Bearlyfy Hits Russian Firms with Custom GenieLocker Ransomware
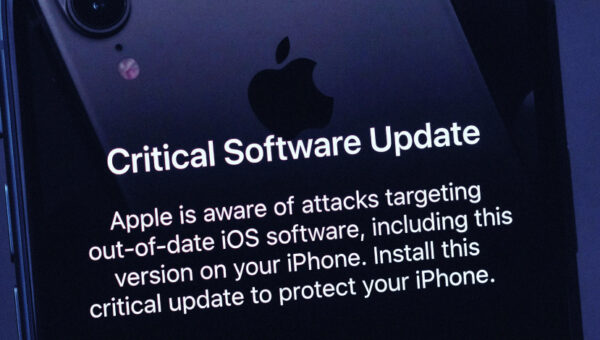
Ravie LakshmananMar 27, 2026Threat Intelligence / Vulnerability A pro-Ukrainian group called Bearlyfy has been attributed to more than 70 cyber attacks targeting Russian companies since…