The second half of 2022 marked a significant turning point in the security landscape. In several high-profile incidents, application programming interfaces (APIs) emerged as a primary attack vector, posing a new and significant threat to organizations’ security posture, according to Cequence Security.
“API breaches have plagued numerous high-profile organizations in recent months, elevating the need for CISOs to prioritise API protection. Attackers are getting more creative and specific in their tactics, and traditional protection techniques are no longer enough,” said Ameya Talwalkar, CEO of Cequence Security.
“As attack automation becomes an increasingly prevalent threat against APIs, it’s critical that organizations have the tools, knowledge and expertise to defend against them in real- time,” Talwalkar added.
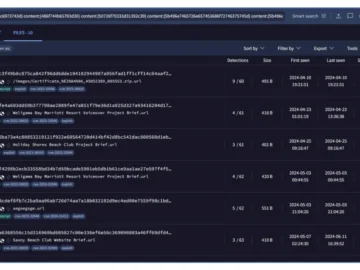
Automated API threat landscape
- Shadow APIs spike 900%, highlighting a lack of API visibility – In the second half of 2022 alone, approximately 45 billion search attempts were made for shadow APIs, marking a 900% increase from the 5 billion attempts made in the first half of 2022.
- Holiday season sees 550% increase in unique threats – There was a 550% increase in the number of unique TTPs employed by attackers, rising from approximately 2,000 in June to a staggering 11,000 towards the end of 2022.
- Attackers increasingly combine API and web application security tactics – From June 2022 to October 2022, attackers favoured traditional application security tactics; however, as the holidays approached, there was a 220% surge in API security tactics.
- Attack surface sprawl highlights the telecom API protection challenge – Most re-tool attempts in the telecom industry were entirely new TTPs, which shows that the threat tactics utilised are diverse, sophisticated, and persistent.
- New OWASP API threat category API8 – Lack of protection from automated threats, validated – The CQ Threat Research Team previously identified the need for API10+ to go beyond the OWASP API Top 10 to include protection against automated attacks. The threat report findings and the addition of API8: – Lack of protection from automated threats in the OWASP API Security Top 10 2023RC confirm the past observations made by Cequence and endorse the inclusion of native bot mitigation capabilities to a robust API security program.
The API threat landscape is constantly evolving, and organizations must be vigilant in protecting their APIs and web applications from automated threats (bots) and vulnerability exploits. Attackers are becoming more sophisticated and API-specific in their tactics, and traditional protection techniques continue to provide an ineffective defense.
“Our research is vital in providing organizations with the necessary tools and knowledge to mitigate attacks in real-time,” Talwalkar continued.
“By staying ahead of the curve and understanding the latest attack methods and tools, organizations can achieve Unified API Protection and build the awareness and confidence needed to protect their APIs from even the most sophisticated attacks,” Talwalkar concluded.