The secure messaging platform Signal recently confirmed active, targeted phishing campaigns resulting in severe account takeovers.
These sophisticated attacks have successfully compromised the accounts of high-profile individuals, specifically targeting government officials and journalists.
Despite these high-profile breaches, Signal explicitly clarified that its underlying infrastructure and end-to-end encryption protocols remain robust and completely uncompromised.
The breaches stem entirely from external social engineering tactics rather than technical vulnerabilities within the application itself.
Sophisticated Social Engineering Tactics
Threat actors execute these account takeovers by manipulating users into voluntarily surrendering their sensitive authentication data, as reported by Signal.
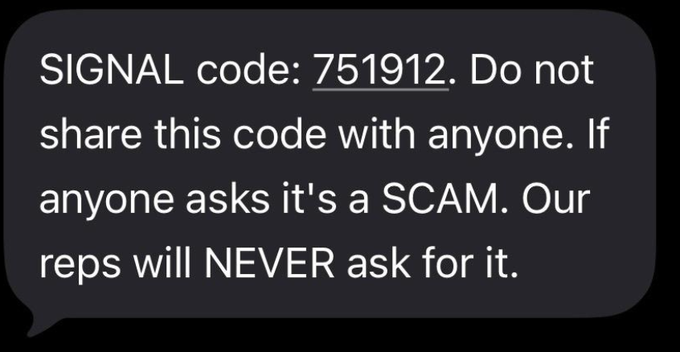
The primary objective of the attackers is to harvest two critical pieces of information: the victim’s SMS verification code and their Signal personal identification number (PIN).
Cybercriminals achieve this by impersonating trusted contacts or deploying deceptive personas, most notably a fabricated “Signal Support Bot.”
When attackers initiate contact using these fraudulent accounts, they rely on psychological manipulation to create a false sense of urgency.
They trick the victim into sharing the one-time SMS code sent to their mobile device.
Because Signal uses phone numbers and SMS verification for device registration, capturing this code allows the attacker to register the victim’s phone number on an attacker-controlled device.
Once the attacker successfully links the account to their device, they effectively lock the legitimate user out.
While Signal’s security architecture prevents the attacker from accessing the victim’s past message history, the threat actor can impersonate the victim to send new messages, further propagating the phishing cycle to the victim’s contact list.
Mitigation and Security Recommendations
Defending against these account takeover attacks requires strict user awareness and proactive security configurations.
Signal emphasizes that its official support team will never initiate contact through in-app messages, text messages, or social media platforms to request a PIN or verification code.
Any request for a Signal-related code, regardless of the sender’s apparent identity, is definitively a scam.
While Signal continues to develop technical safeguards and interface warnings to alert users, individuals must implement robust account protection measures to secure their communication.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.