A new Windows stealer dubbed BoryptGrab is being distributed through a large, ongoing campaign abusing fake GitHub repositories that pose as free tools, game cheats, and popular utilities.
The malware focuses on stealing browser data, cryptocurrency wallet information, and system details, while also grabbing screenshots, common files, Telegram data, Discord tokens, and stored passwords.
Attackers created more than a hundred public GitHub repositories using SEO‑stuffed READMEs so that search engines rank them near legitimate projects.
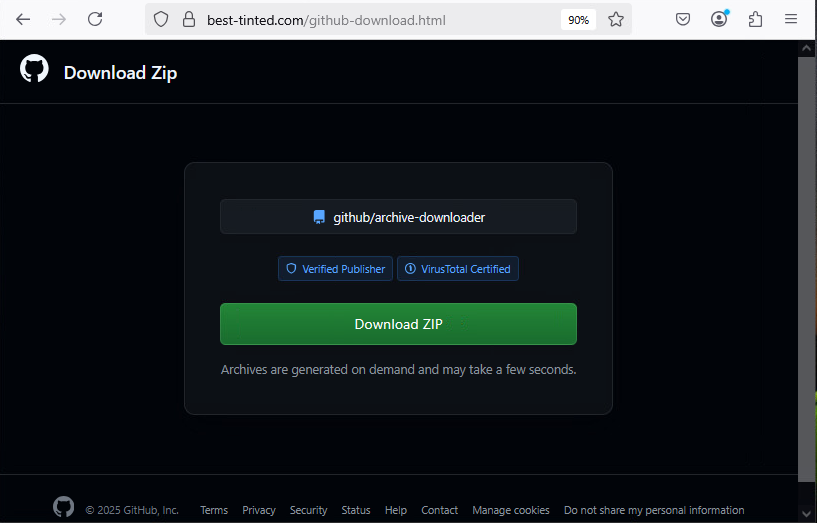
These repositories advertise items such as “Voicemod Pro download tool,” “Valorant performance boost,” “CS2 skin changers,” and other cracked or cheat‑style tools, often using ZIP filenames with or without “github-io” in their names to appear trustworthy.
When victims follow the README link, they are redirected through GitHub‑hosted pages containing Russian comments and base64/AES‑based URL redirection logic, eventually landing on a fake GitHub download page that dynamically generates a malicious ZIP archive.
The campaign dates back at least to April 2025, based on repository commits, with ZIP samples seen from late 2025, indicating an active and maturing ecosystem rather than a short‑lived operation.
Inside the ZIP, the infection can begin either via a DLL side‑loading chain or via a VBS/PowerShell downloader that pulls a launcher executable from attacker‑controlled infrastructure.
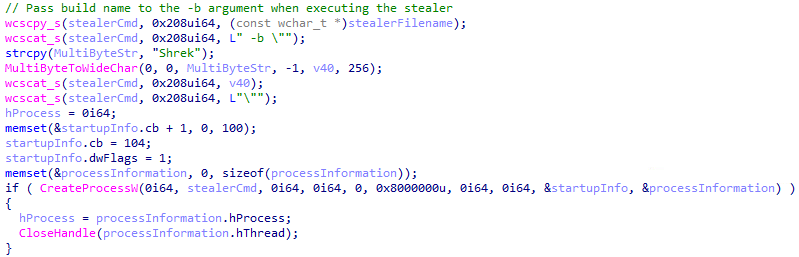
These launchers frequently talk to servers on port 5466 and can pass “build names” such as Shrek, Leon, CryptoByte, Sonic, or Yaropolk to request specific payloads and track infection branches.
BoryptGrab Malware
In one route, an executable side‑loads a malicious libcurl.dll that decrypts an embedded launcher payload using XOR plus AES‑CBC, then runs it to download the main BoryptGrab stealer as well as optional extra payloads.
VBS scripts that decode PowerShell commands, add Microsoft Defender exclusions, and fetch a C/C++ launcher which then retrieves BoryptGrab via HTTP.
Additional variants employ a .NET stub that embeds a base64‑encoded VBS downloader, or include a Golang‑based downloader called HeaconLoad directly inside the ZIP.
HeaconLoad persists via Run‑key registry entries and scheduled tasks, beacons to the attacker via HTTP POST on port 8088 with system info and a hardcoded tag, and when instructed, downloads and unzips bundles, executing the first binary inside.
The infrastructure can also deliver obfuscated Vidar stealer variants via an /api/custom_exe?build={BUILD_NAME} endpoint, using XOR‑encrypted strings, opaque predicates, and dynamic API resolution to hinder analysis while exfiltrating data in Vidar‑style HTTP POST traffic.
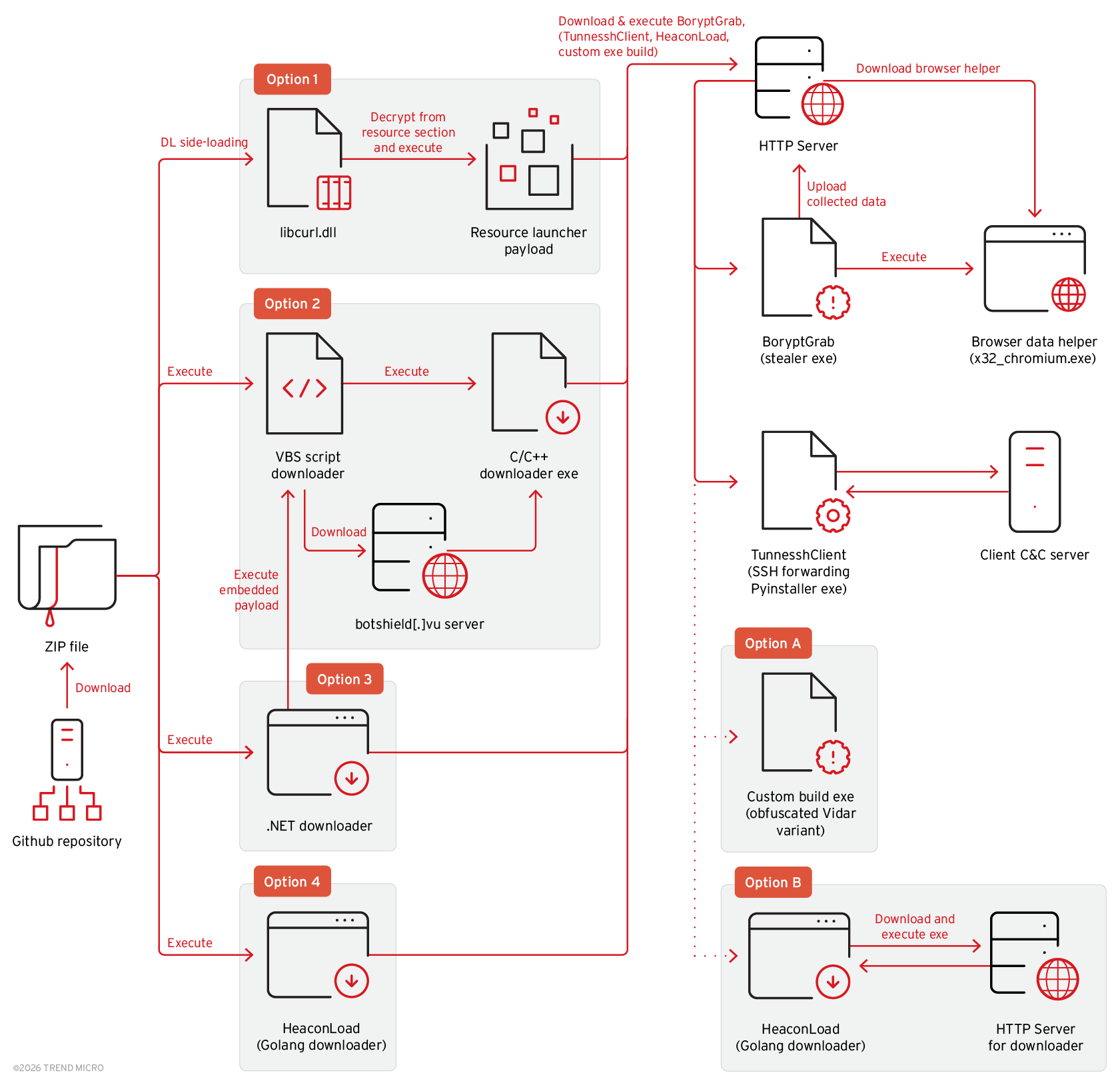
Certain chains further deploy TunnesshClient, a PyInstaller‑packed backdoor that establishes a reverse SSH tunnel to attacker servers.
TunnesshClient first requests a challenge and credentials over HTTP, derives SSH keys, and then sets up remote port forwarding so attackers can run commands, list and exfiltrate files, upload data, or use the victim as a SOCKS5 proxy.
One variant instead spins up a local SSH server on the victim and forwards credentials to the operator, who can then pivot traffic through the compromised host.
What BoryptGrab steals and why it matters
BoryptGrab itself is a C/C++ information stealer with anti‑VM and anti‑analysis checks that inspect registry keys, VM artifacts, and process names before proceeding.
URLs vary across the GitHub repositories we identified, similar Russian-language comments and URL-fetching logic were also present in other GitHub repositories we found for this campaign.
It supports command‑line arguments such as –output-path to control where it stores loot and –build-name to tag each infection, falling back to defaults or hardcoded identifiers (for example CryptoByte, Shrek, Sonic, Yaropolk, and others) when no value is provided.
The stealer focuses heavily on browser credential theft, targeting Chrome, Edge, Firefox, Opera, Brave, Vivaldi, Yandex, and others, and integrates code from public GitHub projects that bypass Chrome App‑Bound Encryption to decrypt stored passwords.
It loads an encrypted internal payload (PAYLOAD_DLL) that handles browser data extraction and also logs installed applications along with a hardcoded timestamp.
For cryptocurrency, BoryptGrab searches directories for many popular desktop wallets and extensions, including Exodus, Electrum, Ledger Live, Atomic, Binance, Wasabi, Trezor, and dozens more, then collects wallet files, captures a screenshot, and gathers system information.
Beyond credentials and wallets, BoryptGrab runs a “Filegraber” module to harvest files with specific extensions from common folders, steals Telegram data, and in newer builds also captures Discord tokens to expand account takeover opportunities.
Finally, it compresses all collected data and uploads it to the attacker’s server; in some variants it then pulls and launches TunnesshClient to establish longer‑term remote access over encrypted SSH tunnels.
Russian‑language comments and log strings observed in multiple malware components, plus IP addresses located in Russia, suggest a likely Russian‑speaking threat actor behind this campaign, though formal attribution remains unconfirmed.
For defenders, the combination of SEO‑poisoned GitHub repositories, layered downloaders, multiple stealers, and SSH‑based backdoors highlights the need to treat “free” development tools and cheat utilities as high‑risk, enforce application control, and closely monitor outbound HTTP and SSH traffic for suspicious patterns tied to this evolving threat.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.