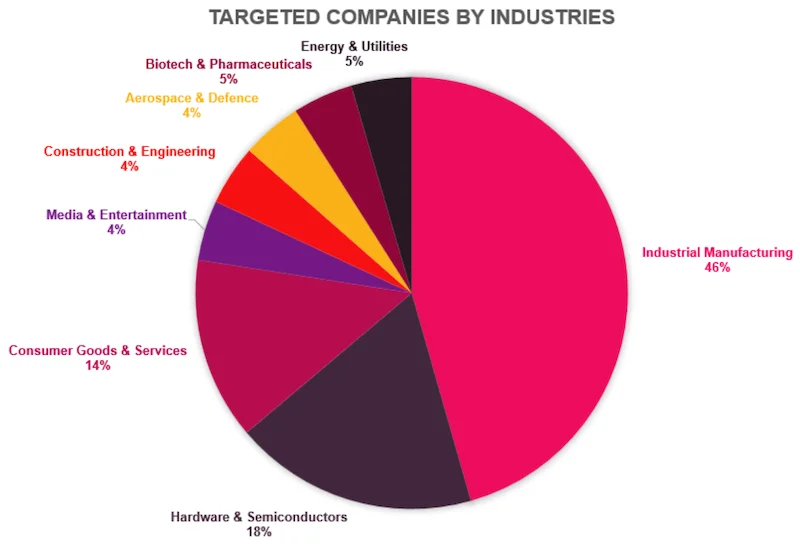
A recently uncovered phishing campaign – carefully designed to bypass security defenses and avoid detection by its intended victims – is targeting firms in industrial manufacturing and other companies critical to various supply chains, Check Point researchers have warned.
The phishing campaign(s)
The researchers believe that the campaign has been mounted by financially motivated threat actors.
Its goal is to deliver a malicious ZIP archive that contains a PowerShell script that will be executed in memory, and use it to ultimately deliver a custom in-memory implant/backdoor called “MixShell”. The malware uses DNS TXT tunneling with HTTP fallback for C2 communications and executes commands and file operations remotely.
The most interesting thing about this campaign in the effort invested in convincing employees at victim organizations to trust the email and download and run the malicious ZIP file.
The attackers reached out to them via the “Contact Us” form found on target companies’ website, thus effectively tricking victims into initiating email correspondence and automatically bypassing reputation-based email filters.
“Attackers invest days or weeks in credible, professional conversations, often requesting that the victim sign a Non-Disclosure Agreement (NDA),” the researchers shared. (The NDA document can serve as a lure and as a decoy document.)
“The domains used by the threat actors to initiate email communication appear to be carefully selected for credibility and legitimacy. Many of these domains match the names of LLCs registered in U.S-based companies and in some cases, may have previously belonged to legitimate businesses.”
These domains were originally registered more than five years ago. Their clear reputations and legitimate business histories helped the attackers fool both security filters and potential victims.
How the attackers trick the recipients (Source: Check Point Research)
Once the attackers felt that they’ve managed to gain the targets’ trust, they asked them to download the malicious file from a subdomain of the herokuapp.com.
The researchers have also spotted newer wave of phishing emails associated with this same campaign: Instead of reaching out via the “Contact Us” form, the attackers are emailing employees directly and claiming that they are working with the organization to help implement AI-driven operational changes.
“The email is positioned as an internal initiative and framed as an ‘AI Impact Assessment’, asking the recipient to review a short questionnaire about how artificial intelligence might affect their team’s workflows. To increase legitimacy and urgency, the attacker explicitly states that the company’s leadership requested the recipient’s personal input, implying that their opinion will influence upcoming decisions,” the researchers noted.
This campaign is still in the initial phase so the researchers weren’t able to confirm that the malicious payload (that will be) used is the same.
The victims
The attackers have targeted organizations across multiple sectors, but mainly in the US.
They mostly hit enterprise-level companies, but small and medium (SMB) companies have also been targeted.
“The long-term engagement with the victim (multi-week conversations) suggests that the attacker is willing to invest time cultivating the relationship regardless of company size, possibly tailoring their efforts based on perceived value or ease of compromise,” the researchers noted.
“More than 80% of the identified targets in this campaign are based in the United States, underscoring a clear geographic concentration, while also companies in Singapore, Japan and Switzerland were targeted. Overall, the engagement patterns observed were U.S-centric regarding infrastructure, communication style, and initial access points.”
![]()
Subscribe to our breaking news e-mail alert to never miss out on the latest breaches, vulnerabilities and cybersecurity threats. Subscribe here!
![]()