Cisco Secure Application provides business risk insights for cloud native apps
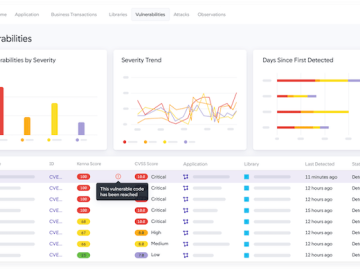
Cisco has unveiled Cisco Secure Application (previously Security Insights for Cloud Native Application Observability) on the Cisco Full-Stack Observability Platform, enabling organizations to bring together…