Threat Actors Exploiting Legitimate Software For Stealthy Cyber Attacks
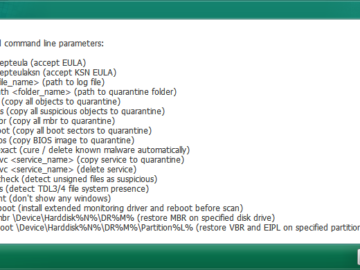
CAMO, or Commercial Applications, Malicious Operations, highlights attackers’ increasing reliance on legitimate IT tools to bypass security defenses, which can be used for various malicious…