Hackers Use Pahalgam Attack-Themed Decoys to Target Indian Government Officials
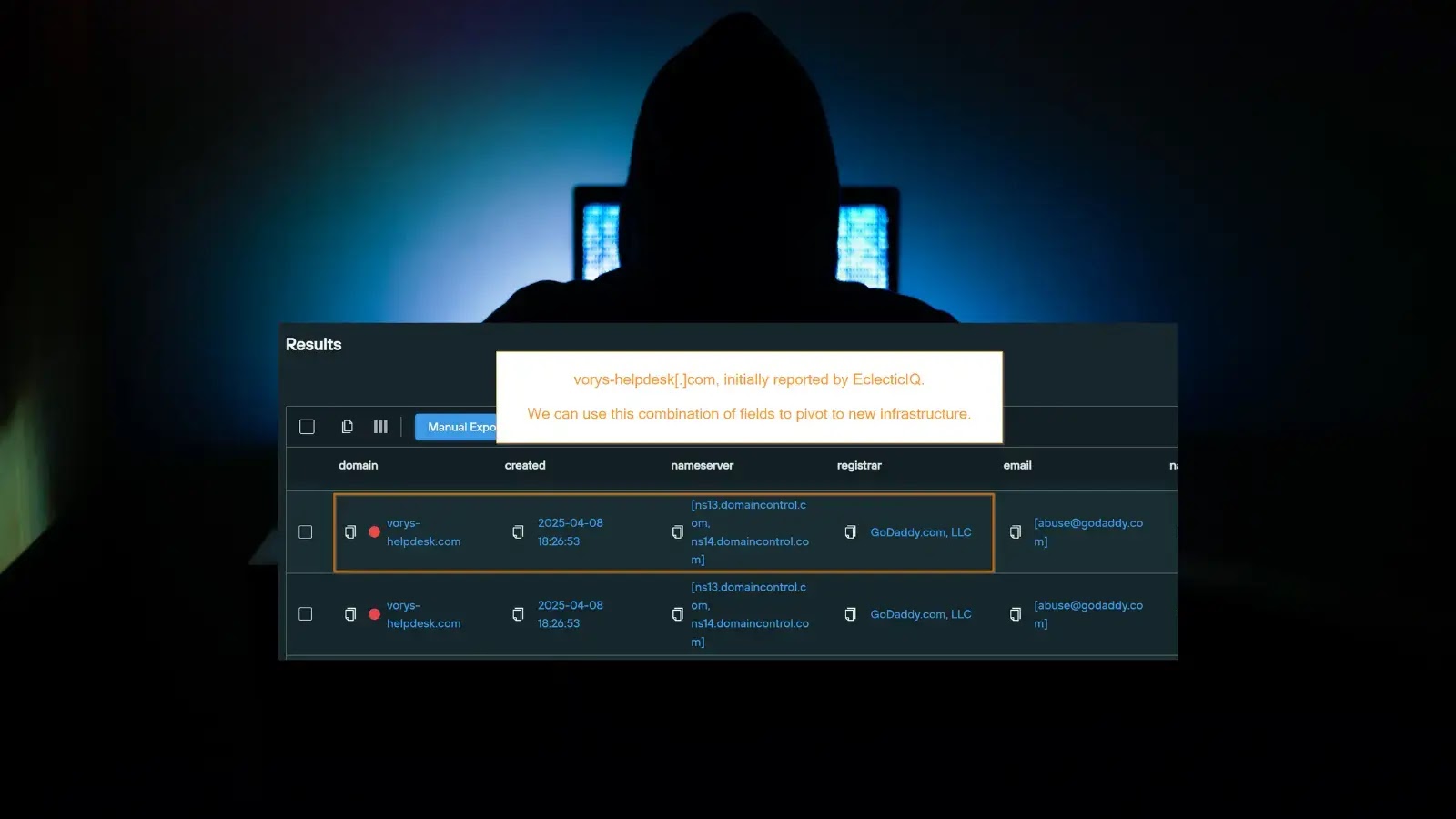
The Seqrite Labs APT team has uncovered a sophisticated cyber campaign by the Pakistan-linked Transparent Tribe (APT36) targeting Indian Government and Defense personnel. This operation,…