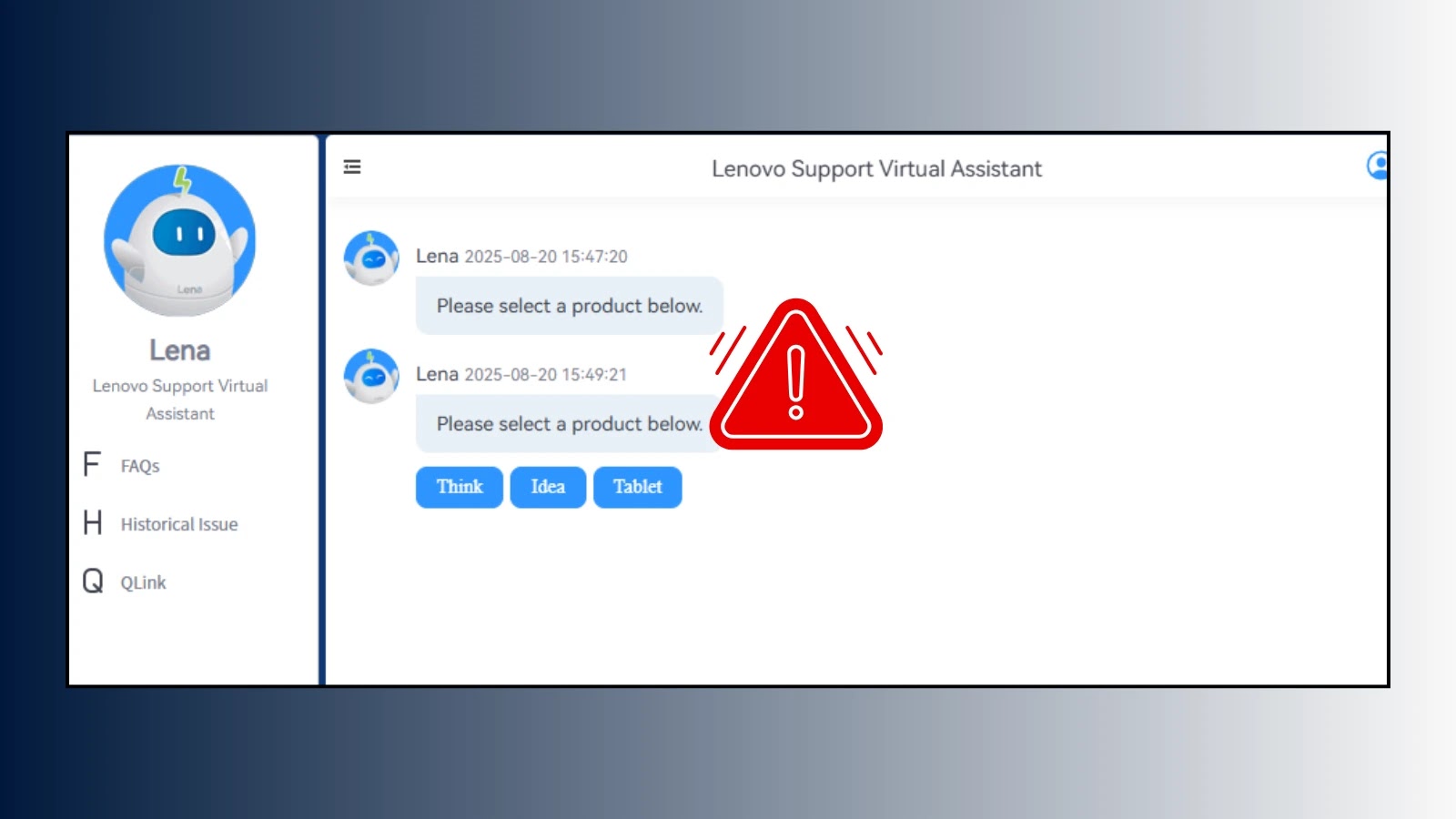
Lenovo AI Chatbot Vulnerability Let Attackers Run Remote Scripts on Corporate Machines
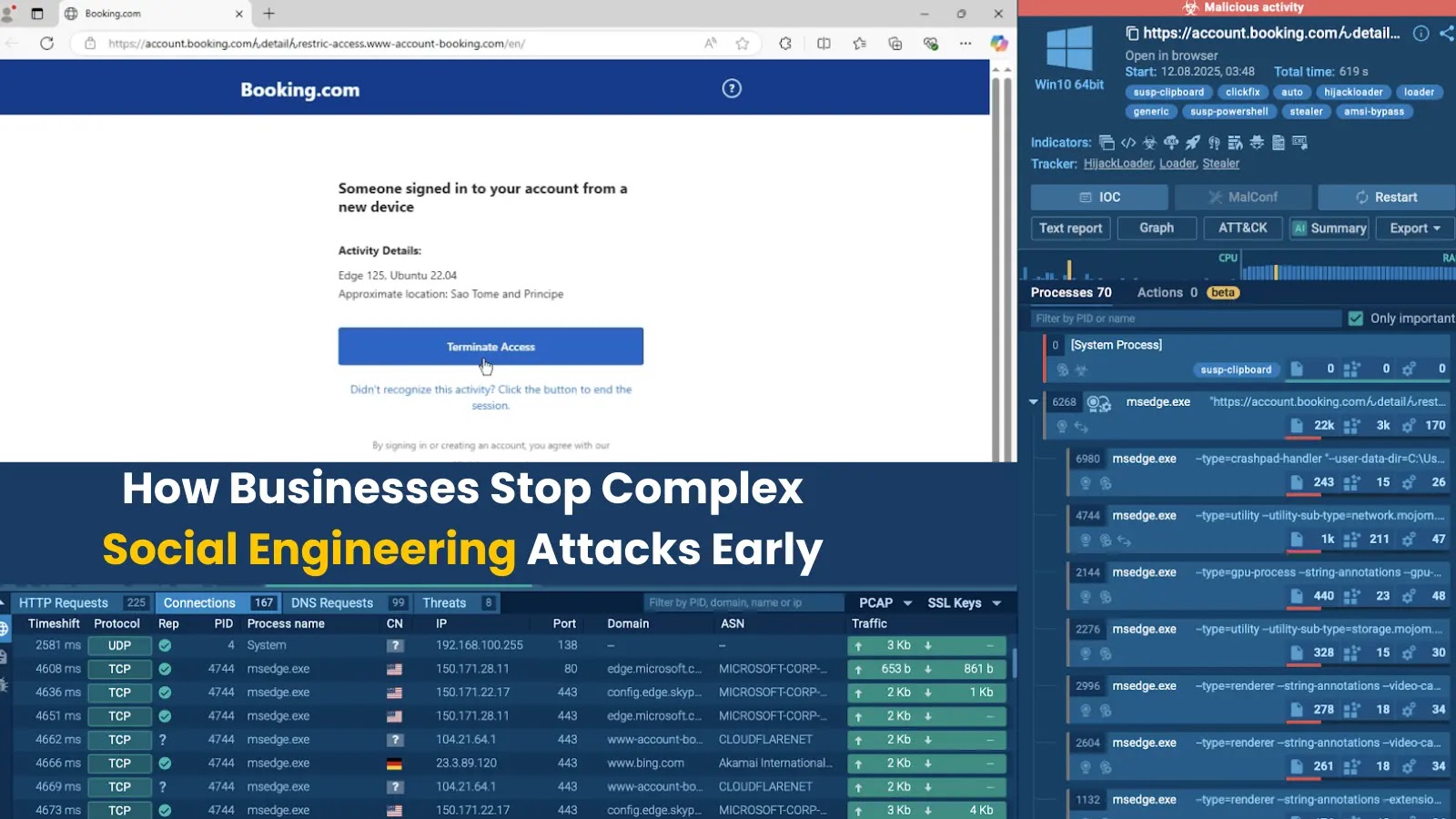
A critical security flaw in Lenovo’s AI chatbot “Lena” has been discovered that allows attackers to execute malicious scripts on corporate machines through simple prompt…