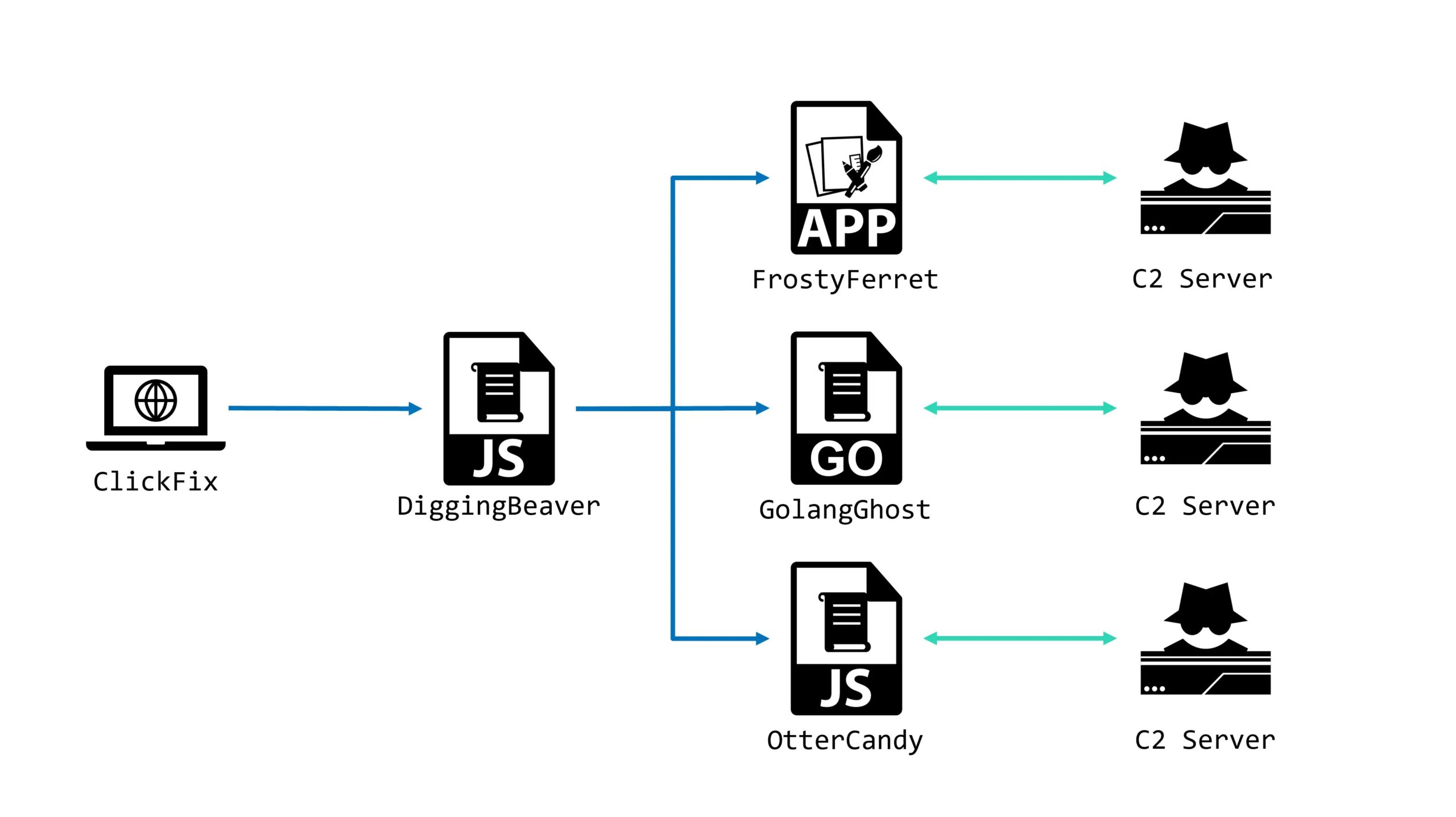
Threat Actors Leveraging ClickFake Interview Attack to Deploy OtterCandy Malware
Cybercriminals associated with the North Korean threat group WaterPlum, also known as Famous Chollima or PurpleBravo, have escalated their activities with a sophisticated new malware…