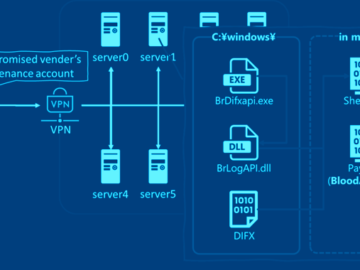
Pakistan-linked Hackers Deploy Python, Golang, and Rust Malware on Indian Targets
The Pakistan-nexus Transparent Tribe actor has been linked to a new set of attacks targeting Indian government, defense, and aerospace sectors using cross-platform malware written…