Hackers take advantage of Word documents as weapons due to their widespread use and trust.
This is facilitated by the ease with which users can be deceived into opening them.
These documents may have macros or exploits that are dangerous when activated to run malicious code on a victim’s machine. This allows an attacker to steal data, install malware, or even gain control over the system remotely.
Cybersecurity researchers at Cisco Talos recently discovered that malware, which is dubbed “CarnavalHeist,” has been actively weaponizing the Word documents to steal login credentials.
CarnavalHeist Weaponizing Word Documents
It is of high certainty that the CarnavalHeist focuses on the Brazilians.
This is based on the use of only Portuguese language and Brazilian slang, as well as command and control infrastructure located in Microsoft Azure hosting facility BrazilSouth region, which majorly concentrates on leading financial institutions in Brazil.
However, starting from February 2024, there are visible activities of this malware being ongoing.
Looking for Full Data Breach Protection? Try Cynet’s All-in-One Cybersecurity Platform for MSPs: Try Free Demo
Although samples have been seen on VirusTotal since late 2023, they are showing continuing development.
Still actively active as of May 2024, due to which Talos keeps identifying fresh Brazilian malware samples of CarnavalHeist.
Malicious invoice-themed emails are being used to start CarnavalHeist, and these lure users into clicking on shortened URLs, which then redirect them to fake invoice websites.
This website then downloads a malicious LNK file through WebDAV, which runs the next stage payload.
The attack extensively uses Portuguese terms such as “Nota Fiscal Eletrônica” (electronic invoice) across the domains, files, and contents, enhancing social engineering lures for Brazilian users.
.webp)
Common threat actor techniques for executing malicious commands are exemplified in the metadata of this LNK file.
The malware employs deceptive techniques, such as showing a false PDF document to mislead users while running malicious code at the back.
It uses obscured Python scripts, dynamically generated domains, and DLLs injected into loading a banking Trojan payload.
This Trojan targets Brazilian financial institutions using overlay attacks. It captures credentials, screenshots, and video and enables remote access.
One of its capacities includes generating QR codes for stealing transactions.
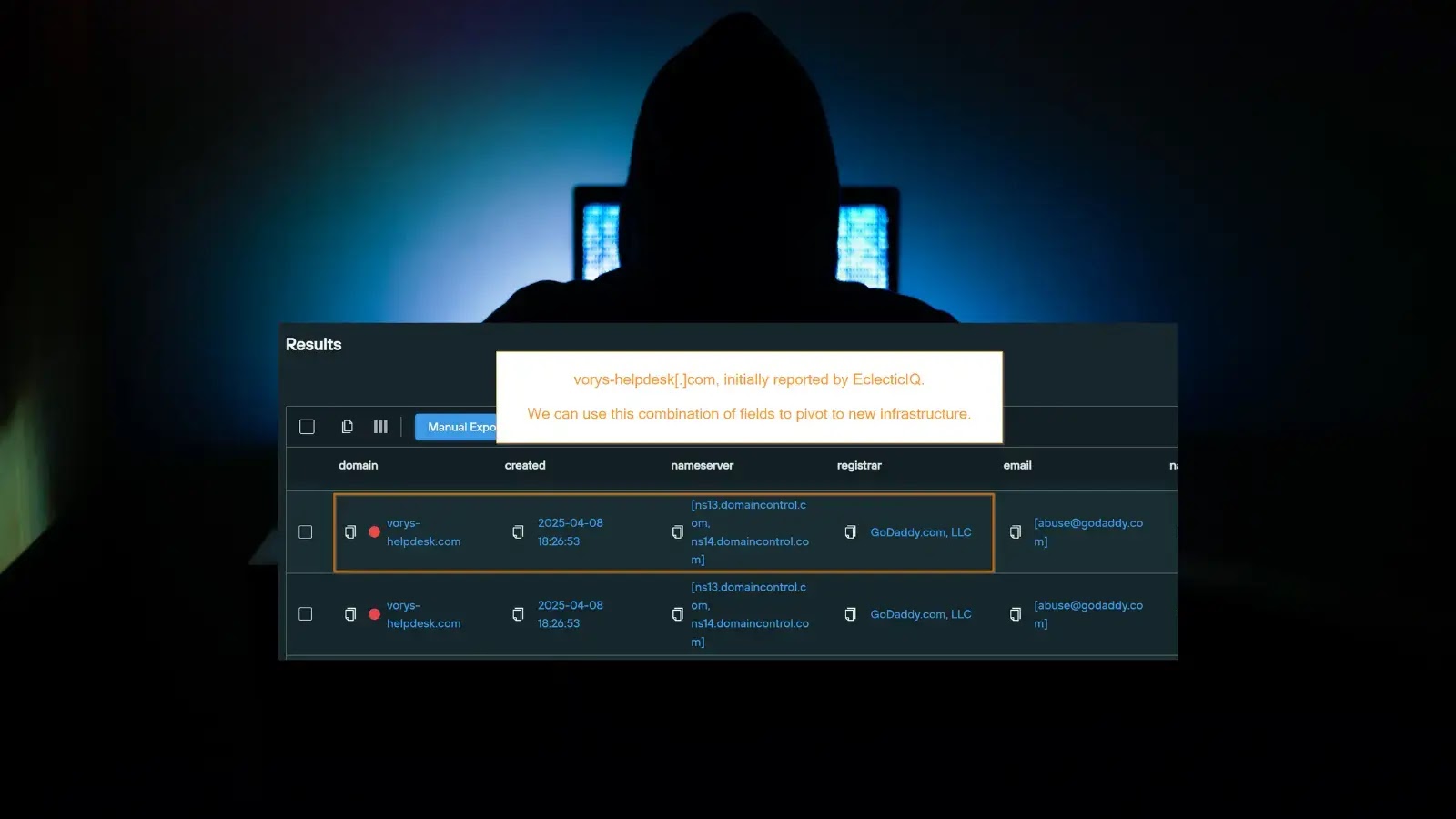
Exposed project metadata and domain registration details pointing to individuals in Brazil who have made some aspects of these campaigns.
Cisco said that CarnavalHeist is a domain generation algorithm (DGA) that dynamically creates subdomains under the Azure BrazilSouth region for downloading payloads and C2 communications.
The Python script uses dates and an embedded string to create probable sub-domains while the final payload exploits seed values associated with targeted banks in conjunction with date and time parameters that form the C2 domains.
.webp)
Evidence indicates that the campaign may have been active since November 2023, but intensive activities began in February 2024, as shown by analysis of telemetry sources of generated DGA domains.
Get special offers from ANY.RUN Sandbox. Until May 31, get 6 months of free service or extra licenses. Sign up for free.