LightSpy Expands to 100+ Commands, Increasing Control Over Windows, macOS, Linux, and Mobile
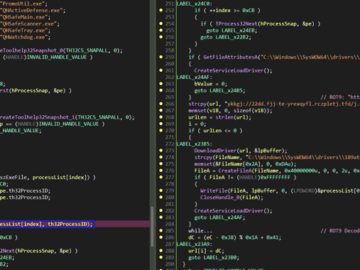
Cybersecurity researchers have flagged an updated version of the LightSpy implant that comes equipped with an expanded set of data collection features to extract information…