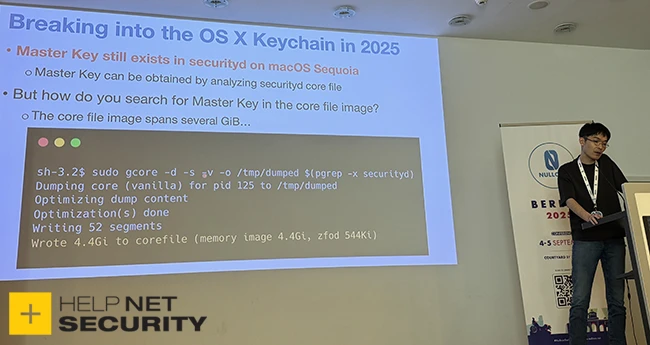
macOS vulnerability allowed Keychain and iOS app decryption without a password
Today at Nullcon Berlin, a researcher disclosed a macOS vulnerability (CVE-2025-24204) that allowed attackers to read the memory of any process, even with System Integrity…