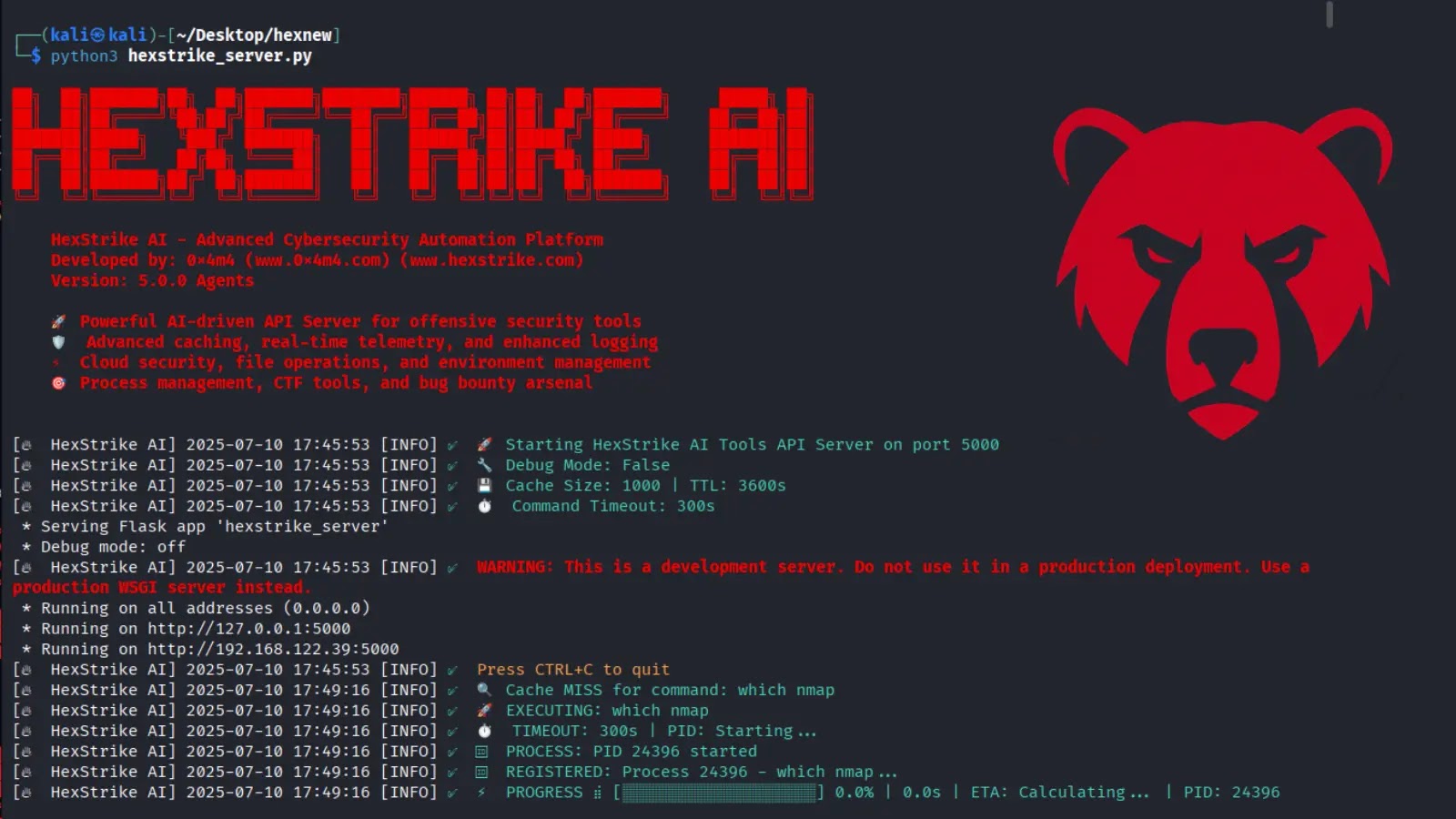
HexStrike AI Connects ChatGPT, Claude, Copilot with 150+ Security Tools like Burp Suite and Nmap
A new AI tool named HexStrike AI has been launched, designed to bridge the gap between large language models (LLMs) and practical cybersecurity operations. The…