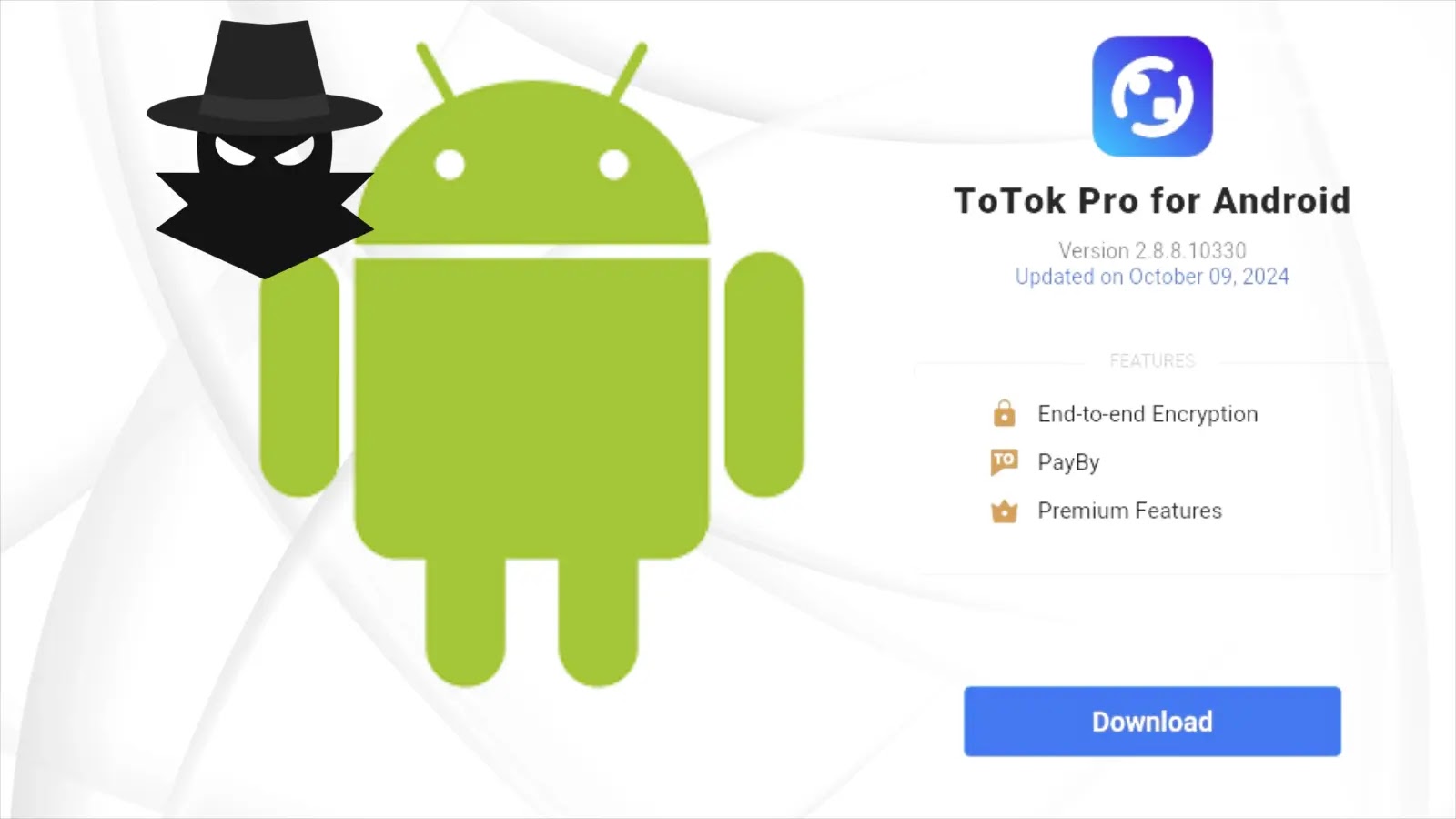
New Android Spyware Targeting Users by Imitating Signal and ToTok Apps
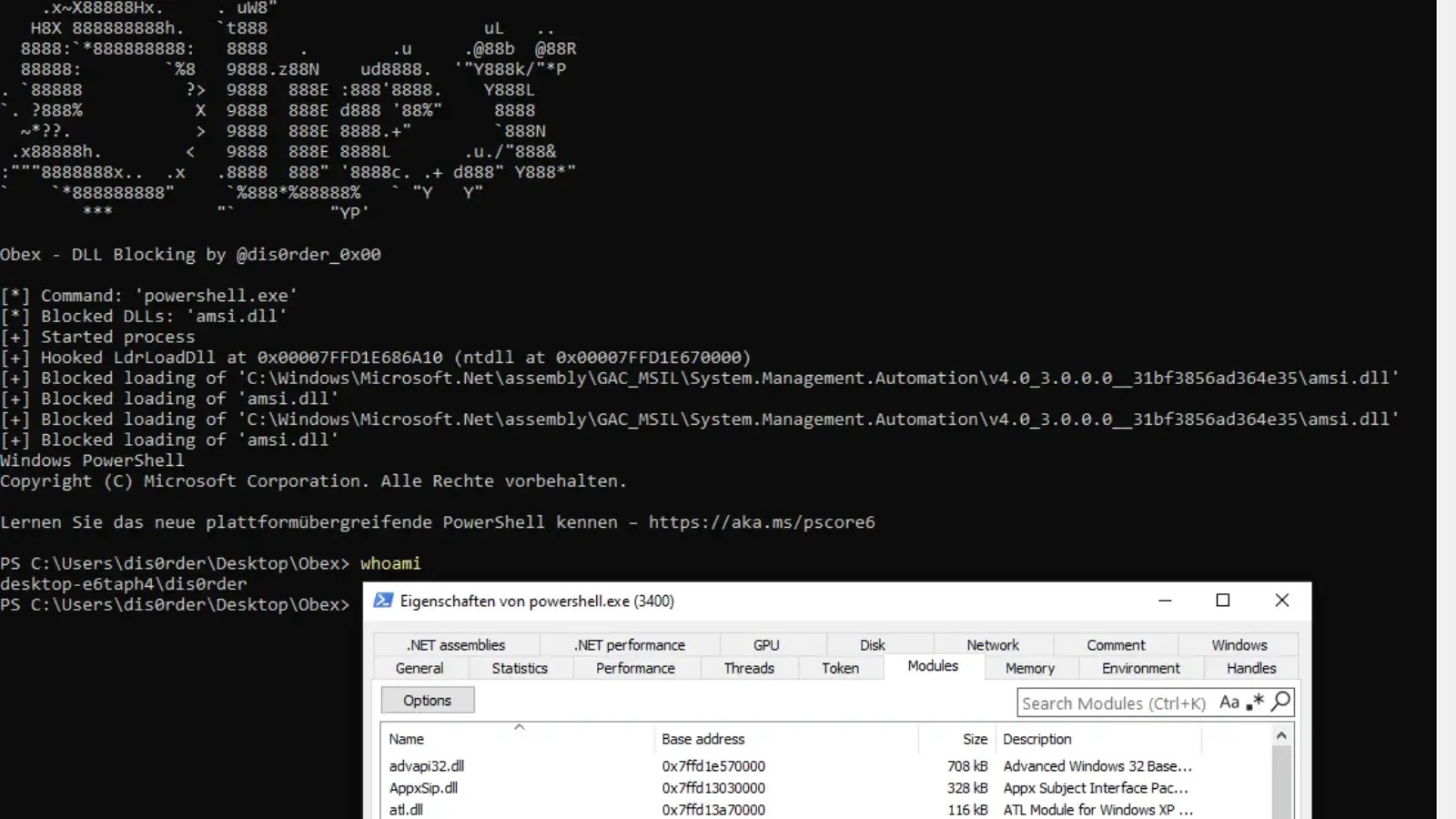
ESET researchers have uncovered two sophisticated Android spyware campaigns that target users seeking secure communication platforms by impersonating popular messaging apps Signal and ToTok. These…