Broken Access Control – Lab #5 URL-based access control can be circumvented | Short Version

Source link
Related Articles
All Mix →3 quick questions with Security Awards nominee Jonatan Haltorp
Security Awards is a yearly event arranged by the Swedish publication Skydd och Säkerhet, where the aim is to highlight persons or companies that are…
Hostfind: Another Lame Tool | Daniel Miessler
Only this one is more lamerer. This will take a list of words from a list you provide and append them to the front of…
Cloud Security Alliance Webinar Recap: Avoid the Breach with Shopify’s Andrew Dunbar
In this Cloud Security Alliance (CSA) fireside chat, Shopify’s VP of Security Engineering and IT sat down with HackerOne’s Luke Tucker to talk about how…
Don’t Force Yourself to Become a Bug Bounty Hunter
Ever since I was a kid I was never good at doing schoolwork. I had envied everyone that seemed to complete things so effortlessly and…
Inside the head of a white hat hacker
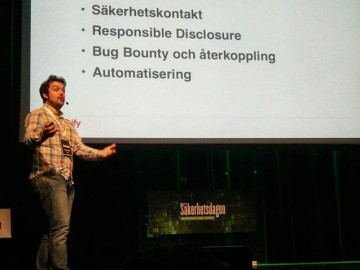
Yesterday, Detectify’s Knowledge Advisor Frans Rosén gave an inspiring talk about white hat hacking and web security at Computer Sweden’s event Säkerhetsdagen 2016 in Stockholm.…
ASUS Vulnerability Disclosure Déjà vu
Two years after a settlement with the FTC, has ASUS still not learned how to receive vulnerability reports from hackers? Last February, the Taiwanese hardware…