CISA adds recently discovered Apple zero-days to Known Exploited Vulnerabilities Catalog

U.S. CISA adds vulnerabilities in Apple devices exploited to install NSO Group’s Pegasus spyware on iPhones to Known Exploited Vulnerabilities Catalog
US Cybersecurity and Infrastructure Security Agency (CISA) added the security vulnerabilities chained in the zero-click iMessage exploit BLASTPASS to its Known Exploited Vulnerabilities Catalog.
The two flaws, tracked as CVE-2023-41064 and CVE-2023-41061, were used to install NSO Group’s Pegasus spyware on iPhones.
The two Apple zero-day vulnerabilities, tracked as CVE-2023-41064 and CVE-2023-41061, reside in the Image I/O and Wallet frameworks.
CVE-2023-41064 is a buffer overflow issue that was reported by researchers from researchers at Citizen Lab. The IT giant addressed the flaw with improved memory handling.
“Processing a maliciously crafted image may lead to arbitrary code execution. Apple is aware of a report that this issue may have been actively exploited.” reads the advisory.
CVE-2023-41061 is a validation issue that was discovered by Apple. The IT giant addressed the flaw with improved logic. An attacker can achieve arbitrary code execution by tricking the device into processing a specially crafted attachment.
“A maliciously crafted attachment may result in arbitrary code execution. Apple is aware of a report that this issue may have been actively exploited.” reads the advisory.
Apple addressed the flaws with the release of macOS Ventura 13.5.2, iOS 16.6.1, iPadOS 16.6.1, and watchOS 9.6.2.
Recently, researchers at Citizen Lab reported that the actively exploited zero-day flaws are being used to infect devices with the Pegasus spyware. According to the researchers, the two vulnerabilities were chained as part of the BLASTPASS exploit used in attacks on iPhones running the latest version of iOS (16.6).
Citizen Lab reported that the exploit was used to install the Pegasus Spyware on the device belonging to an individual employed by a Washington DC-based civil society organization with international offices.
The experts reported that the exploit involved PassKit attachments containing malicious images that were sent to the victim from an attacker’s iMessage account.
“Last week, while checking the device of an individual employed by a Washington DC-based civil society organization with international offices, Citizen Lab found an actively exploited zero-click vulnerability being used to deliver NSO Group’s Pegasus mercenary spyware.” reads the report published by Citizen Lab” “We refer to the exploit chain as BLASTPASS. The exploit chain was capable of compromising iPhones running the latest version of iOS (16.6) without any interaction from the victim.
The exploit involved PassKit attachments containing malicious images sent from an attacker iMessage account to the victim.”
The researchers plan to publish technical details about the BLASTPASS exploit chain in the future.
Citizen Lab recommends iPhone users immediately update their devices. The organization pointed out that civil society is continuously targeted by threat actors using highly sophisticated exploits and spyware.
According to Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities, FCEB agencies have to address the identified vulnerabilities by the due date to protect their networks against attacks exploiting the flaws in the catalog.
Experts recommend also private organizations review the Catalog and address the vulnerabilities in their infrastructure.
CISA orders federal agencies to fix this flaw by October 2nd, 2023.
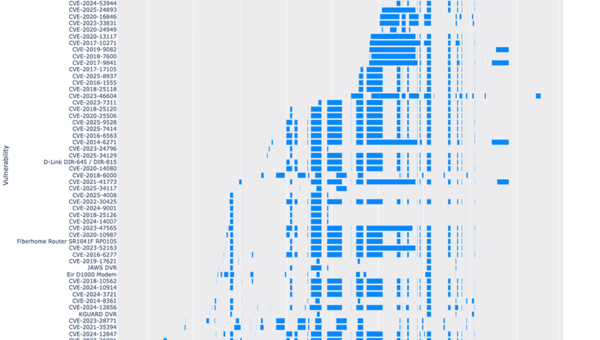
Apple has already patched 13 actively exploited zero-day vulnerabilities in 2023, below is the list of the flaws fixed by the company:
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, Known Exploited Vulnerabilities Catalog)