Threat actors are increasingly exploiting legitimate Remote Monitoring and Management (RMM) tools to breach corporate networks and establish persistent access.
This tactic allows attackers to bypass traditional security defenses by blending malicious activities with routine administrative tasks.
The Surge of RMM Abuse
The exploitation of remote management software has become a primary initial access vector for cybercriminals across all skill levels.
Recent intelligence indicates that RMM abuse surged by 277% last year, representing nearly a quarter of all observed security incidents.
Attackers are abandoning conventional malware in favor of building operational playbooks entirely around these trusted administrative applications to drop payloads and steal credentials.
A prominent technique observed in recent intrusions is the daisy-chaining of distinct remote access tools to fragment security telemetry.
Hackers abuse vulnerability management software, such as Action1, to silently deploy secondary remote access clients like ScreenConnect via Microsoft Installer packages.
This approach relies on legitimately signed deployment packages, complicating attribution and containment efforts for network defenders.
Lower-skilled attackers are increasingly relying on Large Language Models to generate the deployment scripts used in these intrusions.
While these scripts successfully parse browser history for cryptocurrency and financial platforms, they often lack technical maturity.
In several observed cases, the generated code failed to properly implement data exfiltration APIs, leaving the harvested data stranded locally.
Deceptive Phishing Lures
Threat actors frequently deploy these administrative tools through broad social engineering campaigns centered around predictable themes.
Victims are manipulated into downloading malicious files through highly tailored psychological triggers.
- Attackers impersonate government entities like the Social Security Administration during tax season.
- Campaigns distribute fake meeting RSVP and party invitations that secretly execute installer files.
- Phishing pages target mobile users with fake online greeting cards designed specifically for credential harvesting.
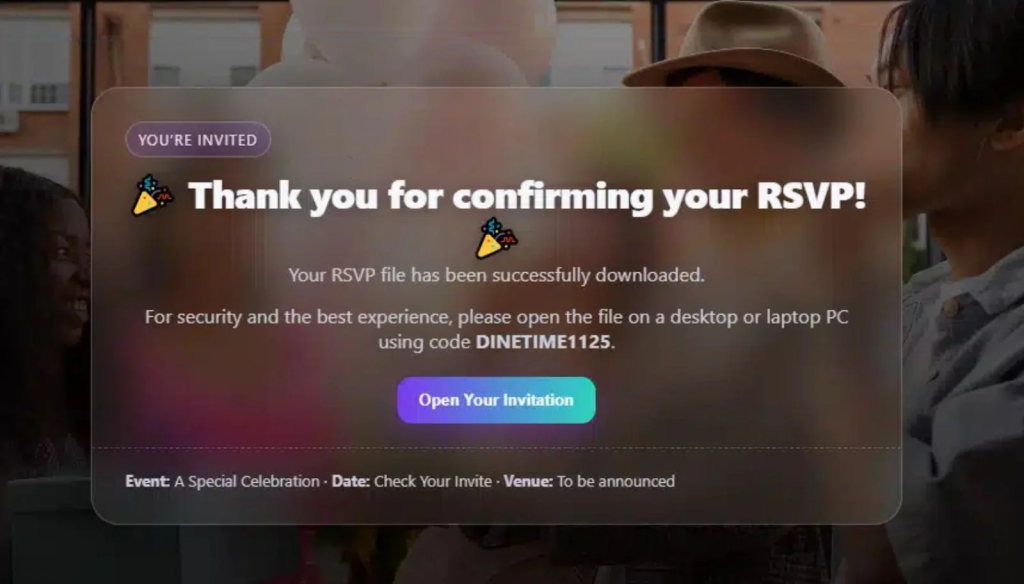
Victims are often funneled toward malicious GitHub repositories hosting custom domains and disguised installer files.
These repositories utilize functional phishing pages that cycle through multiple browser-native download techniques, such as hidden iframes and programmatic anchor clicks, to force payload delivery.
Additionally, attackers use lightweight client-side filtering to block non-Windows devices from accessing the malicious downloads.
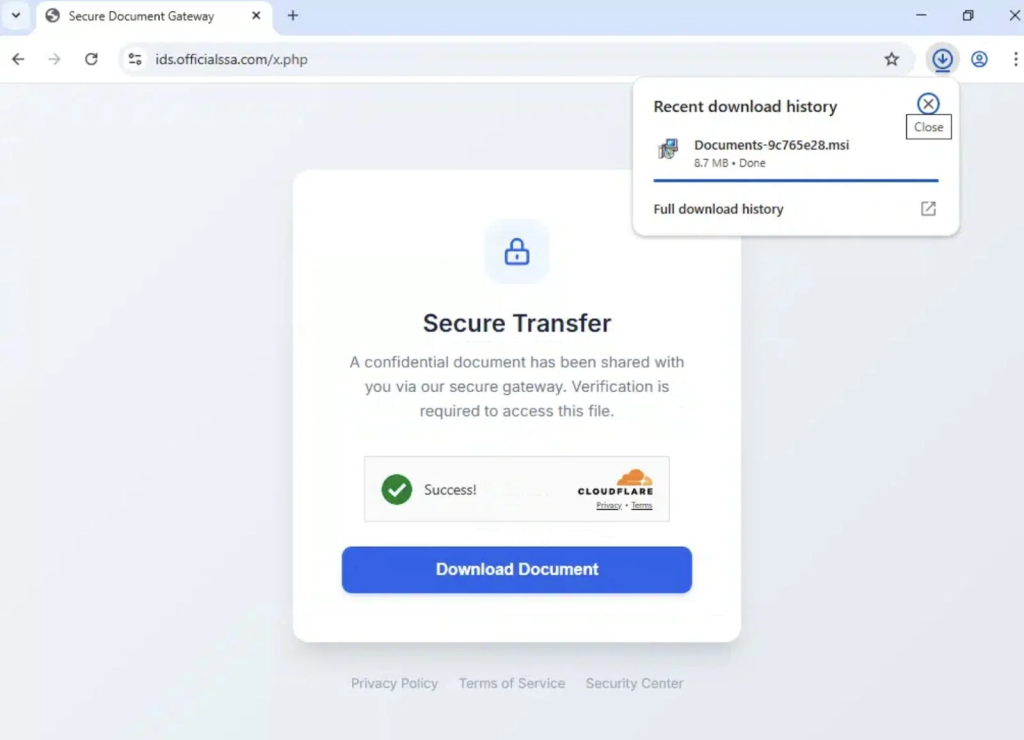
To ensure their malicious downloads remain online, attackers frequently abuse trusted services like Cloudflare to shield their hosting infrastructure.
This adds a layer of friction for defenders by obscuring backend details, request telemetry, and geographic locations.
Meanwhile, the presence of secure transfer messaging and recognizable branding reinforces the illusion of legitimacy for the targeted victim.
Security researchers from Huntress recently gained firsthand visibility into these campaigns by observing threat actors registering on defensive platforms to test their evasion capabilities.
Operating from virtual private servers, the attackers utilized browser extensions like email extractors and proxy routers to harvest credentials and maintain operational safety.
They subsequently leveraged purchased credential combo lists to systematically infiltrate victim email accounts and linked banking portals.
Defending Corporate Networks
Combatting this rising threat requires organizations to immediately treat unapproved remote management installations as critical security events.
Industry experts recommend adopting a defense-in-depth approach that restricts the unauthorized use of administrative utilities.
- Organizations must implement strict allow-listing for all authorized administrative software.
- Security teams should treat unverified software deployments originating from user-writable paths as highly suspicious.
- Defenders must focus on sharing behavioral patterns, such as parent-child process relationships, rather than static indicators.
- IT departments need to scrutinize trial-based usage and demand greater telemetry transparency from software vendors.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.