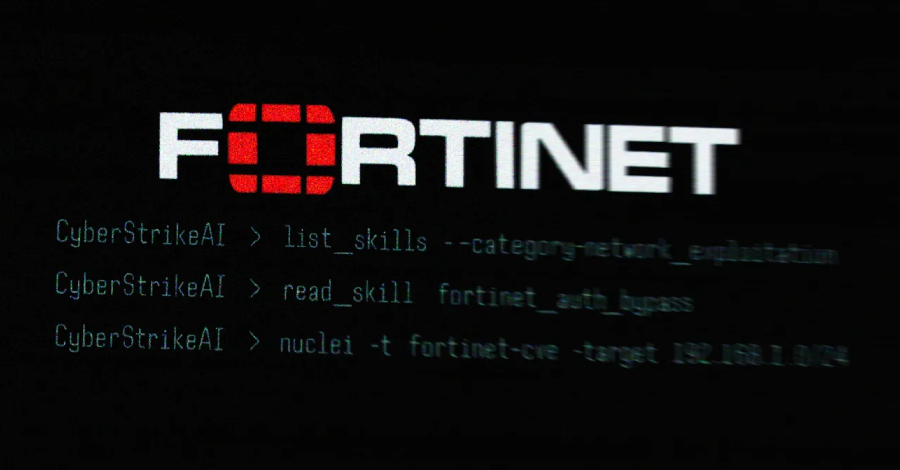
Open-Source CyberStrikeAI Deployed in AI-Driven FortiGate Attacks Across 55 Countries
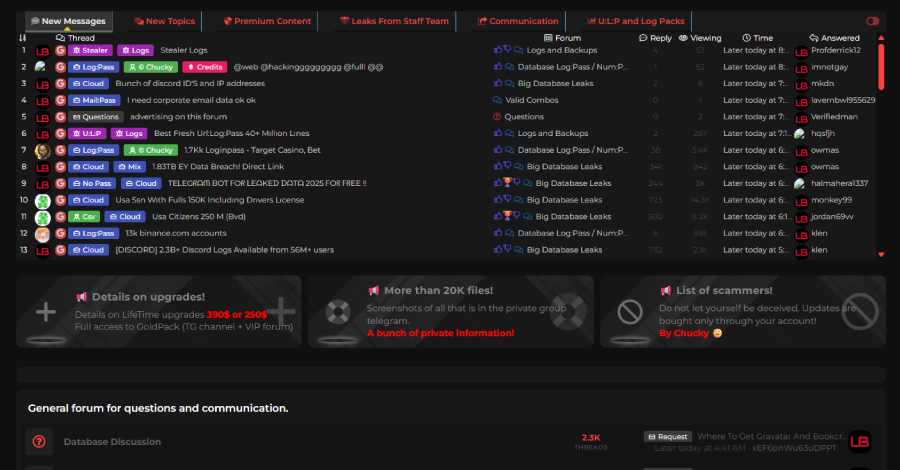
Ravie LakshmananMar 03, 2026Vulnerability / Artificial Intelligence The threat actor behind the recently disclosed artificial intelligence (AI)-assisted campaign targeting Fortinet FortiGate appliances leveraged an open-source,…