Hottest cybersecurity open-source tools of the month: April 2025
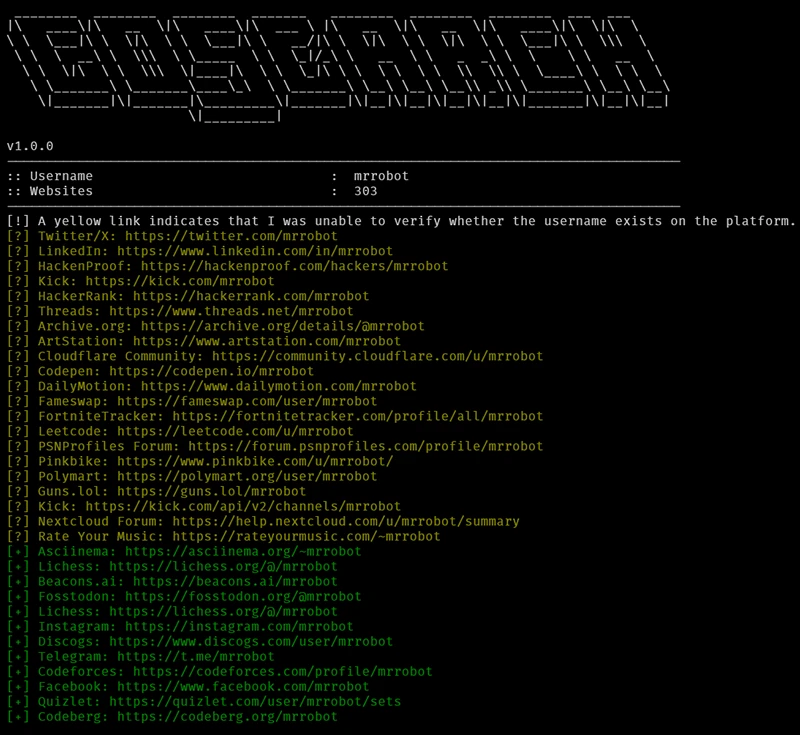
This month’s roundup features exceptional open-source cybersecurity tools that are gaining attention for strengthening security across various environments. GoSearch: Open-source OSINT tool for uncovering digital…