A large-scale spear-phishing campaign distributing a VIP Keylogger variant sold as Malware-as-a-Service (MaaS).
The campaign employs steganography, in-memory execution, and modular payload design to evade defenses while harvesting credentials across browsers, email clients, and collaboration tools.
Researchers observed fraudulent purchase-order emails that encouraged victims to open an attached RAR file.
The compressed archive contained an executable disguised as a spreadsheet – ÜRÜN ÇİZİMİ VE TEKNİK ÖZELLİKLERİ_xlsx.exe. Once executed, the file loads VIP_Keylogger directly into memory without dropping any components to disk, making detection significantly harder.
VirusTotal telemetry revealed multiple samples of this campaign targeting victims across different countries.
A recent investigation into malicious samples uploaded to VirusTotal has uncovered a large-scale spear-phishing campaign distributing a VIP Keylogger.
While the social engineering lures and packaging layouts varied, the core payload behavior and in-memory execution style remained consistent.
MaaS VIP Keylogger Campaign
In the first observed case, the malware was a .NET Portable Executable (PE) containing two DLLs hidden within its resource section using steganography.
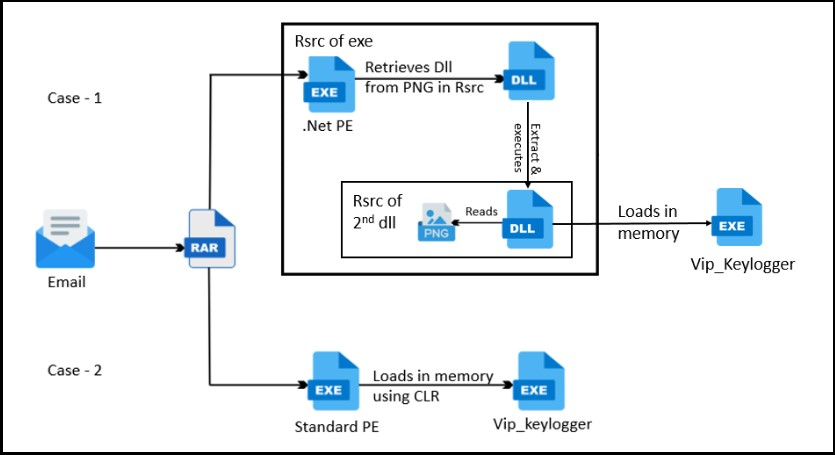
The first DLL (Turboboost.dll) extracted the second DLL (Vertical bars.dll), which concealed the final payload as an encrypted PNG file.
The malware unpacked VIP_Keylogger by dynamically retrieving functions from Kernel32.dll and Ntdll.dll such as CreateProcessA, VirtualAllocEx, WriteProcessMemory, and ResumeThread typical indicators of process hollowing.
In another sample, the malicious PE contained AES-encrypted bytes inside the .data section.
After decrypting these in memory, the loader disabled Windows AMSI (Antimalware Scan Interface) and ETW (Event Tracing for Windows) before executing the keylogger via the CLR runtime.
The VIP_Keylogger samples suggest a MaaS (Malware-as-a-Service) distribution model, with some client-customized versions missing certain functions like Anti-VM detection, Process Killer, and Downloader modules.
Credential Theft Capabilities
Once active, the keylogger steals credentials, browser cookies, form autofills, and stored payment data from more than 40 Chromium-based browsers, including Chrome, Brave, Vivaldi, and Opera, storing them in a SQLite database files.
For browsers using AES-256 GCM encryption (“V10” marker), it extracts the master key and decrypts passwords via Windows DPAPI.
For Mozilla-based browsers such as Firefox, Waterfox, or Thunderbird, it leverages PK11SDR_Decrypt from nss3.dll to retrieve saved logins.
The stealer also collects email credentials from Outlook (via registry inspection), Foxmail, and Thunderbird profile data, decrypting the passwords using the Windows Unprotect API or PK11SDR mechanisms.
Additionally, the malware harvests Discord tokens, FileZilla server credentials, and Pidgin chat accounts by parsing plaintext configuration files like recentservers.xml and accounts.xml.
Stolen information is exfiltrated via multiple channels FTP, Telegram, Discord, web POST requests, and most notably SMTP.
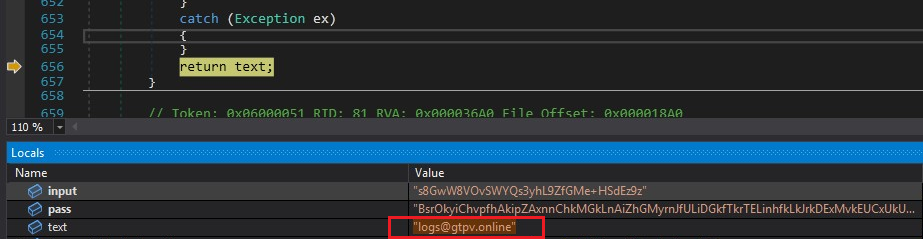
Analyzed samples were found sending stolen credentials from logs@gtpv[.]online to log@gtpv[.]online using hosting2[.]ro.hostsailor[.]com over port 587.
Despite having modules for clipboard capture, screenshots, and Wi-Fi credential theft, these features remained dormant in the observed samples.

The campaign underscores how stealthy social engineering and in-memory execution can mask powerful MaaS keyloggers.
Organizations are urged to deploy reputable endpoint protection solutions, enable heuristic scanning, and train users to recognize phishing emails disguised as order or invoice attachments.
IOCs
| Hash | Detection Name |
| D1DF5D64C430B79F7E0E382521E96A14 | Trojan ( 700000211 ) |
| E7C42F2D0FF38F1B9F51DC5D745418F5 | Trojan ( 006d73c21 ) |
| EA72845A790DA66A7870DA4DA8924EB3 | Trojan ( 005d5f371 ) |
| 694C313B660123F393332C2F0F7072B5 | Spyware ( 004bf6371 ) |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.