The Cybersecurity and Infrastructure Security Agency (CISA) recently detailed findings from a Red Team Assessment (RTA) conducted on a critical infrastructure organization in the United States.
The assessment, carried out over three months, simulated real-world cyberattacks to evaluate the organization’s cybersecurity defenses, detection capabilities, and response readiness.
This comprehensive analysis sheds light on the tactics, techniques, and procedures (TTPs) employed, as well as the lessons learned to enhance cybersecurity resilience.

Purpose and Scope of the Red Team Assessment
CISA’s red team assessments aim to simulate sophisticated adversarial tactics to identify vulnerabilities and test organizational defenses.
The target organization, a critical infrastructure entity, requested this RTA to better understand its cybersecurity risks.
Leveraging 2024 MITRE ATT&CK Results for SME & MSP Cybersecurity Leaders – Attend Free Webinar
During the assessment, the red team operated without prior knowledge of the organization’s technology landscape. The evaluation was divided into two phases:
- Phase I (Adversary Simulation): The red team attempted to infiltrate the organization’s network, maintain persistence, avoid detection, and access sensitive business systems (SBSs).
- Phase II (Defender Response Testing): The red team triggered measurable events to evaluate the organization’s response to suspicious activities.
The findings were mapped to the MITRE ATT&CK® framework and included recommendations for network defenders and software manufacturers to mitigate vulnerabilities.
Key Findings: Tactics, Techniques, and Procedures (TTPs)
The red team began with open-source reconnaissance to gather details about the organization’s network assets, employees, and defensive tools.
Initial spear phishing attempts failed due to the organization’s robust email defenses. However, further reconnaissance revealed a preexisting web shell on an unpatched internet-facing Linux server.
This vulnerability—leftover from a previous Vulnerability Disclosure Program (VDP)—allowed the red team to gain initial access.
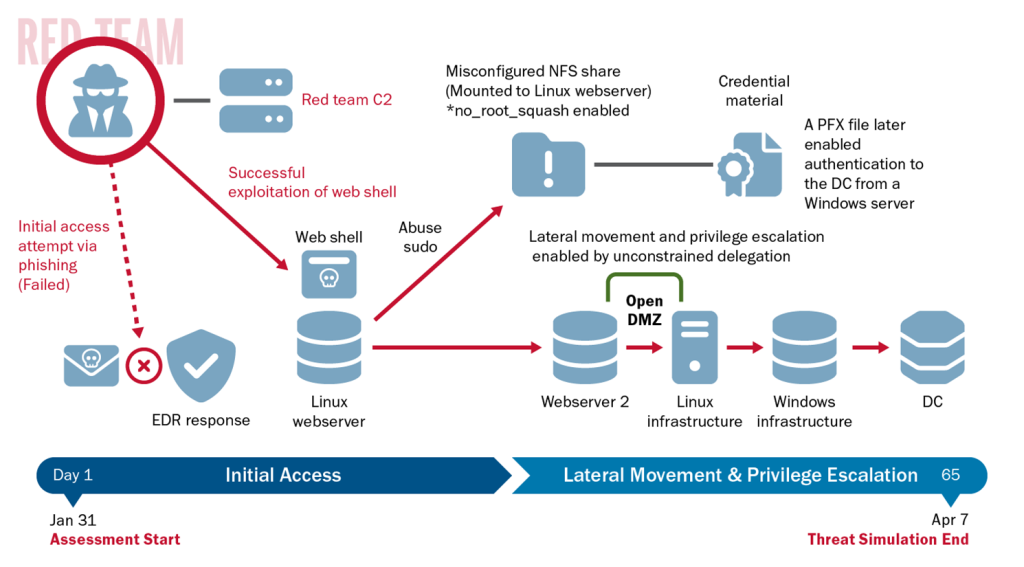
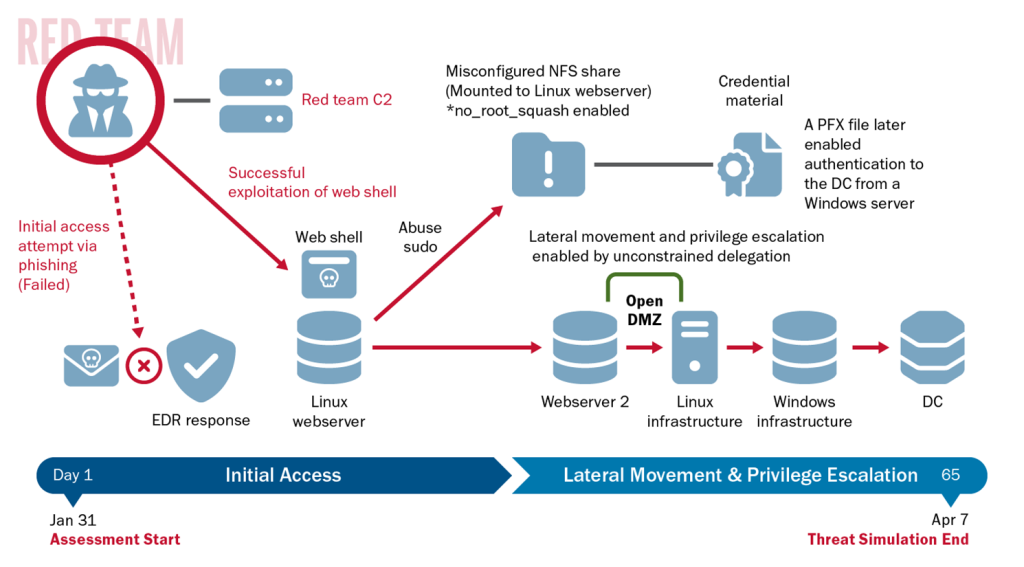
After gaining access, the red team exploited misconfigurations in a Network File System (NFS) share to escalate privileges and obtain credential material.
They moved laterally from the organization’s demilitarized zone (DMZ) to its internal network, leveraging SSH private keys, unconstrained delegation on domain controllers, and Kerberos ticket-granting tickets (TGTs). The red team employed advanced techniques such as:
- Exploiting sudo misconfigurations to escalate privileges.
- Using the Rubeus tool to capture Kerberos tickets.
- Forging “golden tickets” to impersonate domain accounts.
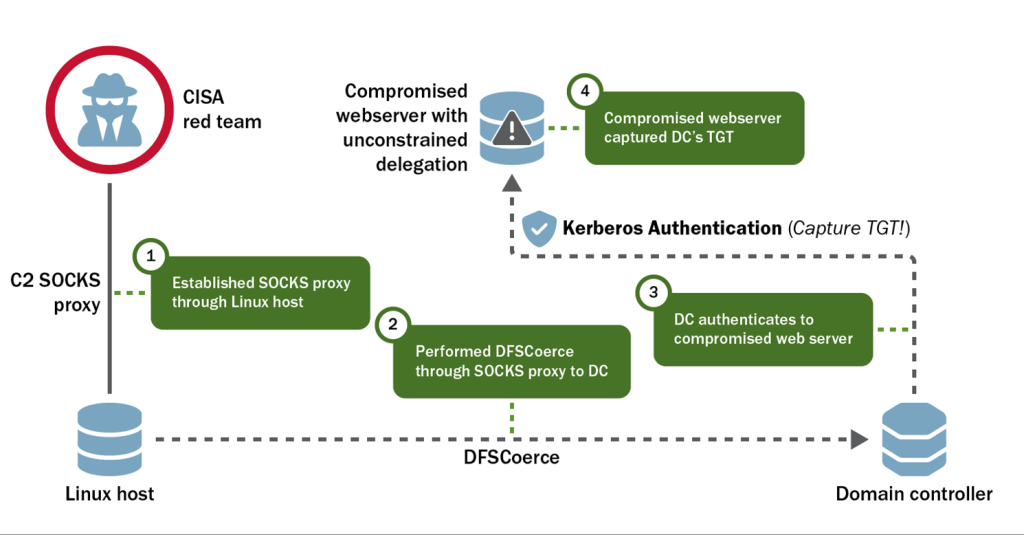
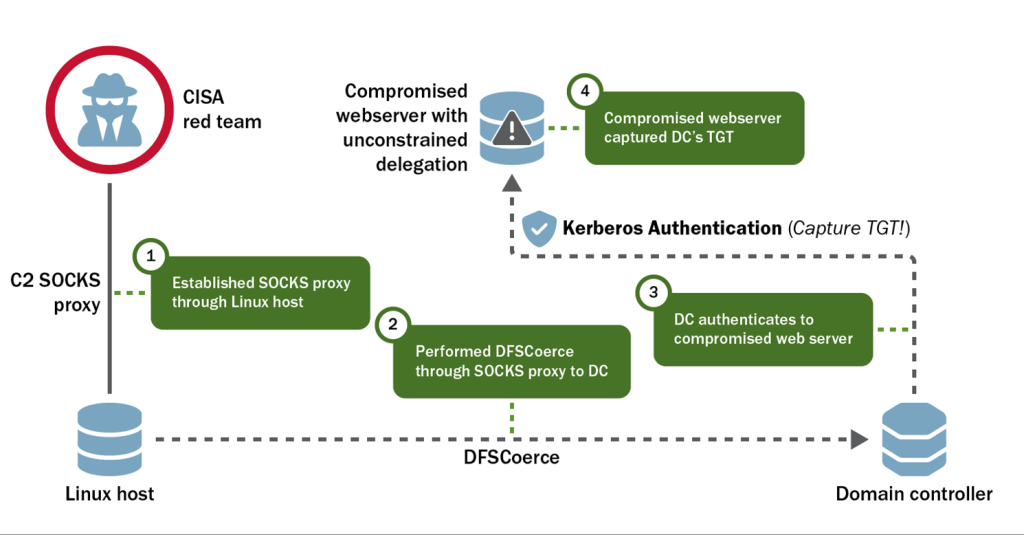
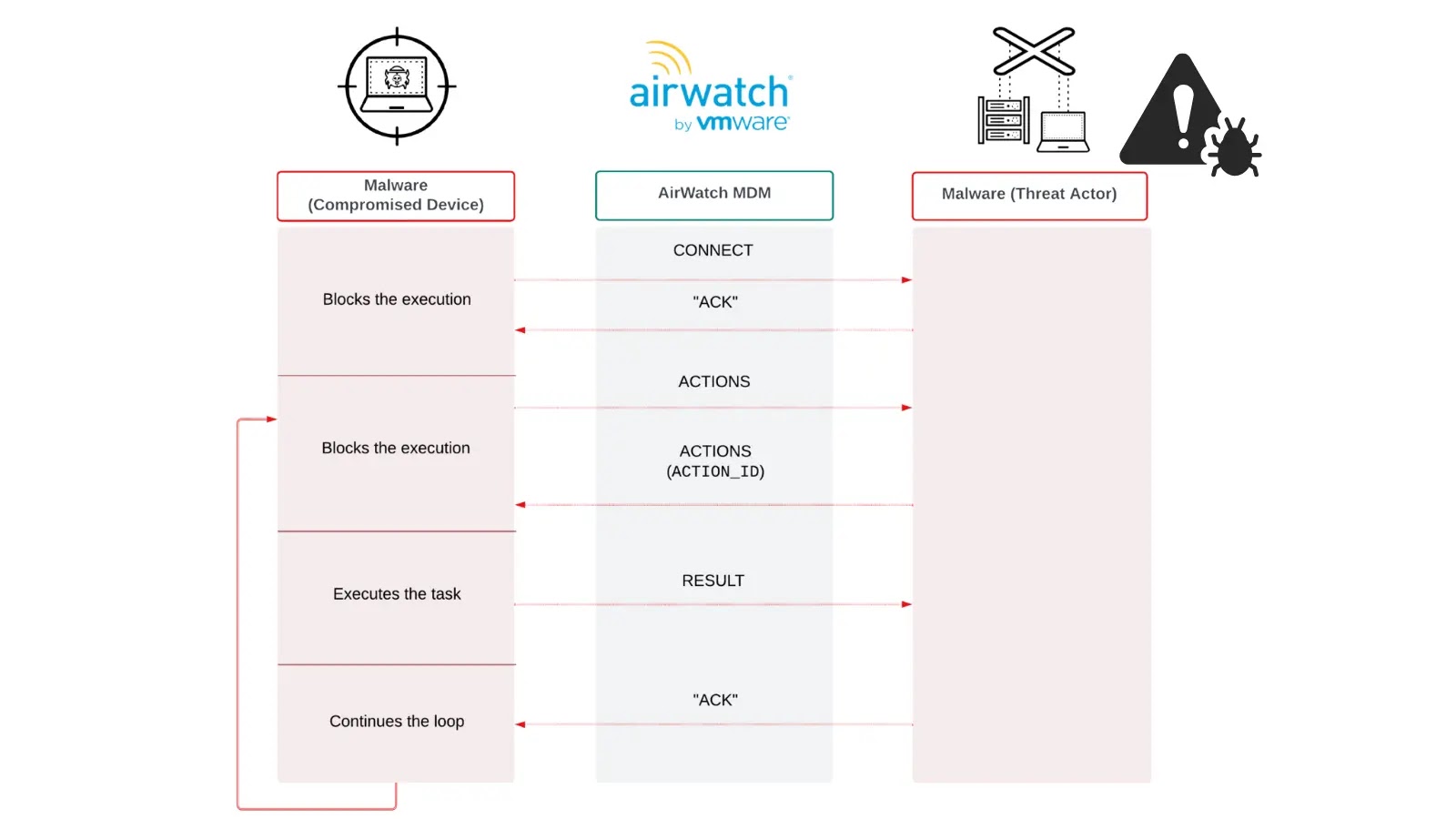
For command and control (C2), the team used HTTPS communications, obfuscation techniques like domain fronting, and third-party infrastructure such as cloud-based redirectors.
These methods made it difficult for defenders to attribute malicious activity to the red team.
Defender Challenges and Network Vulnerabilities
The organization’s Endpoint Detection and Response (EDR) tools failed to detect many red team activities. While some alerts were generated, they were not acted upon by network defenders. Key issues included:
- A lack of monitoring for Active Directory (AD) and Kerberos anomalies, such as S4U2Self and DCSync activity.
- Insufficient segmentation between Linux and Windows domains, enabling lateral movement.
- No intrusion detection systems (IDS) in the DMZ, leaving malicious traffic undetected.
The organization’s decision to enable no_root_squash on legacy NFS shares exposed sensitive credentials, while outdated Windows Server 2012 R2 systems provided an entry point for further exploitation.
Although the organization eventually detected the web shell and terminated much of the red team’s access, these actions were delayed. Critical vulnerabilities were not remediated promptly, allowing the red team to maintain persistence.
CISA recommended implementing tighter controls in software products to reduce the likelihood of domain compromises. This includes secure default configurations, built-in monitoring for privileged actions, and enhanced logging capabilities.
Red Team Successes and Defender Wins
Despite the challenges, the organization demonstrated partial success in mitigating threats:
- They detected and remediated the web shell used for initial access.
- Network defenders identified persistent implants in Linux hosts through threat hunting and NetFlow analysis.
- Some defensive tools successfully blocked initial phishing payloads.
However, the red team’s ability to bypass EDR solutions and move laterally across networks highlighted the need for better visibility and response capabilities.
The CISA red team assessment provided a critical learning opportunity for the targeted organization, exposing weaknesses in detection, response, and configuration management.
By documenting their TTPs and the organization’s defensive actions, CISA has equipped network defenders with actionable insights to strengthen cybersecurity postures across industries.
Analyze cyber threats with ANYRUN's powerful sandbox. Black Friday Deals : Get up to 3 Free Licenses.