OpenClaw’s rapid rise has accidentally exposed how far GitHub’s advisory ecosystem has drifted from traditional CVE‑centric vulnerability tracking.
Within roughly three weeks, the project published more than 200 GitHub Security Advisories (GHSA), and its advisory page now lists around 255 disclosures covering command execution controls, authorization checks, allowlist logic, and plugin boundaries.
Only a subset of these issues currently have CVE identifiers, creating an immediate gap between what developers can see in GitHub and what enterprise tools detect through CVE feeds.
That gap came into focus when vulnerability intelligence firm VulnCheck asked the CVE Project’s researcher working group to “call DIBS” on 170 OpenClaw advisories that lacked CVEs.
OpenClaw, a self‑hosted AI agent platform, went from launch to GitHub’s most‑starred repository in weeks and then became a live‑fire test of disclosure plumbing.
DIBS is an informal signal among CVE Numbering Authorities (CNAs) that an organization intends to evaluate a specific vulnerability and potentially assign a CVE identifier.
VulnCheck framed the request around customer interest and the risk of weaponization, arguing that having CVEs would make it easier to track and prioritize these issues before they were actively exploited.
MITRE’s TL‑Root pushed back, stressing that DIBS is meant to identify individual vulnerabilities meeting CVE criteria, not to treat a single supplier as a “hot” category for bulk reservation.

The issue was eventually closed, with VulnCheck acknowledging that a mass DIBS call was the wrong fit, though individual advisories may still receive CVEs through other channels.
GHSA Convenience vs CVE Visibility
The OpenClaw case highlights a structural tension. Publishing a GHSA is low‑friction: a researcher reports, a maintainer publishes, and no external coordination is required.
Requesting a CVE, by contrast, means working with a CNA, formatting metadata, and waiting for the process to complete, so many projects now default to GHSA‑only disclosure and add CVEs later, if at all.
Yet most enterprise scanners, SBOM tools, patch pipelines, and compliance frameworks still revolve around CVE identifiers, so a vulnerability disclosed only as a GHSA may be effectively invisible to those systems.
That blind spot is amplified by scale. A 2024 UC Irvine investigation found that as of April that year, the GitHub Advisory Database contained more than 213,000 unreviewed advisories, with fewer than six reviewed per day implying roughly 95 years to clear the backlog at current rates.
Unreviewed advisories do not trigger Dependabot alerts, meaning downstream projects may never be notified that they rely on vulnerable dependencies.
Recent academic work suggests this imbalance is not going away. A 2026 study led by researchers at Brazil’s Fluminense Federal University analyzed 288,604 GHSAs and found that only about 8.2% had been GitHub‑reviewed, leaving more than 265,000 records unreviewed.

The authors note that GitHub‑reviewed advisories are the ones most likely to propagate into dependency alerts and security tooling, reinforcing the visibility gap between “fully processed” vulnerabilities and the rest.
The table below shows how the advisory backlog and review rate align with the OpenClaw surge:
| Aspect | Data point |
|---|---|
| OpenClaw repo advisories | ~255 GHSAs in weeks of scrutiny socket+1 |
| UC Irvine 2024 snapshot | 213,594 unreviewed advisories, ~95‑year backlog sp2024.ieee-security+1 |
| 2026 FFRJ study | 288,604 total GHSAs, 8.2% reviewed arxiv |
Independent Tracking and Community
OpenClaw’s disclosure burst has already inspired independent tracking in an attempt to bridge these systems.
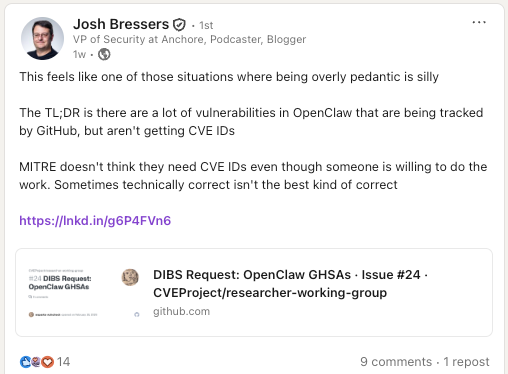
Josh Bressers, VP of Security at Anchore, contends that MITRE was being overly procedural when someone was willing to do the work.
Security engineer Jerry Gamblin built an OpenClaw CVE and Security Advisory Tracker that reconciles repo‑level advisories, the global GitHub Advisory Database, and the CVE Project’s cvelistV5, including renamed project identifiers like Clawdbot and Moltbot, and adds fixed‑version data to avoid misreading counts as unpatched exposure.
The DIBS debate also surfaced deeper disagreements about how much the ecosystem should still rely on CVE as a single source of truth.
Some practitioners argue that modern vulnerability management already depends on multiple identifiers and sources, and question the need for CVEs when detailed GHSAs exist in a public database.
Others counter that many organizations still ignore issues without CVE IDs, making non‑CVE‑backed advisories second‑class even as GHSA usage accelerates.
For AI agent platforms like OpenClaw, which combine automation, integrations, and extensible plugins, this fragmentation is likely to become a recurring pattern.
High‑velocity advisory streams will stress both GitHub and CVE processes, forcing vendors, researchers, and enterprises to decide whether to double down on CVE alignment or adapt their tooling to treat GHSAs and other advisory systems as first‑class signals.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.