
Bug Bounty Guide: How to Exploit Microsoft/nni with Deserialization Attacks | Open-Source Python

Source link
Related Articles
All Mix →My Current Definition of AGI
Table of Contents My definition of AGI Don’t smuggle in humanness The escape hatch People throw the term “AGI” around like it’s nothing, but they…
Sony hit again?, Taiwan Disinformation, Corporations Demand Hardcore Workers, and GPTVision Examples…
Unsupervised Learning is a Security, AI, and Meaning-focused podcast that looks at how best to thrive as humans in a post-AI world. It combines original…
Extreme Transparency or Corporate Security Responsibility?
Extreme Transparency or Corporate Security Responsibility? Source link
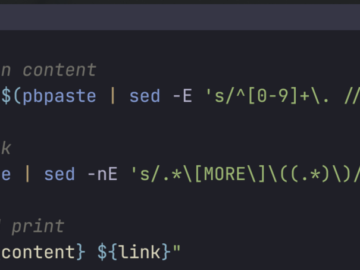
Streamlining Tweet Creation from Markdown
Table of Contents The Bash Script: tweet_from_markdown Integrating with Espanso How It Works in Practice Conclusion As an experience engineer, I’m always looking for ways…
[tl;dr sec] #295 – AI Code Analysis, AWS Detection Engineering, Anthropic Threat Intel Report
Table of Contents Gonna be Golden AppSec Cloud Security Blue Team Red Team AI + Security Misc Wrapping Up I hope you’ve been doing well!…
Marten Mickos wants to let a million hackers loose on corporate America
This first appeared in the San Francisco Business Times on November 3, 2016. View the original article here: http://www.bizjournals.com/sanfrancisco/news/2016/11/03/marten-mickos-hackerone-hackers-bugs-bounties.html Marten Mickos in SFBT Marten Mickos…

![[tl;dr sec] #295 - AI Code Analysis, AWS Detection Engineering, Anthropic Threat Intel Report](https://image.cybernoz.com/wp-content/uploads/2025/09/tldr-sec-295-AI-Code-Analysis-AWS-Detection-Engineering.png)
