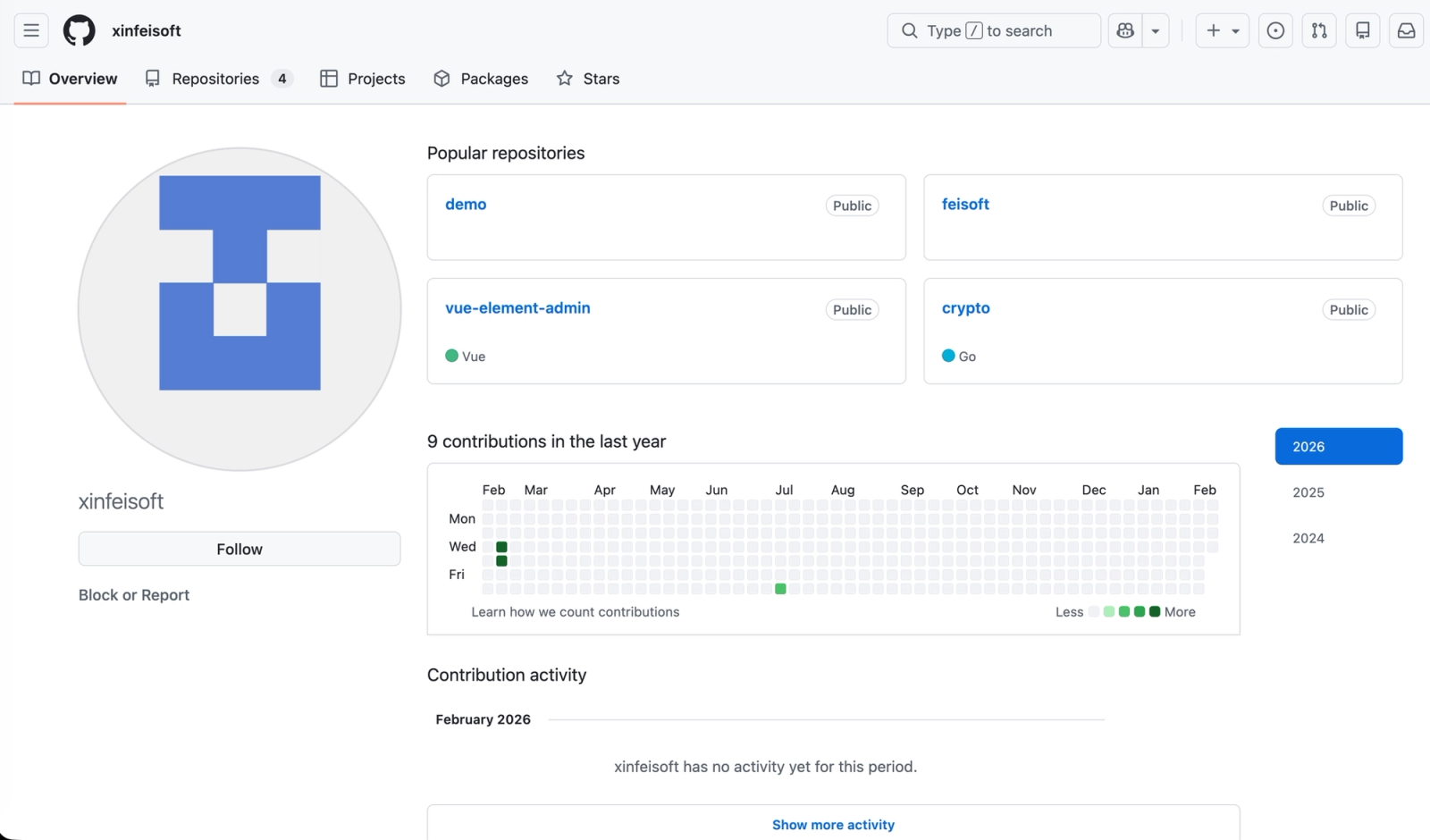
xinfeisoft account highlights the small set of public repositories used in the campaign (Source : Socket).Socket reports that as of early 2026, the public Go module proxy now blocks github[.]com/xinfeisoft/crypto as malicious and returns a 403 SECURITY ERROR instead of serving it, reducing exposure via default module resolution.
However, the module has appeared as a normal entry on pkg.go.dev, and any environment that previously vendored or cached it remains at risk if the code is still present in builds.
Socket’s AI Scanner now flags the package as known malware due to the backdoored ReadPassword path and its network-scripting behavior.
This campaign demonstrates how little effort is needed to weaponize a high-trust library boundary: copy a foundational module, hook a credential edge like ReadPassword, hide staging behind GitHub Raw, and pivot into curl | sh-based Linux compromise.
Defenders should treat Go module roots as supply chain boundaries, closely review go.mod and go.sum changes, and scrutinize new utility dependencies that introduce outbound HTTP or shell execution capabilities.
Detection engineering should prioritize behaviors such as writes to /usr/share/nano/.lock, GitHub Raw fetches immediately followed by dynamic POST destinations, curl | sh execution chains, modifications to authorized_keys, and iptables policy changes to ACCEPT.
Indicators of Compromise (IOCs)
| Category | Details |
|---|---|
| Malicious Go Module | github[.]com/xinfeisoft/crypto |
| Threat Actor GitHub Account | github[.]com/xinfeisoft |
| GitHub-Hosted Configuration | https://raw.githubusercontent[.]com/xinfeisoft/vue-element-admin/refs/heads/main/public/update[.]html |
| Payload Delivery Endpoints | https://img.spoolsv[.]cc/seed.phphttp://img.spoolsv[.]cc/snn50.txthttps://img.spoolsv[.]cc/sss.mp5https://img.spoolsv[.]cc/555.mp5https://img.spoolsv[.]net/seed.php (historical) |
| Related Domains | img.spoolsv[.]ccimg.spoolsv[.]netspoolsv[.]cc (parent domain, likely related)spoolsv[.]net (parent domain, likely related) |
| Network Indicators | 154[.]84[.]63[.]184 |
| Payload SHA256 Hashes | sss.mp5: 4afdb3f5914beb0ebe3b086db5a83cef1d3c3c4312d18eff672dd0f6be2146bc555.mp5: 8b0ec8d0318347874e117f1aed1b619892a7547308e437a20e02090e5f3d2da6 |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.



