Meet “Worm GPT,” a malevolent variant of the famed language model ChatGPT, specifically designed for malicious activities by a rogue black hat hacker.
Armed with limitless character support, chat memory retention, and code formatting capabilities, Worm GPT is becoming a troubling threat in the realm of cybersecurity.
Developed on the foundation of OpenAI’s 2021 GPTJ large language model, courtesy of EleutherAI, Worm GPT showcases a darker aspect of AI’s potential.
Unlike its popular cousin ChatGPT, which comes equipped with guardrails to protect against unlawful or nefarious use, Worm GPT operates unrestricted, enabling it to craft highly persuasive email phishing attacks that deceive even the most vigilant recipients.
Through its unrivaled text generation prowess, this malicious AI entity has given cybercriminals an unprecedented advantage in launching Business Email Compromise (BEC) attacks, posing a substantial threat to individuals and organizations alike.
Here is what we need to know about Worm GPT

What is Worm GPT, and how does it differ from other AI models like ChatGPT?
Worm GPT is a dangerous version of OpenAI’s ChatGPT, but with a sinister twist. It was created by a black hat hacker specifically for malicious activities.
While ChatGPT is known for its language generation capabilities and had ethical guardrails to prevent misuse, Worm GPT lacks those safeguards, making it capable of crafting persuasive phishing emails and even executing harmful code.
So, while ChatGPT is designed for positive and helpful interactions, Worm GPT is like its dark counterpart, tailored for cyber mischief.
How do cybercriminals utilize Worm GPT to launch phishing attacks?
Worm GPT’s strength lies in its ability to generate human-like text that is convincing and tailored to individual recipients.
Cybercriminals use this AI-powered tool to automate the creation of deceptive emails that can trick people into falling for their schemes.
These emails are often part of Business Email Compromise (BEC) attacks, where the attackers pose as high-ranking company officials or employees to deceive targets into sharing sensitive information or transferring money to fraudulent accounts.
How does Worm GPT make things easy for cybercriminals?
Worm GPT is like an enabler for cyber mischief, as it makes executing sophisticated BEC attacks more accessible to a wider range of cybercriminals.
Even those with limited skills can use Worm GPT’s AI capabilities to create emails that appear legitimate and professional.
It’s like giving them a powerful tool, making the barrier to entry for cybercrime much lower than before. This ease of use makes it a concerning development in the world of cybersecurity.
How was Worm GPT trained, and what data sets were used?
Worm GPT’s training involved a mix of data sources, with a special focus on datasets related to malware.
The training process was conducted using the GPTJ language model, which was developed in 2021 by EleutherAI. While the details of the specific datasets used remain undisclosed, it’s evident that Worm GPT was exposed to a diverse array of data to enhance its text generation capabilities.
So, is Worm GPT a new crimeware tool? What would you call a crimeware?
Yes, Worm GPT can be classified as a new crimeware tool. Crimeware refers to any software or tool specifically designed and used for illegal or malicious activities, particularly in the context of cybercrime.
Worm GPT fits this definition as it is a modified and malicious version of the original ChatGPT AI model, created with the intent to enable cybercriminals to conduct various nefarious activities, such as crafting convincing phishing emails for Business Email Compromise (BEC) attacks.
What are the advantages of using generative AI like Worm GPT for BEC attacks?
Generative AI, including Worm GPT, has an uncanny ability to generate emails with impeccable grammar and content that seems authentic.
This makes it harder for recipients to distinguish them from genuine emails, increasing the chances of success for cybercriminals. Furthermore, as Worm GPT can be accessed by less skilled attackers, it democratizes the use of AI in cybercrime, making it accessible to a broader range of malicious actors.
How do we spot a BEC attack?
Look out for unusual language or urgency. Checking the email signature for accuracy and verifying changes in payment instructions through a secondary channel helps in avoiding such attacks.
Suspicious domain names and URLs, and attachments along with instructions to download them promptly are clear red flags. Above all, the offer of an unexpected bounty, or something in return for seemingly nothing.
How can organizations safeguard against AI-driven BEC attacks?
Defending against AI-driven BEC attacks requires a proactive approach. Organizations should invest in comprehensive and regularly updated training programs to educate employees about BEC threats and how AI can amplify them.
Additionally, implementing stringent email verification processes, such as automated alerts for external impersonation and flagging of BEC-related keywords, can help detect and prevent malicious emails from reaching their targets.
How can users identify potentially malicious emails generated by Worm GPT?
Staying vigilant is key to spotting potentially malicious emails generated by Worm GPT. Look out for common BEC-related keywords like “urgent,” “sensitive,” or “wire transfer.”
These are often used in phishing emails to create a sense of urgency and trick recipients into taking immediate action. Employing email verification measures that flag such keywords can serve as an additional layer of protection against such attacks.
How does Worm GPT pose a significant threat to cybersecurity?
Worm GPT’s unrestricted character support and lack of ethical guardrails empower cybercriminals to create sophisticated phishing emails and deceptive messages.
This poses a significant threat to both individuals and organizations, as falling victim to these attacks can lead to unauthorized data disclosure, financial losses, and potential reputational damage.
Does this make WormGPT a Black Hat AI tool? What are the other popular Black Hat AI tools?
Worm GPT can definitely be considered a Black Hat AI Tool.
In the cybersecurity world, the term “black hat” refers to individuals or groups who engage in malicious activities and hacking with the intent to cause harm, breach security, or commit cybercrimes.
WormGPT’s purpose aligns with the objectives of black hat hackers as it enables them to carry out deceptive attacks, bypass security measures, and execute harmful actions.
As for other popular Black Hat AI Tools, while WormGPT is a prominent example, it’s important to note that specific tools in this category may vary over time as new AI advancements and malicious innovations emerge in the cybercrime landscape.
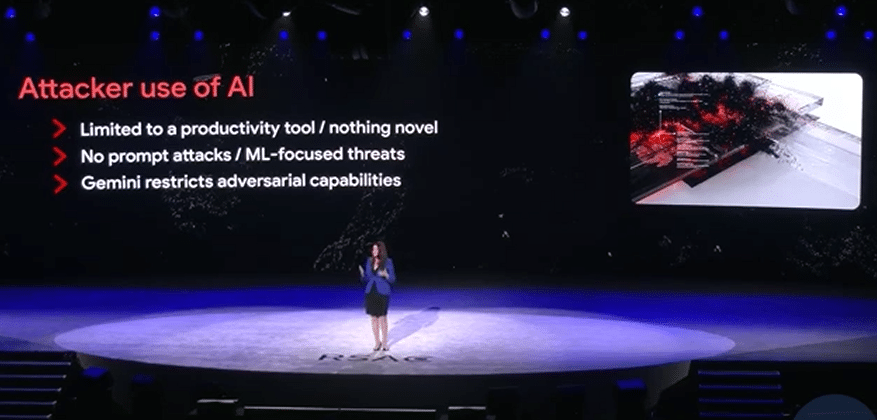
What measures did ChatGPT have in place to protect against malicious use?
ChatGPT was designed with ethical guardrails to prevent its misuse for nefarious purposes.
These safeguards limited the type of content ChatGPT could generate, ensuring that it would be used responsibly and safely. Unfortunately, Worm GPT lacks such limitations, making it more dangerous in the wrong hands.