74% of ransomware victims were attacked multiple times in a year
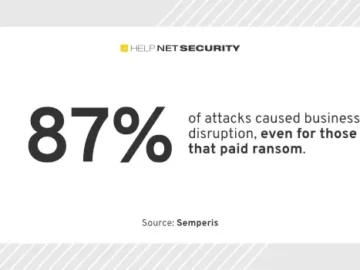
An alarming trend toward multiple, sometimes simultaneous cyber attacks forces business leaders to re-evaluate their cyber resilience strategies to address common points of failure, including…