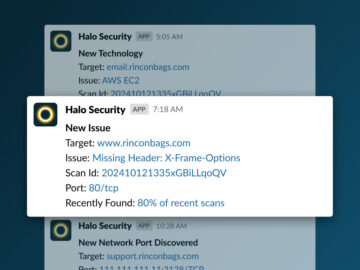
Halo Security Launches Slack Integration for Real-Time Alerts on New Assets and Vulnerabilities
MIAMI, Florida, November 21st, 2024, CyberNewsWire Halo Security, a leader in external attack surface management and penetration testing, has announced the launch of its new…